CrowdStrike and Zscaler Bring Continuous Identity to Zero Trust Access
A rule configured in Falcon Next-Gen Identity Security’s CAEP Hub triggers a risk level change event,…

A rule configured in Falcon Next-Gen Identity Security’s CAEP Hub triggers a risk level change event,…
In this guide, we explore the best Microsoft Teams alternatives for Linux that you can use…
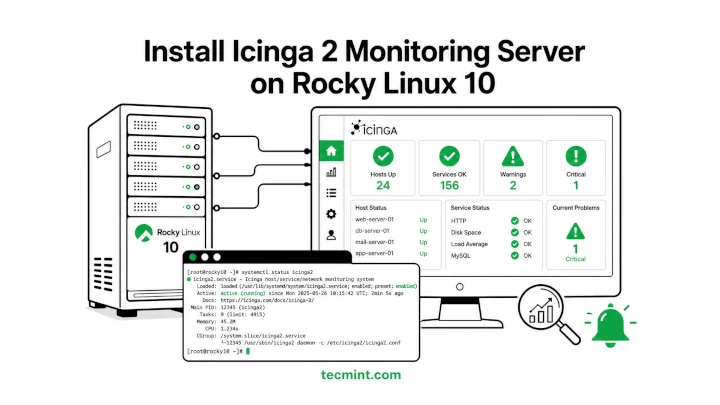
Icinga 2 is a free and open-source monitoring tool that helps you keep an eye on…
Cockpit ships pre-installed on Rocky Linux 10 and gives you a browser-based dashboard for managing your…
Employees may unknowingly input sensitive information into AI chatbots, GenAI tools, or third-party platforms. Once the…

Rocky Linux 10 replaced VNC with RDP (Remote Desktop Protocol) for remote graphical installations, so if…
This content includes discussion of unreleased services or features. Any references to unreleased features reflect our…
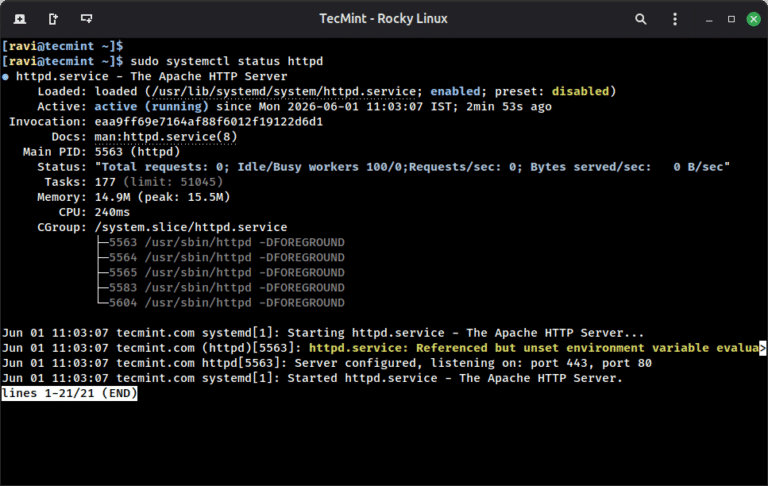
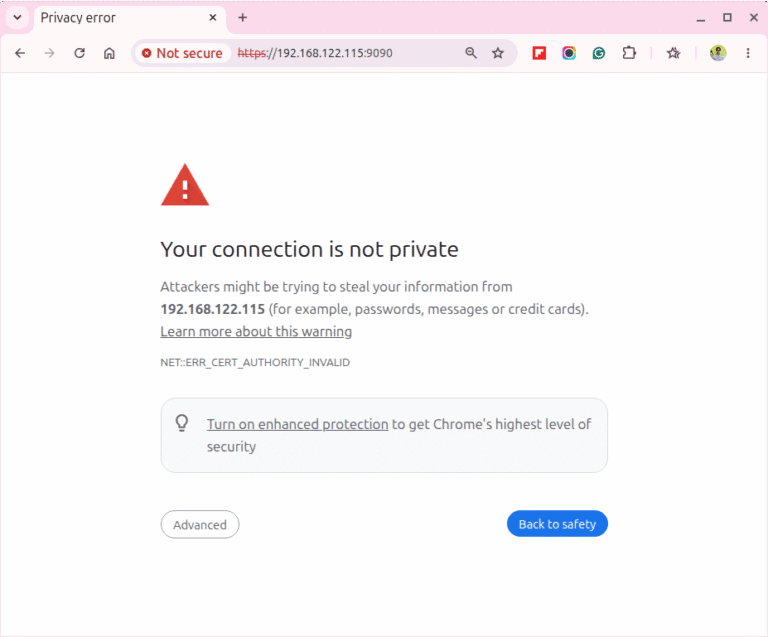
A self-signed SSL certificate lets you run Apache over HTTPS on Rocky Linux 10 without buying…
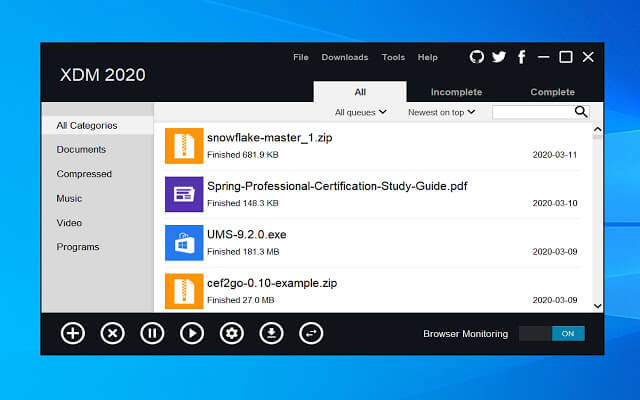
One thing many people miss after switching from Windows to Linux is a good download manager….
Enterprises face new AI-specific attacks. For example, prompt injection techniques can manipulate models into exposing information,…
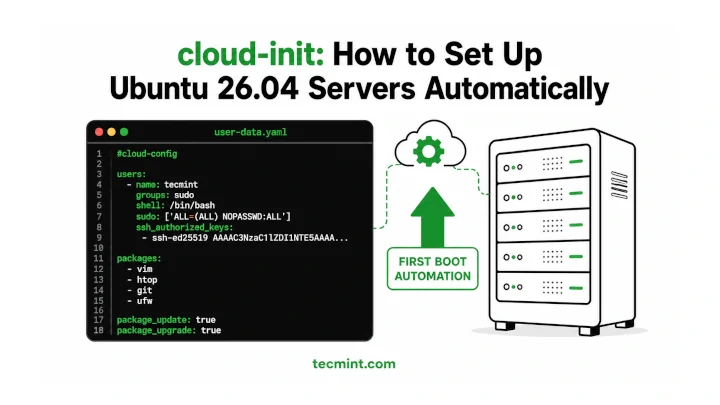
Installing and configuring cloud-init on Ubuntu 26.04 makes it much easier to automate server setup, especially…
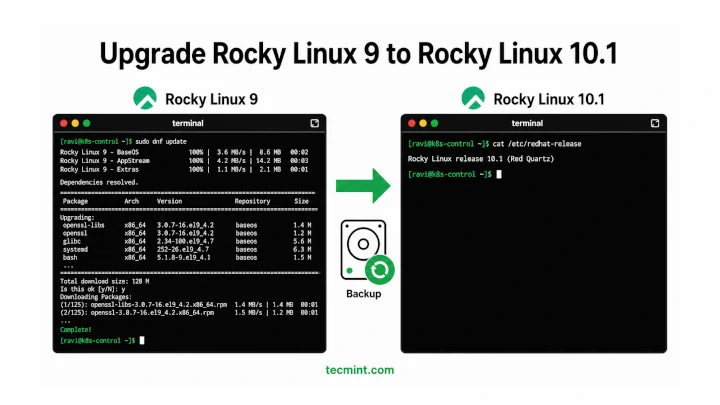
In this article, we’ll show you how to move from Rocky Linux 9 to Rocky Linux…

