How to Protect Identities and Sessions from Infostealers
Financial LossesThe impact of an infostealer attack can be devastating. Because infostealers quietly extract sensitive data,…
Financial LossesThe impact of an infostealer attack can be devastating. Because infostealers quietly extract sensitive data,…
Learn more: Download the CrowdStrike 2026 Financial Services Threat Landscape Report The trends outlined in this…
Critical Vulnerability in Azure DevOps CVE-2026-33823 is a Critical information disclosure vulnerability affecting the Microsoft Teams…
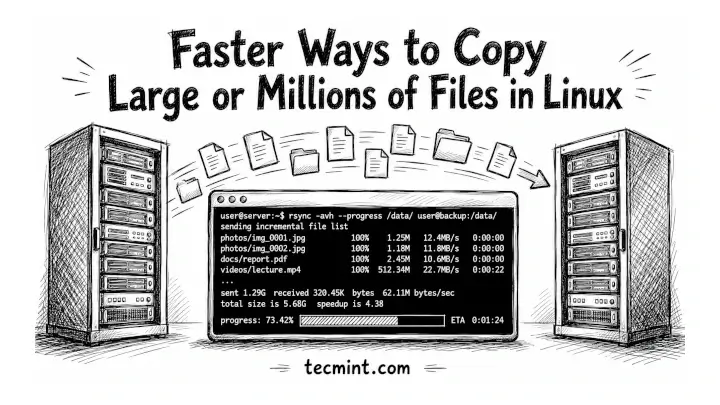
You’ve been copying files with cp for years, and if you’re moving a 50GB backup or…
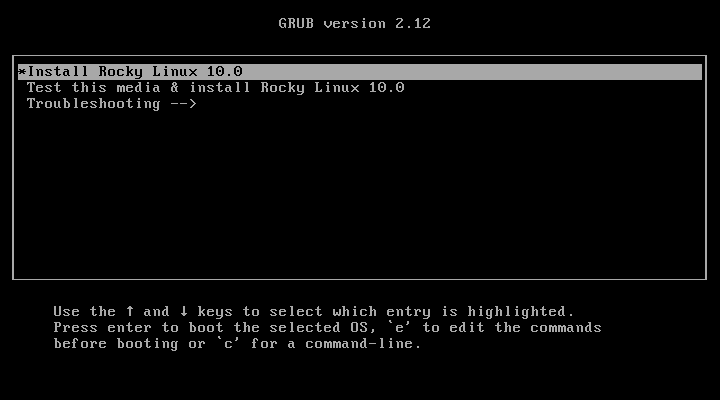
Rocky Linux 10 is the latest stable, community-driven enterprise Linux distribution built as a downstream rebuild…
In our Technical Risk Assessments, we consistently find that this external footprint is larger and more…
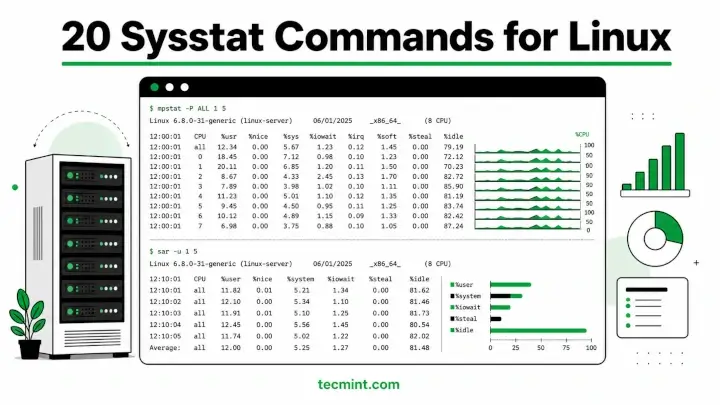
