MURKY PANDA: A Trusted-Relationship Threat in the Cloud
Since late 2024, CrowdStrike Counter Adversary Operations has observed significant activity conducted by MURKY PANDA, a…
Since late 2024, CrowdStrike Counter Adversary Operations has observed significant activity conducted by MURKY PANDA, a…
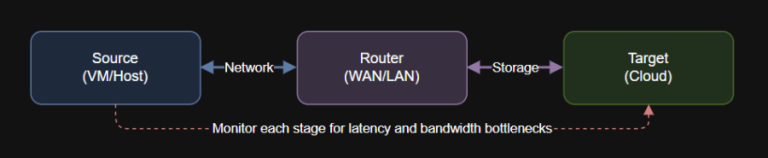
Introduction Data movement in cloud and hybrid architectures is only as fast as your slowest link….
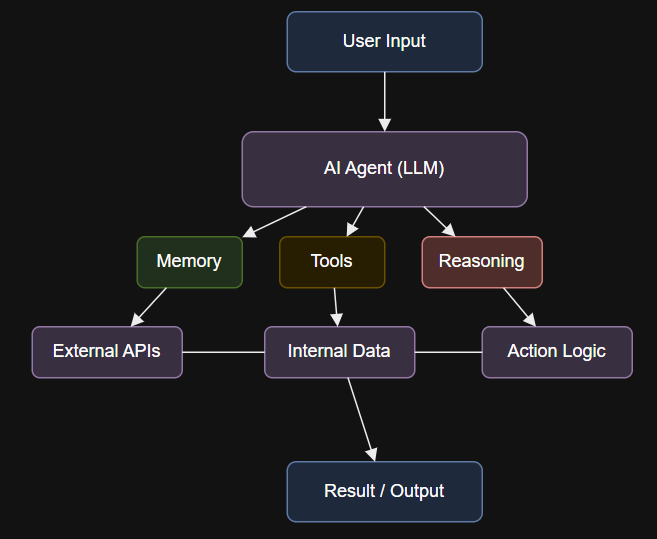
Introduction Run the agent, triggering the entire research and drafting process: What Sets AI Agents Apart?…
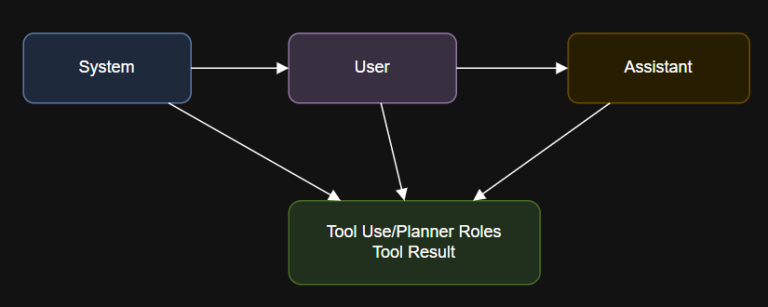
Introduction A simple chat session using system and user roles with an OpenAI-compatible API: In both…
Publicly Disclosed Zero-Day Vulnerability in Windows Kerberos As we have learned with other notable vulnerabilities, such…
“Leakage” in machine learning (ML) occurs when data that an ML model should not learn on…
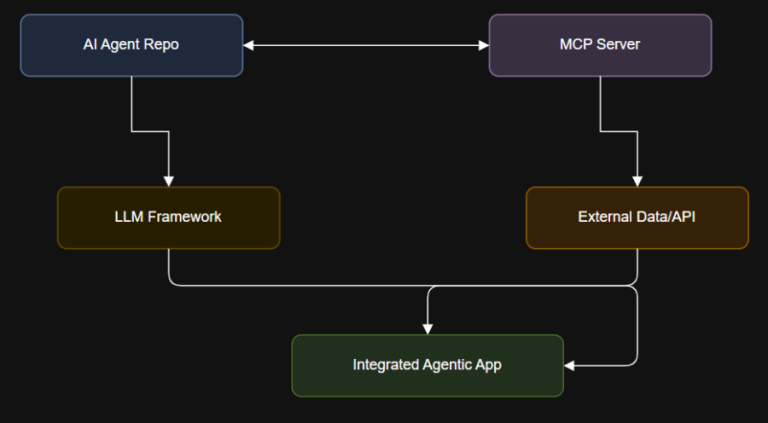
1. Learn AI and LLMs from Scratch Repo: coleam00/ai-agents-masterclassAll code and resources from the AI Agents…
