3 Principles to Safely Scale Agentic AI
Organizations need to treat AI agents as privileged identities from Day One. This means enforcing least-privilege…
Organizations need to treat AI agents as privileged identities from Day One. This means enforcing least-privilege…
A process suddenly consuming 99% of your CPU at 2 AM can turn a stable server…
For example, teams can identify when sensitive data such as PII appears within a pipeline, even…
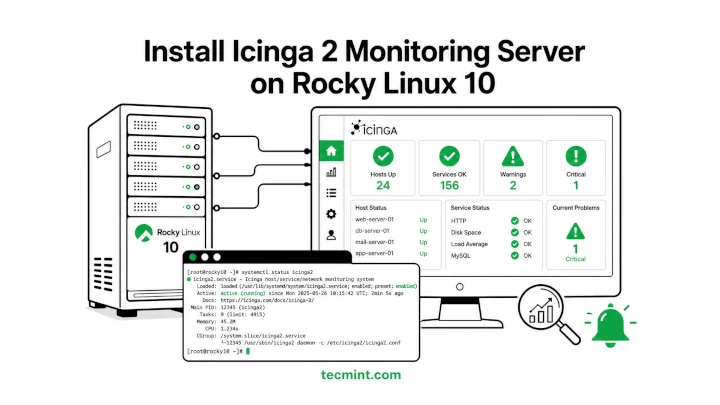
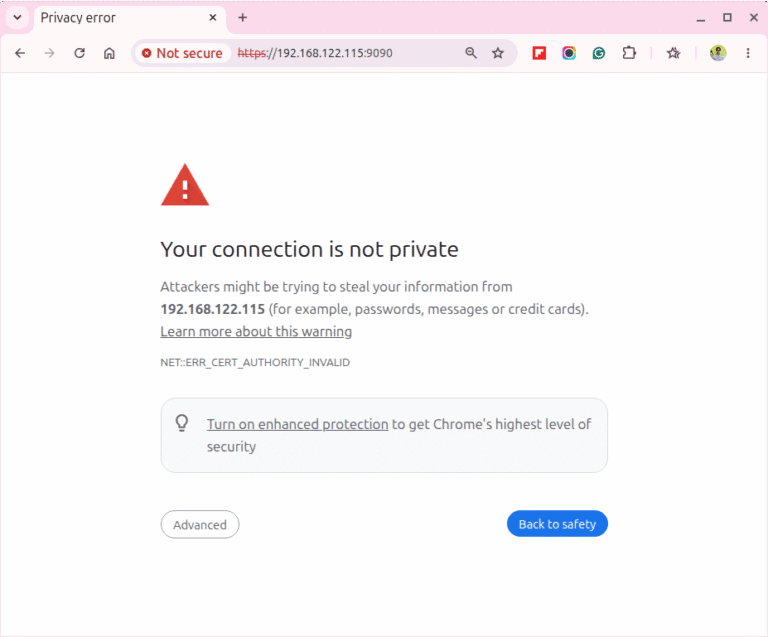
Icinga 2 is a free and open-source monitoring tool that helps you keep an eye on…
Cockpit ships pre-installed on Rocky Linux 10 and gives you a browser-based dashboard for managing your…
Employees may unknowingly input sensitive information into AI chatbots, GenAI tools, or third-party platforms. Once the…
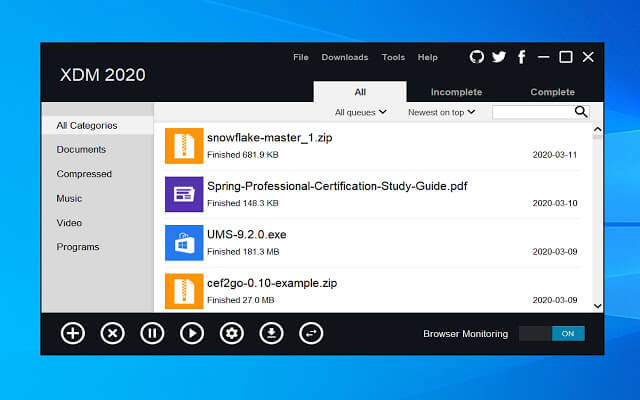
One thing many people miss after switching from Windows to Linux is a good download manager….
