16 Microsoft Teams Alternatives for Linux Users in 2026
In this guide, we explore the best Microsoft Teams alternatives for Linux that you can use…
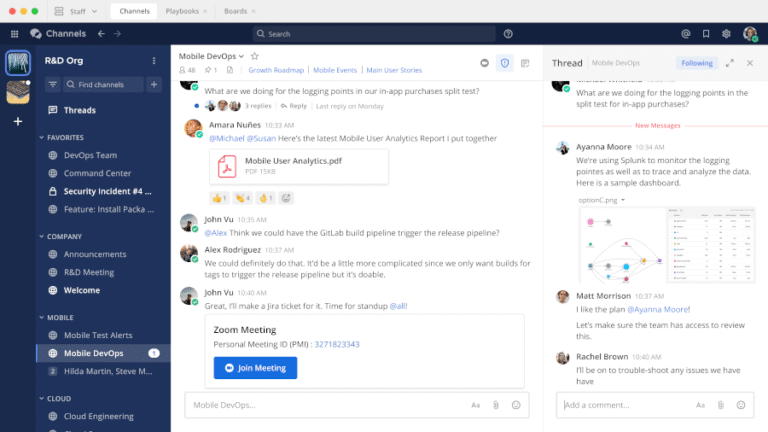
In this guide, we explore the best Microsoft Teams alternatives for Linux that you can use…
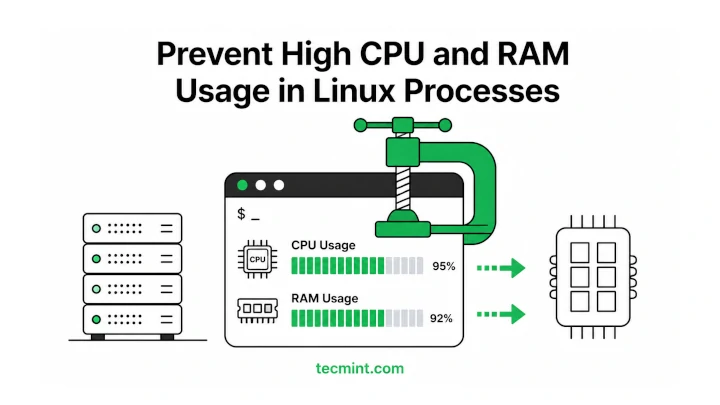
A process suddenly consuming 99% of your CPU at 2 AM can turn a stable server…
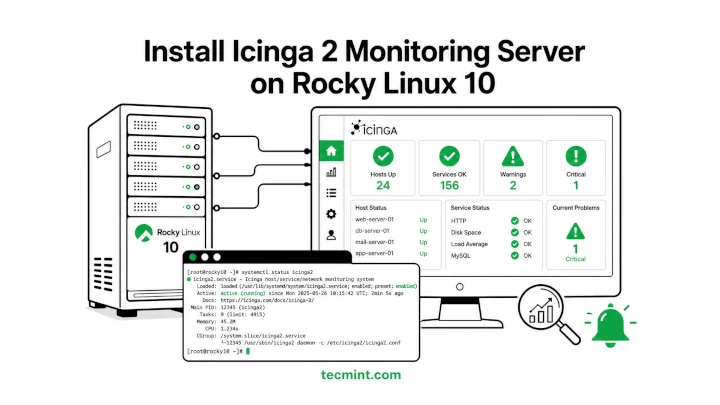
Icinga 2 is a free and open-source monitoring tool that helps you keep an eye on…
After all the configuration is validated and you kick off the workflow, it stops / errors…

Rocky Linux 10 replaced VNC with RDP (Remote Desktop Protocol) for remote graphical installations, so if…
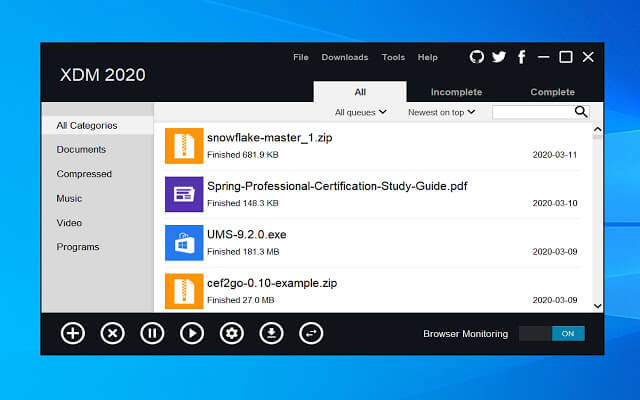
One thing many people miss after switching from Windows to Linux is a good download manager….