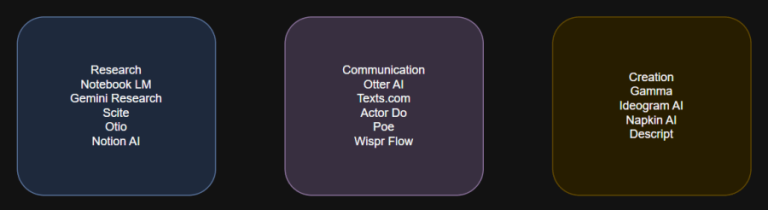
These 15 free AI tools represent the best in practical productivity and innovation for 2025. From…
AI must be deployed strategically in the SOC to outpace AI-savvy adversaries. The Threat Hunting Report…
Today’s enterprising adversaries are weaponizing AI to scale operations, accelerate attacks, and target the autonomous AI…
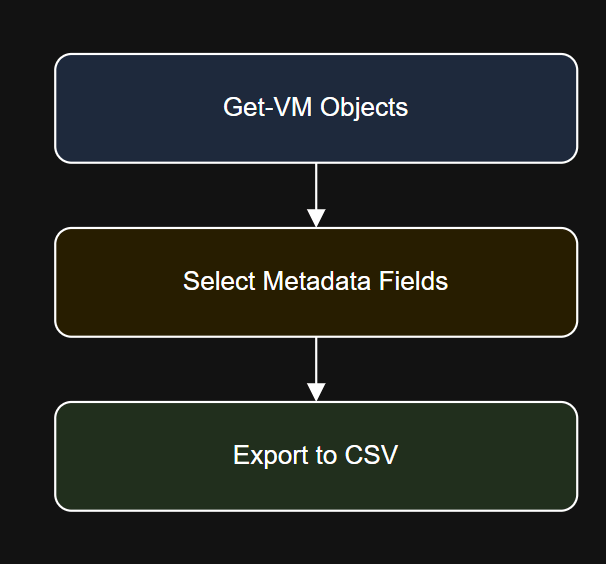
Introduction $timestamp = Get-Date -Format “yyyyMMdd”Export-Csv -Path “C:ReportsVM_Inventory_$timestamp.csv” -NoTypeInformation Step 4: Filter by Folder or Cluster…

There are countless cloud storage platforms that provide safe and secure storage space for your files….
Because Falcon Identity Protection is part of the unified Falcon platform, Mondelēz didn’t have to integrate…

File Transfer Protocol (FTP) was once a widely used method for transferring files or data remotely….
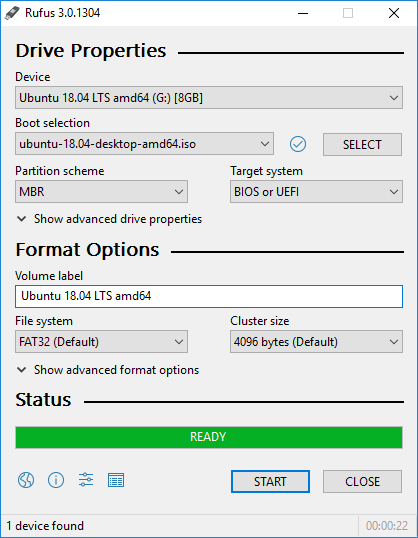
CD and DVD writers are a thing of the past. You are not likely to find…