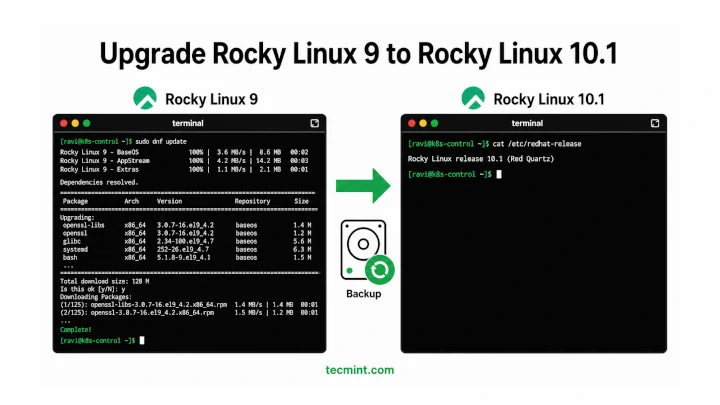
In this article, we’ll show you how to move from Rocky Linux 9 to Rocky Linux…
What it measures: The percentage of employees using approved AI tools, how frequently they use them,…
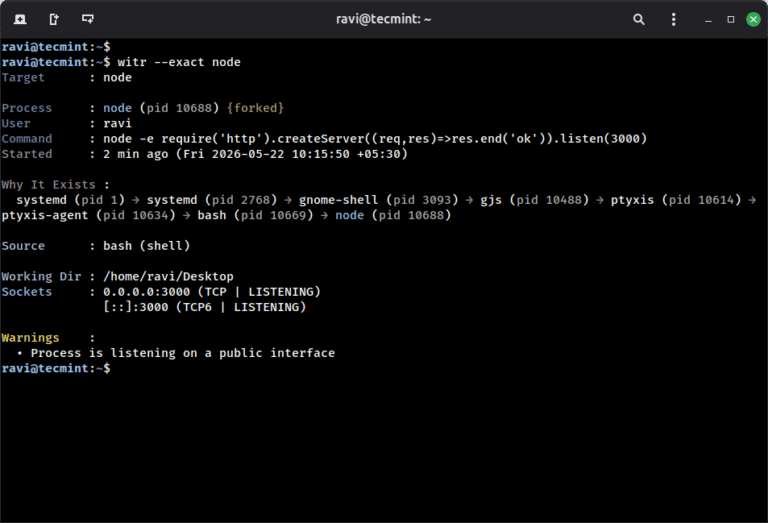
ps aux shows you what is running on your system, but witr goes a step further…
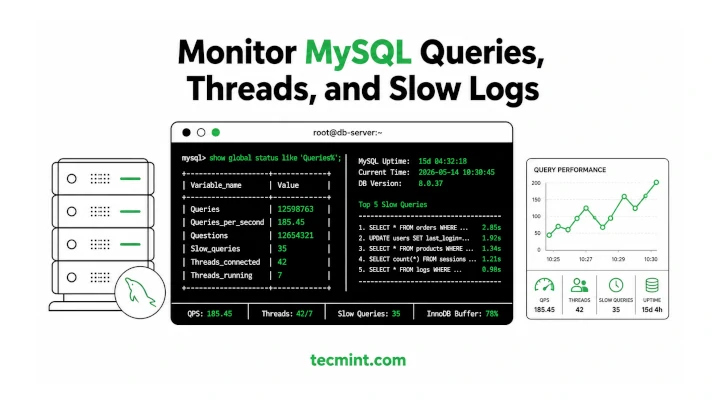
MySQL ships with decent built-in diagnostics, but when your database is slowing down under load, you…
Improving detection is a core driver for the CrowdStrike Advanced Research team, which is behind the…
In our Technical Risk Assessments, we consistently find that this external footprint is larger and more…
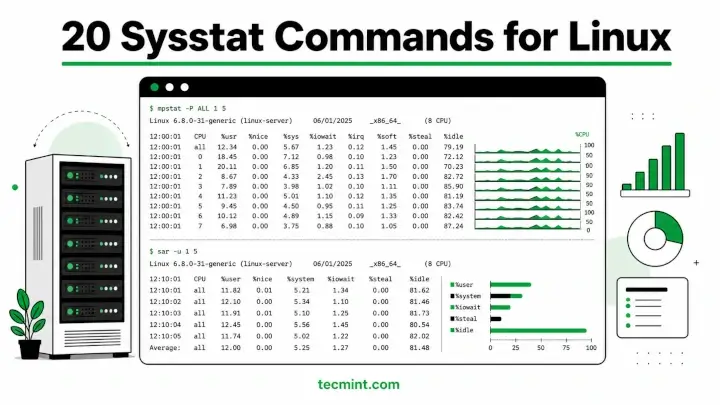
Sysstat is a collection of performance monitoring utilities for Linux that includes mpstat, pidstat, iostat, and…
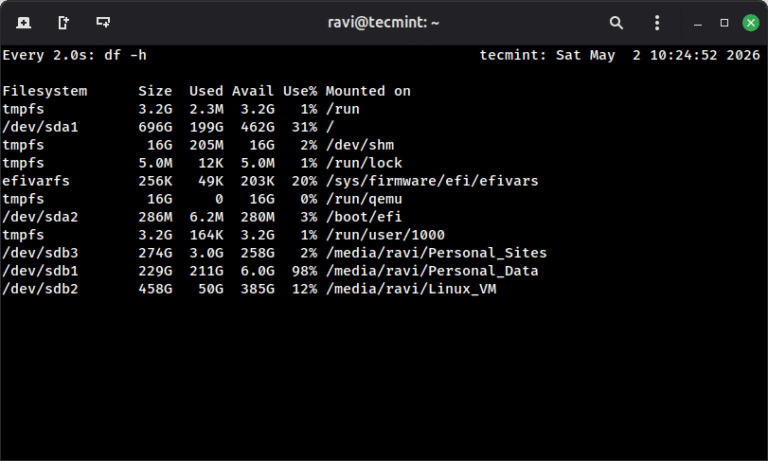
You’re running df -h every 30 seconds by hand to watch a disk fill up, typing…