CrowdStrike Collaborates with AI Leaders to Secure AI Across the Enterprise
As enterprises adopt AI agents and embed them into SaaS workflows, visibility and governance become essential….
As enterprises adopt AI agents and embed them into SaaS workflows, visibility and governance become essential….
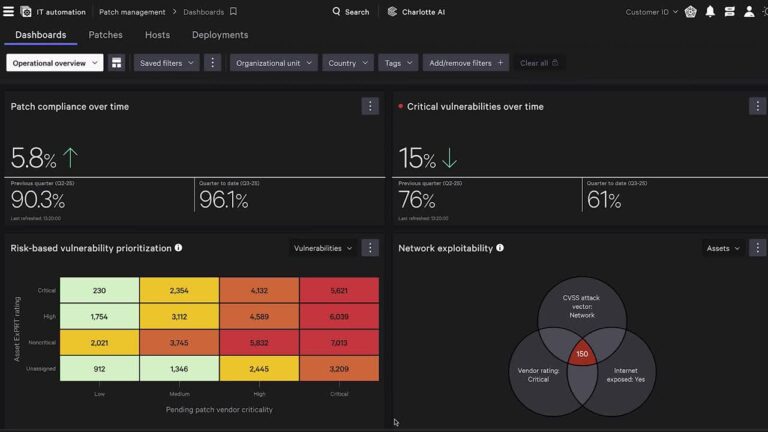
Traditional vulnerability management is broken. Security teams rely on one set of tools to find vulnerabilities;…
The Falcon platform’s console unifies fragmented data, bridges silos, and translates complex queries into natural-language conversations….
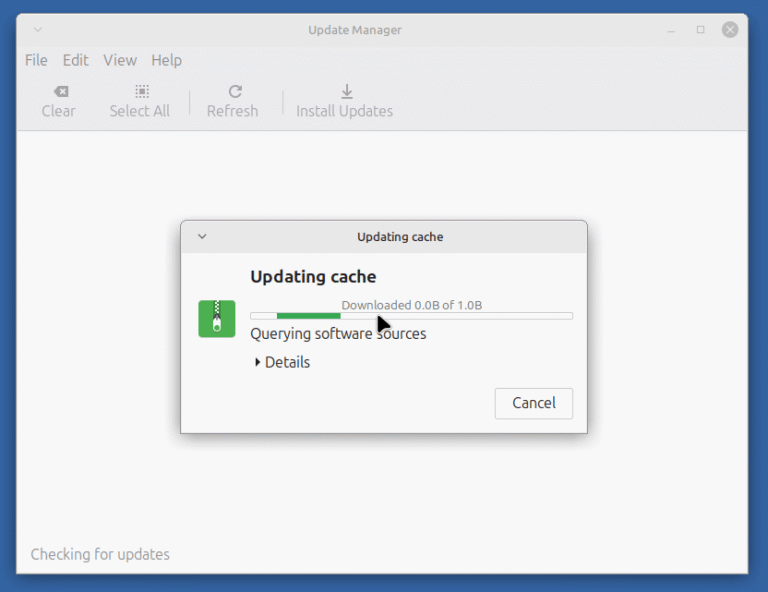
Linux Mint 22.2 (“Zara”) is the latest point release in the Linux Mint 22 series, which…
With Pangea, CrowdStrike will extend this protection into the interaction layer of AI to secure how…
The Hub doesn’t just display what’s happening — it tells teams what to do about it…
Publicly Disclosed Zero-Day Vulnerability in Windows SMB CVE-2025-55226 is a Critical remote code execution vulnerability affecting…
