CrowdStrike Falcon Cloud Security Delivered 264% ROI Through Unified Cloud Protection
This shift is critical in today’s threat landscape. Adversaries move across identity, endpoint, and cloud in…
This shift is critical in today’s threat landscape. Adversaries move across identity, endpoint, and cloud in…

Complexity has become a defining security challenge as organizations expand across hybrid and multi-cloud environments. In…
Alert noise is a persistent challenge for security teams. Analysts in siloed environments often have to…
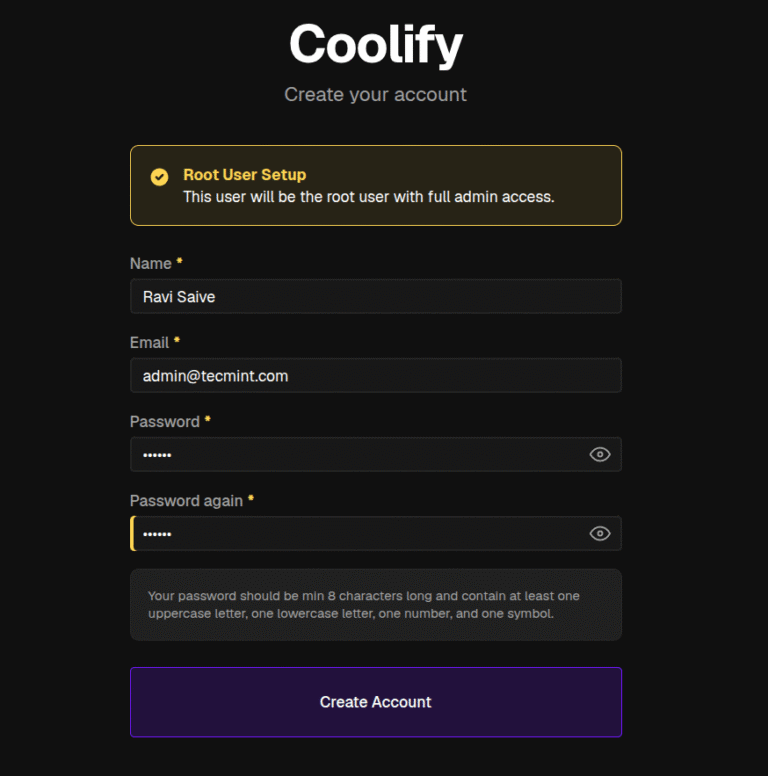
Coolify is an open-source, self-hosted platform that deploys web apps, databases, and services on your own…
Securing AI starts where AI executes: on the endpoint. CrowdStrike has been capturing process-level telemetry on…
As discovery becomes faster and more automated, the ability to validate exposure and act on it…
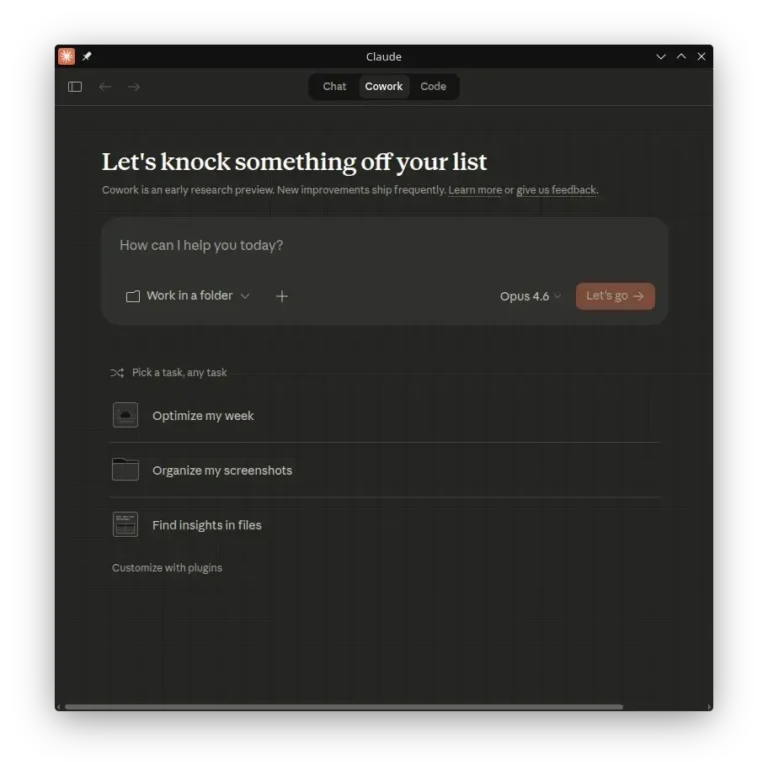
In this guide, we’ll explain what claude-desktop-debian is, how to build the native package without wine,…
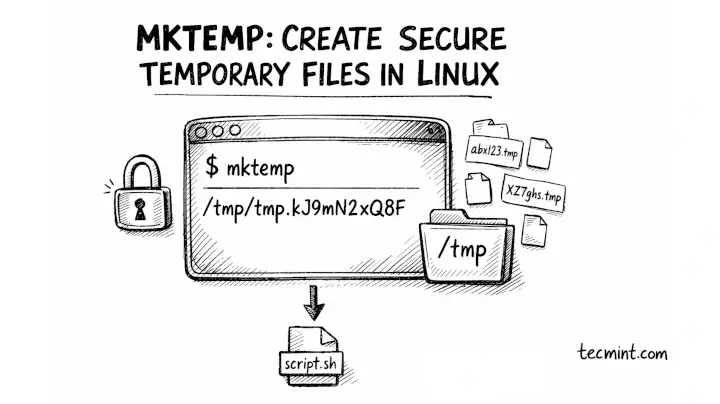
The mktemp command in Linux creates temporary files and directories with unique, unpredictable names, which is…
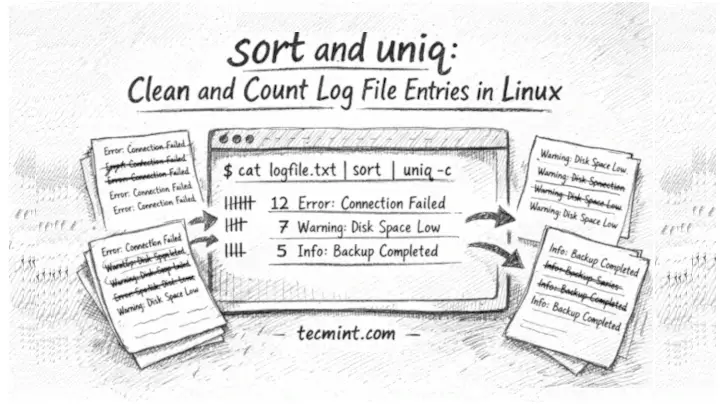
In this guide, we’ll show you how to use sort and uniq together to deduplicate, count,…
Frontier labs drive AI innovation. CrowdStrike delivers the intelligence, protection, and governance to put it to…
Exploited Zero-Day Vulnerability in Microsoft SharePoint Server CVE-2026-23666 is a Critical denial-of-service (DoS) vulnerability affecting the…
What often gets overlooked is how rarely those early platform choices evolve with the business. What…
One of the biggest shifts in SaaS right now is the renewed focus on efficiency. Sustainable…

Instead of optimizing for individual team success, the focus shifts to optimizing the entire revenue engine.The…

Durable revenue comes from merchants who stay, grow, and succeed over time. Not just those who…