The Definitive Guide to Data Gravity: Mastering Performance, Compliance, and Architecture in Hybrid and Multi-Cloud
Table of Contents What Is Data Gravity? The History and Evolution of Data Gravity Why Data…
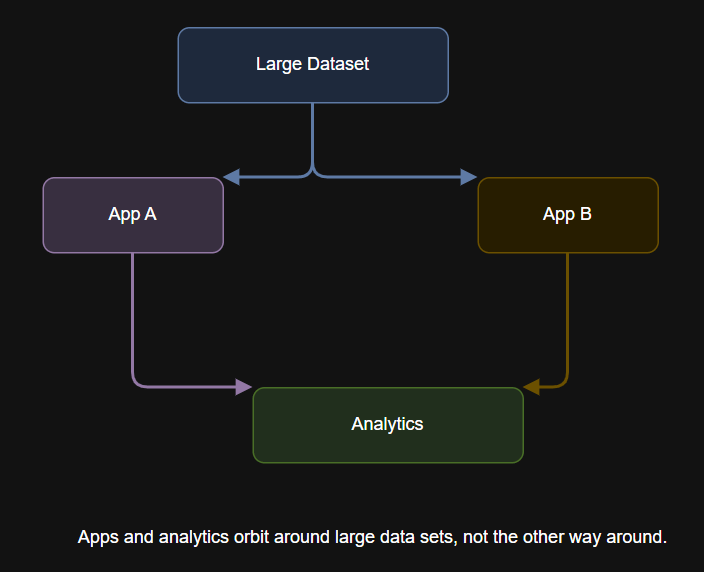
Table of Contents What Is Data Gravity? The History and Evolution of Data Gravity Why Data…
A Leader in Exposure Management The report notes, “Network-based vulnerability scanning was recently added to the…
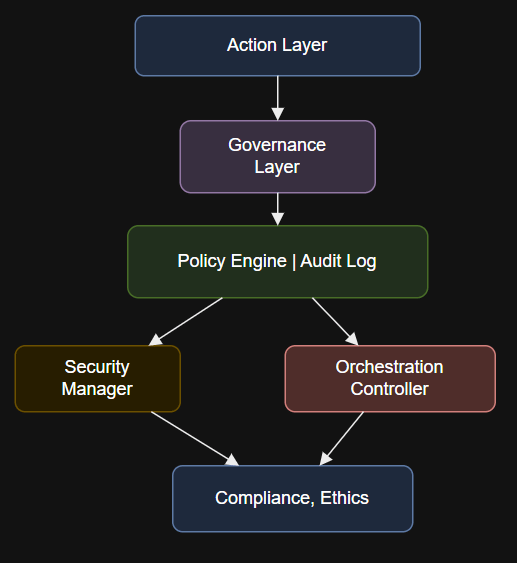
Introduction if __name__ == “__main__”:# Example: Validate if a user action is allowed by enterprise policyinput_payload…
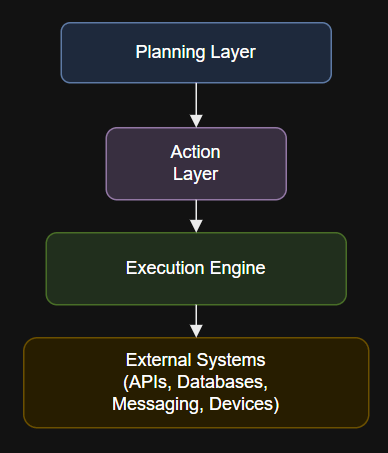
Introduction @app.task(bind=True, max_retries=3)def execute_api_action(self, endpoint, payload):try:response = requests.post(endpoint, json=payload, timeout=10)response.raise_for_status()return {“status”: “success”, “response”: response.json()}except Exception as…
Since late 2024, CrowdStrike Counter Adversary Operations has observed significant activity conducted by MURKY PANDA, a…

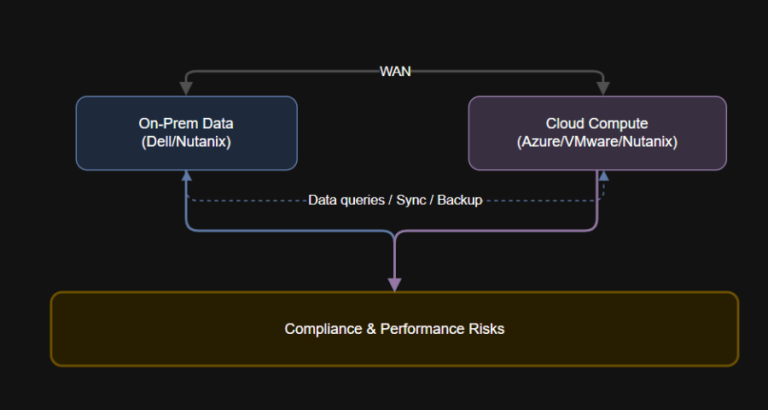
Introduction A global retailer must store EU customer data within European borders to comply with GDPR….

CrowdStrike is excited to announce CrowdStrike Falcon® Next-Gen Identity Security, a new solution built to protect…
The Adversary’s Path to Achieving Persistence Once SCATTERED SPIDER gains access to a target organization, they…
“CrowdStrike’s cloud-native security platform employs an adversarial approach, consolidating telemetry from various security domains to deliver…
Publicly Disclosed Zero-Day Vulnerability in Windows Kerberos As we have learned with other notable vulnerabilities, such…
Introduction: What Is Data Gravity? Data gravity is a defining factor in successful cloud migration and…

Where these traditional tools stay silent, CrowdStrike Signal takes action. It identifies activity that deviates from…
AI must be deployed strategically in the SOC to outpace AI-savvy adversaries. The Threat Hunting Report…
But with this integration comes risk. AI agents are often quickly deployed across SaaS environments by…
With Falcon Shield’s integration with OpenAI ChatGPT Enterprise Compliance API, IT and security teams gain added…