SSH Dropped and Killed Your Job? Here’s the Fix
You’ve been running a long rsync job or a Python script on a remote server only…
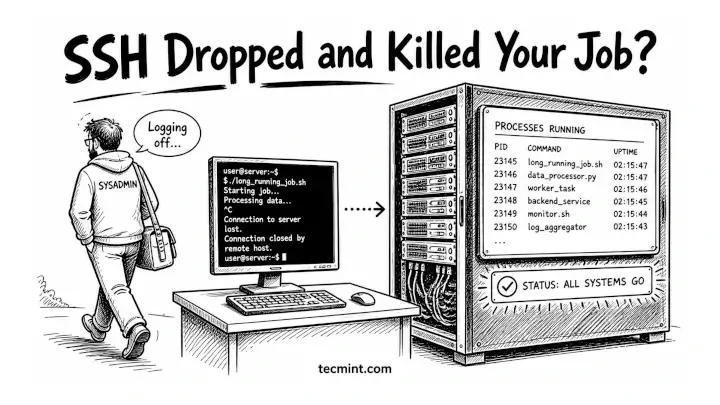
You’ve been running a long rsync job or a Python script on a remote server only…
Building on our August 2025 integration launch that introduced visibility into AI agents and security configurations,…
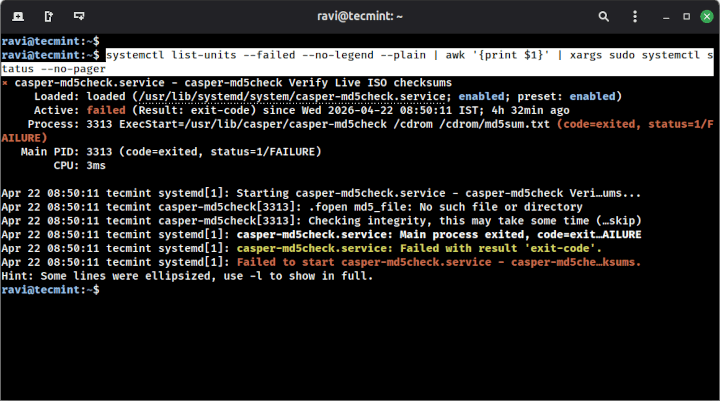
Learn how to use systemctl with the –failed flag to instantly spot broken services on your…

Complexity has become a defining security challenge as organizations expand across hybrid and multi-cloud environments. In…
This shift is critical in today’s threat landscape. Adversaries move across identity, endpoint, and cloud in…
Securing AI starts where AI executes: on the endpoint. CrowdStrike has been capturing process-level telemetry on…
A recommended execution cadence is weekly or monthly to maintain posture awareness and support audit requirements.While…
Before a client can authenticate to a service, it must resolve the service hostname to an…
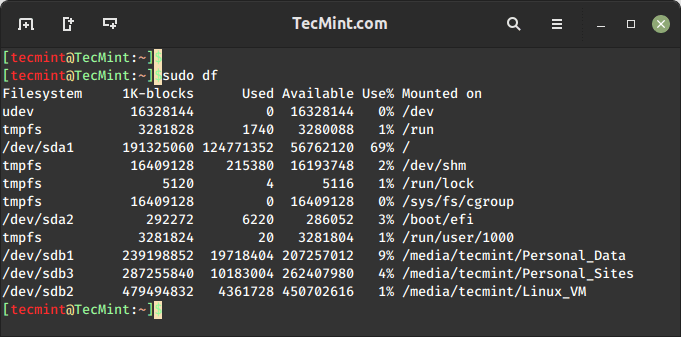
On the internet, you will find plenty of tools for checking disk space usage in Linux….

By correlating runtime application behavior with cloud infrastructure findings, Application Explorer gives organizations a precise view…
Cloud environments are where AI is built, trained, and deployed at scale. Organizations are deploying AI…
Falcon AIDR and its corresponding API enable teams to create named detection policies tailored to their…
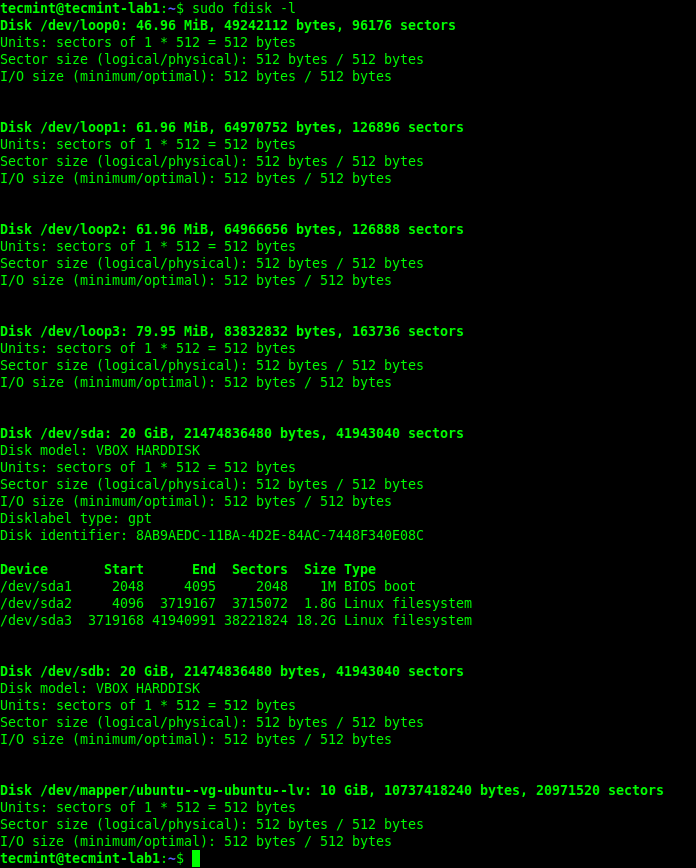
Whether you’re troubleshooting boot issues, preparing to format a drive, or setting up a new disk,…
There are several ways to find out which version of Linux you’re running on your system,…
SOCKS5 At launch, Enhanced Network Visibility will support parsing of plaintext HTTP requests and responses and…