Exploited Zero-Day Vulnerability in Microsoft SharePoint Server
CVE-2026-23666 is a Critical denial-of-service (DoS) vulnerability affecting the .NET Framework and has a CVSS score of 7.5. This vulnerability allows unauthenticated remote attackers to exploit an improper handling of exceptional conditions flaw (CWE-755) to cause a DoS condition on affected systems. It requires no user interaction and has low attack complexity. An official fix is available for customers to deploy.
CVE-2026-32190, CVE-2026-33114, and CVE-2026-33115 are Critical remote code execution vulnerabilities affecting Microsoft Office and Microsoft Word, all with a CVSS score of 8.4. These vulnerabilities allow unauthenticated attackers to execute arbitrary code by exploiting a use-after-free flaw (CVE-2026-32190 and CVE-2026-33115) and an untrusted pointer dereference flaw (CVE-2026-33114) in Microsoft Office components. None of the three vulnerabilities requires user interaction, and all have low attack complexity. While no user interaction is required, an attacker would still need to cause a crafted file to be saved on a victim system.
| Severity | CVSS Score | CVE | Description |
| Important | 6.5 | CVE-2026-32201 | Microsoft SharePoint Server Spoofing Vulnerability |
Disclosed Zero-Day Vulnerability in Microsoft Defender
An attacker that successfully exploits this vulnerability could view sensitive information and make changes to disclosed information, impacting both confidentiality and integrity of the affected system. Availability is not impacted. An official fix is available for customers to deploy.
Regular review of your patching strategy should still be a part of your program, but you should also look more holistically at your organization’s methods for cybersecurity and improve your overall security posture.
| Severity | CVSS Score | CVE | Description |
| Important | 7.8 | CVE-2026-33825 | Microsoft Defender Elevation of Privilege Vulnerability |
Critical Vulnerability in Windows TCP/IP
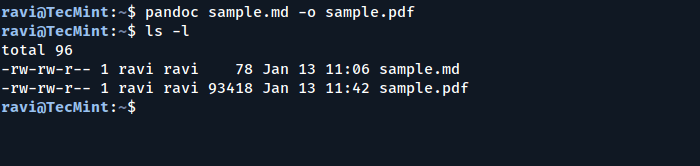
For a visual overview of the systems impacted by this month’s vulnerabilities, you can use our Patch Tuesday dashboard. This can be found in the CrowdStrike Falcon® platform within the Exposure Management > Vulnerability Management > Dashboards page. The preset dashboards show the most recent three months of Patch Tuesday vulnerabilities.
The Preview Pane is an attack vector for all three vulnerabilities. As such, an attacker could create a specially crafted file that executes malicious code on the victim’s machine simply through the preview pane, without requiring the victim to open the file. An official fix is available for customers to deploy.
| Severity | CVSS Score | CVE | Description |
| Critical | 8.1 | CVE-2026-33827 | Windows TCP/IP Remote Code Execution Vulnerability |
Critical Vulnerability in Windows Internet Key Exchange (IKE) Service Extensions
The CrowdStrike Falcon platform regularly collects and analyzes trillions of endpoint events every day from millions of sensors deployed across 176 countries. Watch this demo to see the Falcon platform in action.
This vulnerability had been publicly disclosed prior to a patch being released, though there is no evidence of exploitation in the wild. Proof-of-concept exploit code exists, and Microsoft assesses exploitation as more likely. An official fix is available for customers to deploy, though for some systems this update will be installed automatically with no action required. It is presumed this is the CVE for the BlueHammer exploit released on April 2, 2026, though there is no official confirmation at the time this blog was written.
The Common Vulnerability Scoring System (CVSS) is a free and open industry standard that CrowdStrike and many other cybersecurity organizations use to assess and communicate software vulnerabilities’ severity and characteristics. The CVSS Base Score ranges from 0.0 to 10.0, and the National Vulnerability Database (NVD) adds a severity rating for CVSS scores. Learn more about vulnerability scoring in this article.
| Severity | CVSS Score | CVE | Description |
| Critical | 9.8 | CVE-2026-33824 | Windows Internet Key Exchange (IKE) Service Extensions Remote Code Execution Vulnerability |
Critical Vulnerability in Remote Desktop Client
CVE-2026-33824 is a Critical remote code execution vulnerability affecting Windows Internet Key Exchange (IKE) Service Extensions and has a CVSS score of 9.8. It allows unauthenticated remote attackers to execute arbitrary code by exploiting a double free flaw (CWE-415) in the Windows IKE Extension. No user interaction is required and attack complexity is low.
