CrowdStrike Technical Risk Assessments Reveal Common Exposure Patterns
In our Technical Risk Assessments, we consistently find that this external footprint is larger and more…
In our Technical Risk Assessments, we consistently find that this external footprint is larger and more…
“I’ve been saying since November, we’re looking at three to nine months until a massive influx…
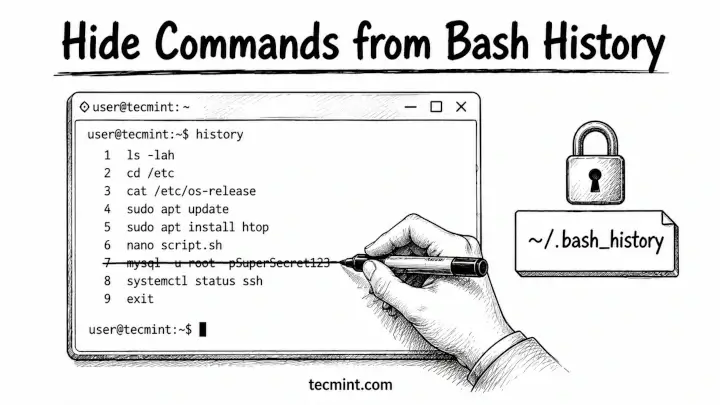
Every Linux user eventually runs a command they’d rather not preserve – a curl with a…
This blog details how these adversaries operate and how CrowdStrike Falcon® Shield identifies and disrupts their…
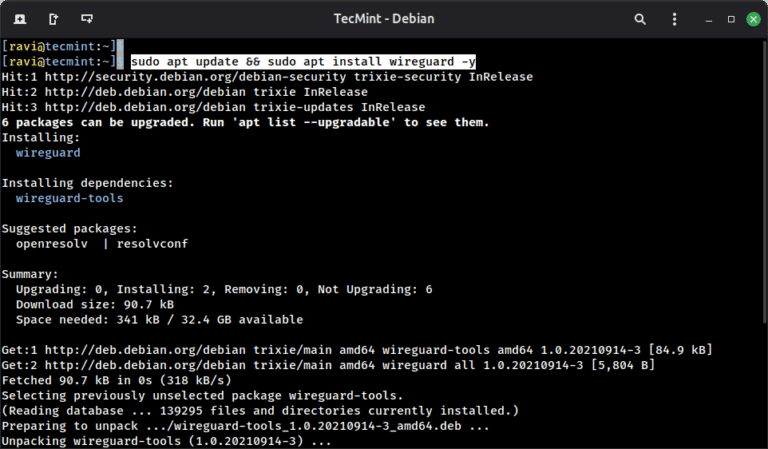
WireGuard is a modern VPN protocol built directly into the Linux kernel since version 5.6, and…
Building on our August 2025 integration launch that introduced visibility into AI agents and security configurations,…
Innovation and Growth Recognized by Frost & Sullivan Our investment in AI security extends beyond automation…

Complexity has become a defining security challenge as organizations expand across hybrid and multi-cloud environments. In…
This shift is critical in today’s threat landscape. Adversaries move across identity, endpoint, and cloud in…
Alert noise is a persistent challenge for security teams. Analysts in siloed environments often have to…
Securing AI starts where AI executes: on the endpoint. CrowdStrike has been capturing process-level telemetry on…
As discovery becomes faster and more automated, the ability to validate exposure and act on it…
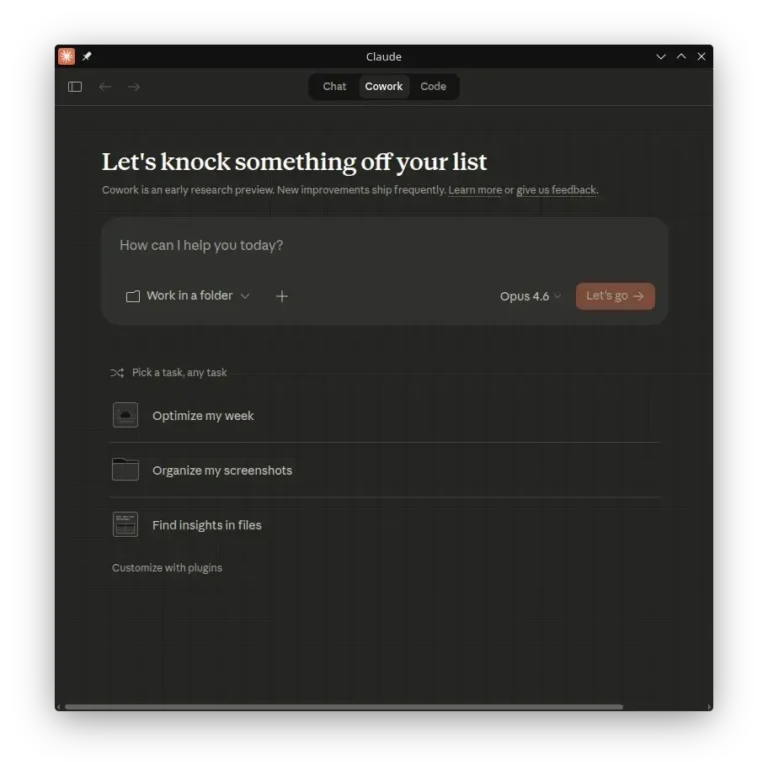
In this guide, we’ll explain what claude-desktop-debian is, how to build the native package without wine,…
Frontier labs drive AI innovation. CrowdStrike delivers the intelligence, protection, and governance to put it to…
Exploited Zero-Day Vulnerability in Microsoft SharePoint Server CVE-2026-23666 is a Critical denial-of-service (DoS) vulnerability affecting the…