Anthropic Claude Mythos Preview: The More Capable AI Becomes, the More Security It Needs
A frontier model is the engine. Data is the fuel. The platform is how you operationalize…
A frontier model is the engine. Data is the fuel. The platform is how you operationalize…
When a high-profile vulnerability is disclosed, teams need to move quickly and with confidence in the…
A recommended execution cadence is weekly or monthly to maintain posture awareness and support audit requirements.While…
Before a client can authenticate to a service, it must resolve the service hostname to an…
Charlotte Agentic SOAR provides the critical components needed to operationalize an agentic defense: It brings together:…

This is critical in a world where data exposure may stem from employee negligence, malicious insider…

Legacy SIEMs, fragmented toolchains, and manual workflows cannot keep up with the scale and complexity of…

By correlating runtime application behavior with cloud infrastructure findings, Application Explorer gives organizations a precise view…
Customers can establish a committed response path in the event of an incident while also using…
Falcon Onum introduces a new paradigm for data management by allowing teams to intelligently prioritize and…
Cloud environments are where AI is built, trained, and deployed at scale. Organizations are deploying AI…
An initial spike on Linux platforms linked to runners was observed on March 19, 2026. The…
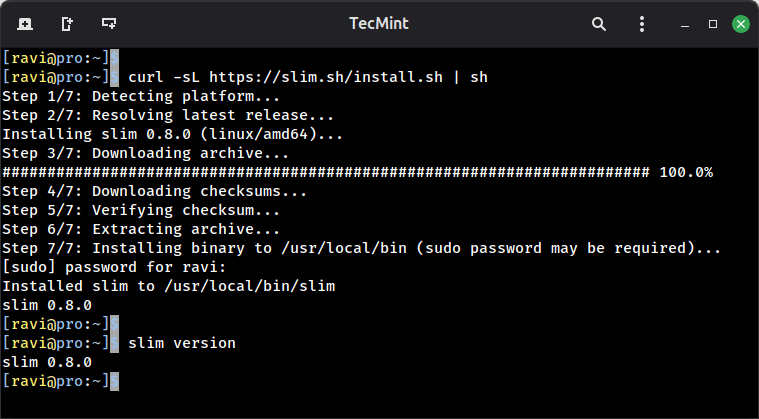
If you do any kind of local web development on Linux, you have almost certainly run…
Falcon AIDR and its corresponding API enable teams to create named detection policies tailored to their…
This milestone underscores our commitment to protecting the federal government’s most critical systems from modern threats. …