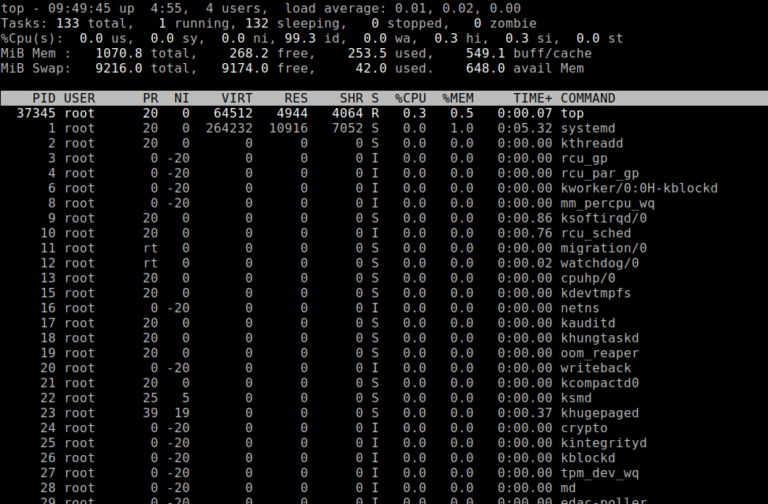
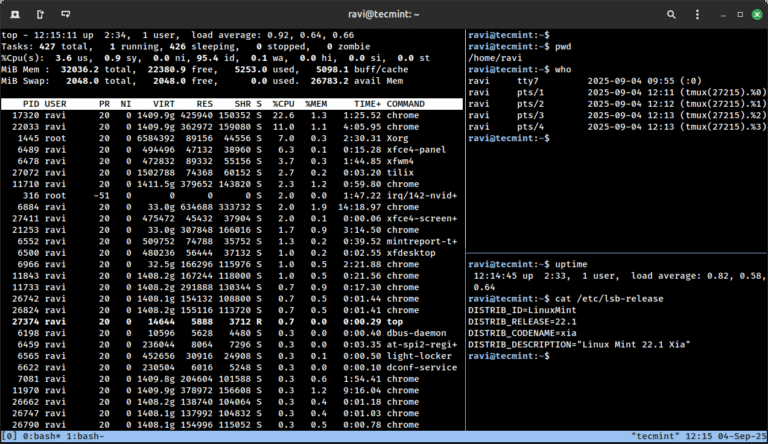
Being a System or Network administrator tasked with monitoring and debugging Linux system performance problems on…
It is time once again to share a list of the best free and open-source software…
A Visionary Leader in MDR See what other industry analysts are saying about CrowdStrike on our…
Core Technology that Powers Security for AI Data remains the primary target for adversaries, but traditional…
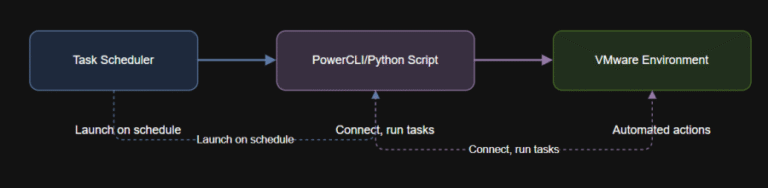
Learning Objectives By the end of this article, you will: Schedule PowerCLI and Python scripts for…
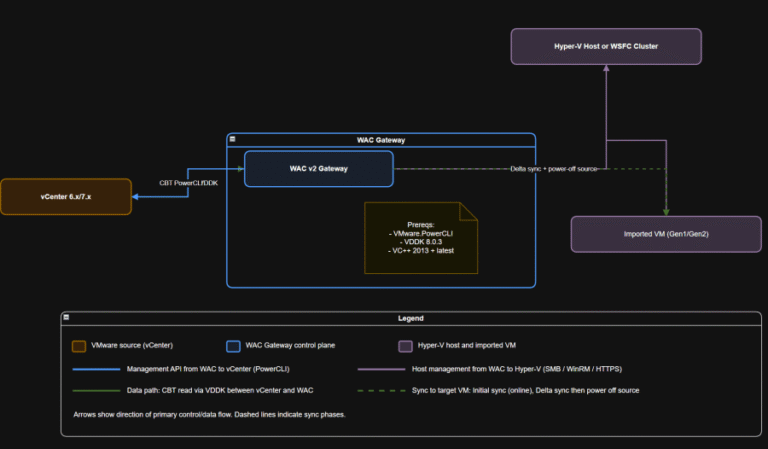
Compliance checkpoints (examples) Why this matters Bridge strategy: If you are standardizing on Windows Server and…
Stopping Breaches with Platform-Native Speed and Expertise With over 100,000 hours of IR casework annually, CrowdStrike…
Security teams today face a data crisis: Exploding volumes of security and IT telemetry are difficult…