CVE-2026-32201 is an Important spoofing vulnerability affecting Microsoft SharePoint Server and has a CVSS score of 6.5. It has been exploited in the wild as a zero-day. This vulnerability allows unauthenticated remote attackers to perform spoofing by exploiting an improper input validation flaw (CWE-20) in Microsoft Office SharePoint. No user interaction is required and attack complexity is low.
| Severity | CVSS Score | CVE | Description |
| Critical | 8.8 | CVE-2026-32157 | Remote Desktop Client Remote Code Execution Vulnerability |
Critical Vulnerabilities in Microsoft Office and Microsoft Word
CVE-2026-32157 is a Critical remote code execution vulnerability affecting Remote Desktop Client and has a CVSS score of 8.8. This vulnerability allows unauthenticated remote attackers to execute arbitrary code by exploiting a use-after-free flaw (CWE-416) in the Remote Desktop Client. It requires user interaction and has low attack complexity.
For customers who cannot immediately apply the update, Microsoft recommends blocking inbound traffic on UDP ports 500 and 4500 for systems that do not use IKE, or restricting inbound traffic on those ports to known peer addresses only for systems that require IKE. Note that these mitigations reduce attack surface but do not replace applying the security update.
| Severity | CVSS Score | CVE | Description |
| Critical | 8.4 | CVE-2026-32190 | Microsoft Office Remote Code Execution Vulnerability |
| Critical | 8.4 | CVE-2026-33114 | Microsoft Word Remote Code Execution Vulnerability |
| Critical | 8.4 | CVE-2026-33115 | Microsoft Word Remote Code Execution Vulnerability |
Critical Vulnerability in Windows Active Directory
Learn more about how CrowdStrike Falcon® Exposure Management can help you quickly and easily discover and prioritize vulnerabilities and other types of exposures here.
An authenticated attacker could exploit this vulnerability by sending a specially crafted RPC call to an RPC host, potentially resulting in remote code execution on the server side with the same permissions as the RPC service. Successful exploitation requires the attacker to be within the same restricted Active Directory domain as the target system. An official fix is available for customers to deploy.
| Severity | CVSS Score | CVE | Description |
| Critical | 8.0 | CVE-2026-33826 | Windows Active Directory Remote Code Execution Vulnerability |
Critical Vulnerability in .NET Framework
CVE-2026-33827 is a Critical remote code execution vulnerability affecting Windows TCP/IP and has a CVSS score of 8.1. This vulnerability allows unauthenticated remote attackers to execute arbitrary code by exploiting a race condition flaw (CWE-362) in the Windows TCP/IP stack. It requires no user interaction, though it carries high attack complexity.
| Severity | CVSS Score | CVE | Description |
| Critical | 7.5 | CVE-2026-23666 | .NET Framework Denial of Service Vulnerability |
Patch Tuesday Dashboard in the Falcon Platform
An unauthenticated attacker could exploit this vulnerability by sending specially crafted packets to a Windows machine with Internet Key Exchange (IKE) version 2 enabled, which could enable remote code execution on the target system. An official fix is available for customers to deploy.
Not All Relevant Vulnerabilities Have Patches: Consider Mitigation Strategies
An attacker with control of a malicious Remote Desktop Server could exploit this vulnerability by enticing a victim to connect to the attacker-controlled server using a vulnerable Remote Desktop Client. Upon connection, the attacker could trigger remote code execution on the victim’s machine. The attack targets the client side of the Remote Desktop connection, meaning the risk lies with users initiating connections to untrusted or compromised servers. An official fix is available for customers to deploy.
An unauthenticated attacker could exploit this vulnerability by sending a specially crafted IPv6 packet to a Windows node where IPSec is enabled. Successful exploitation requires the attacker to win a race condition and take additional preparatory actions to configure the target environment prior to exploitation. An official fix is available for customers to deploy.
Learn More
CVE-2026-33826 is a Critical remote code execution vulnerability affecting Windows Active Directory and has a CVSS score of 8.0. This vulnerability allows authenticated attackers to execute arbitrary code by exploiting an improper input validation flaw (CWE-20) in Windows Active Directory. It requires no user interaction and has low attack complexity.
CVE-2026-33825 is an Important elevation of privilege vulnerability affecting Microsoft Defender and has a CVSS score of 7.8. This vulnerability allows local attackers with low privileges to elevate their privileges by exploiting an insufficient granularity of access control flaw (CWE-1220) in Microsoft Defender. It requires no user interaction and has low attack complexity. An attacker that successfully exploits this vulnerability could gain SYSTEM privileges.
About CVSS Scores
As we have learned with other notable vulnerabilities, such as Log4j, not every highly exploitable vulnerability can be easily patched. As is the case for the ProxyNotShell vulnerabilities, it’s critically important to develop a response plan for how to defend your environments when no patching protocol exists.