Netplan is the default network configuration tool on Ubuntu since 18.04, replacing the older ifupdown system…
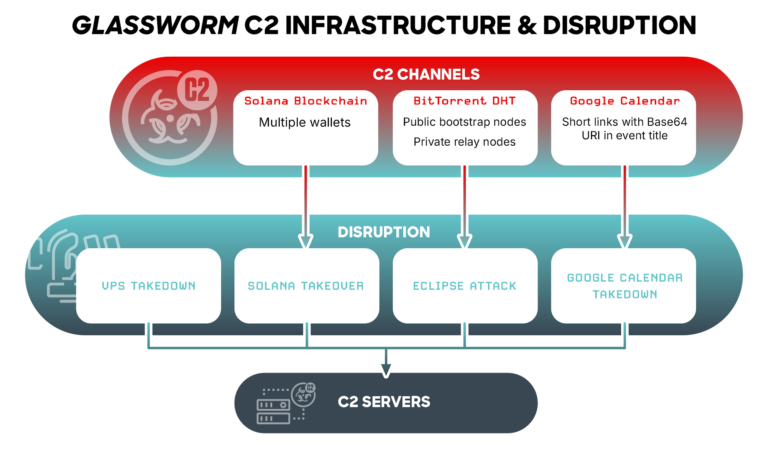
This case demonstrates: rule CrowdStrike_GlasswormRat_01 : glassworm glasswormrat { meta: copyright = “(c) 2026 CrowdStrike Inc.”…
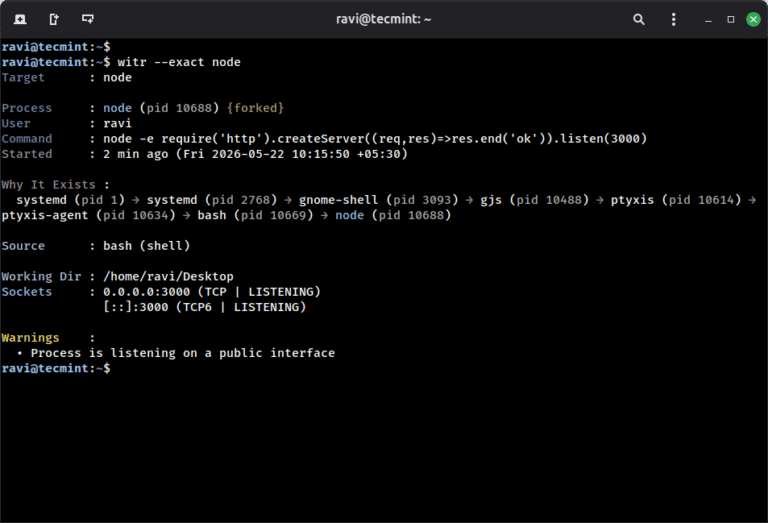
ps aux shows you what is running on your system, but witr goes a step further…