Sysstat is a collection of performance monitoring utilities for Linux that includes mpstat, pidstat, iostat, and…
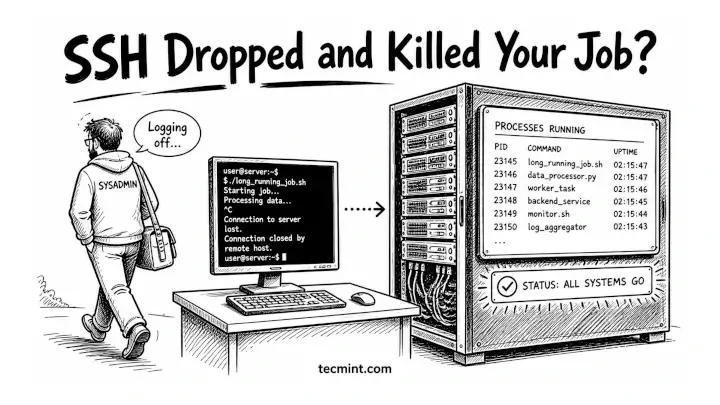
You’ve been running a long rsync job or a Python script on a remote server only…
This blog details how these adversaries operate and how CrowdStrike Falcon® Shield identifies and disrupts their…
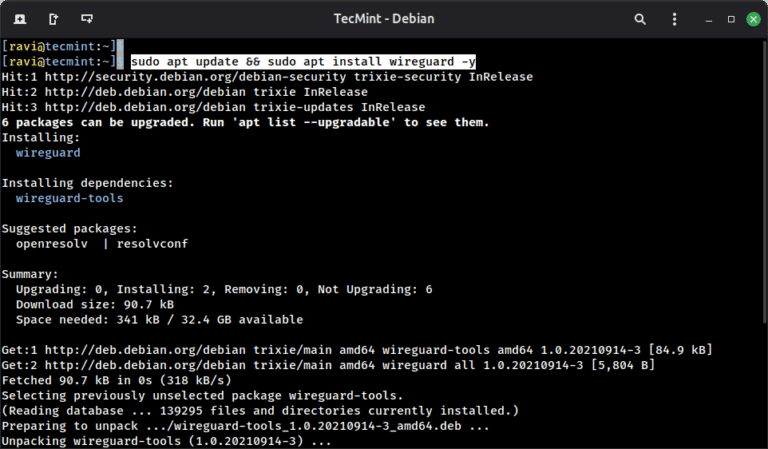
WireGuard is a modern VPN protocol built directly into the Linux kernel since version 5.6, and…
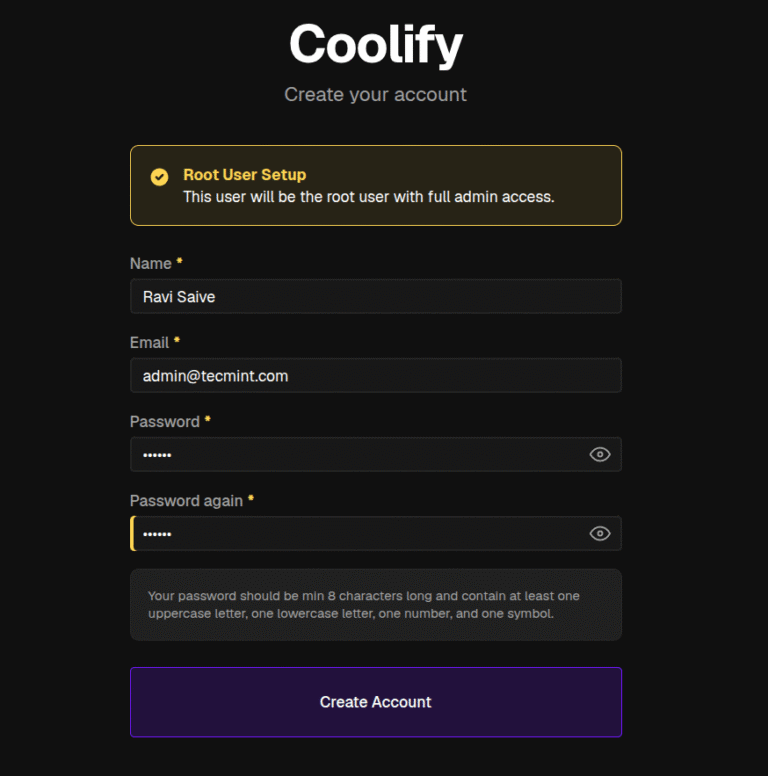
Coolify is an open-source, self-hosted platform that deploys web apps, databases, and services on your own…
Frontier labs drive AI innovation. CrowdStrike delivers the intelligence, protection, and governance to put it to…
When a high-profile vulnerability is disclosed, teams need to move quickly and with confidence in the…
Falcon Onum introduces a new paradigm for data management by allowing teams to intelligently prioritize and…
An initial spike on Linux platforms linked to runners was observed on March 19, 2026. The…