CrowdStrike has once again been named a Leader in the 2026 Gartner® Magic Quadrant™ for Endpoint…
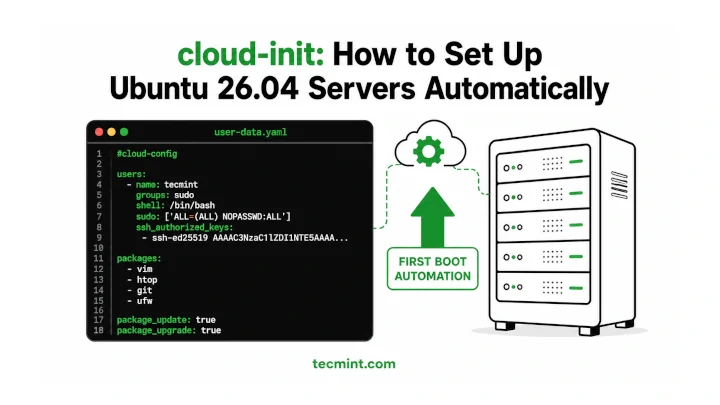
Installing and configuring cloud-init on Ubuntu 26.04 makes it much easier to automate server setup, especially…
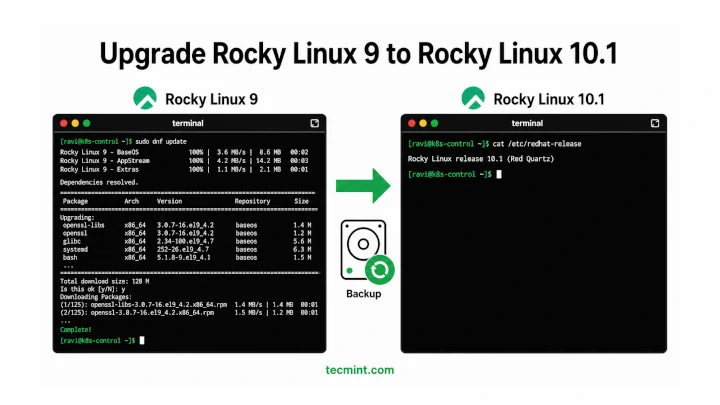
In this article, we’ll show you how to move from Rocky Linux 9 to Rocky Linux…

A self-signed SSL certificate lets you run Apache over HTTPS on Ubuntu 26.04 without buying a…
The analysis emphasizes CrowdStrike’s ability to deliver: Frost & Sullivan has named CrowdStrike its 2026 Company…
What it measures: The percentage of employees using approved AI tools, how frequently they use them,…
AI is among the fastest-growing and most privileged application categories in the enterprise — and one…
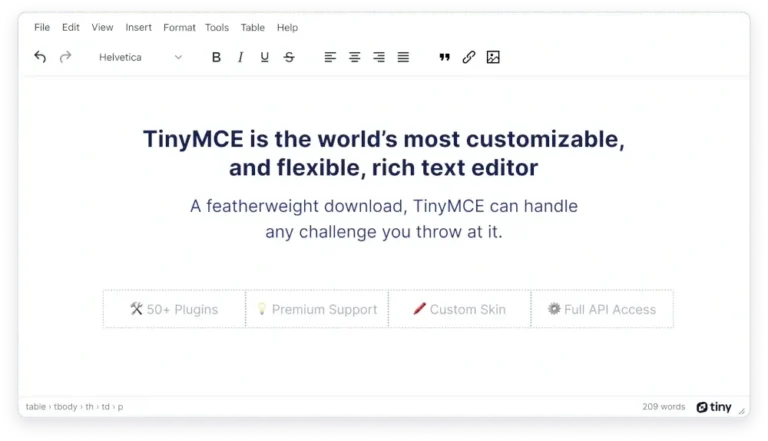
If you’re building a CMS, a documentation portal, or any web app where users type formatted…
Financial LossesThe impact of an infostealer attack can be devastating. Because infostealers quietly extract sensitive data,…