CrowdStrike Scales AI-Native Agents Across Falcon Exposure Management with NVIDIA
Closing the gap between exposure and remediation requires AI that can reason across the entire environment,…
Closing the gap between exposure and remediation requires AI that can reason across the entire environment,…
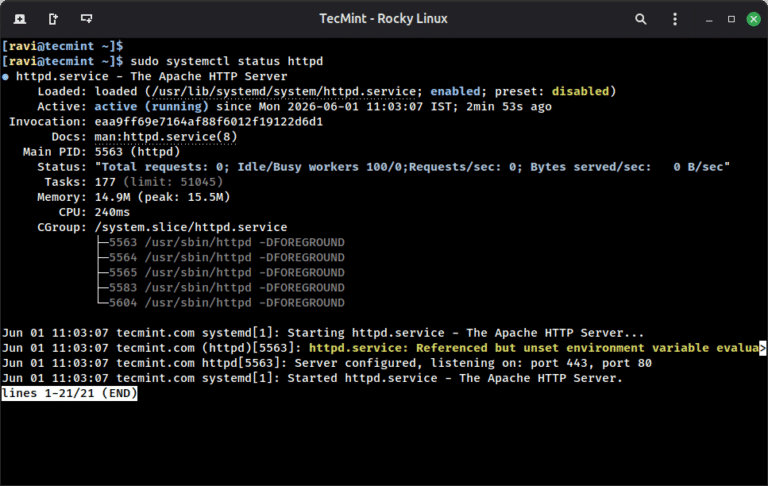
A self-signed SSL certificate lets you run Apache over HTTPS on Rocky Linux 10 without buying…

CrowdStrike has once again been named a Leader in the 2026 Gartner® Magic Quadrant™ for Endpoint…
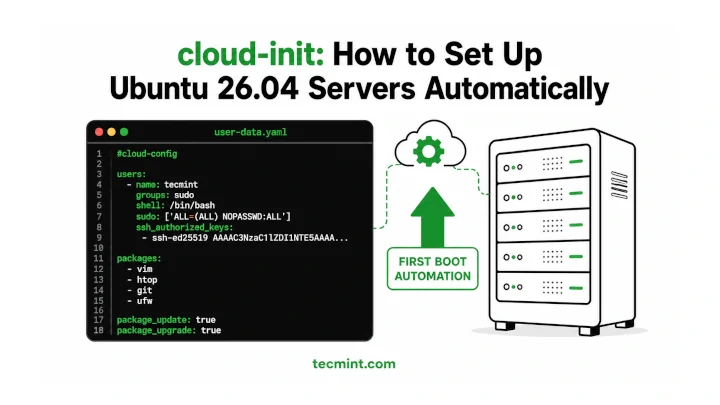
Installing and configuring cloud-init on Ubuntu 26.04 makes it much easier to automate server setup, especially…
Critical Vulnerability in Azure DevOps CVE-2026-33823 is a Critical information disclosure vulnerability affecting the Microsoft Teams…

Threat Intelligence for the AI Era Today’s adversaries are using AI to accelerate their speed, scale,…
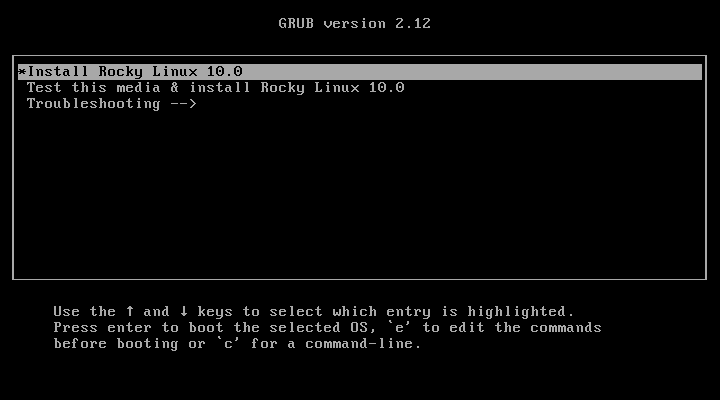
Rocky Linux 10 is the latest stable, community-driven enterprise Linux distribution built as a downstream rebuild…
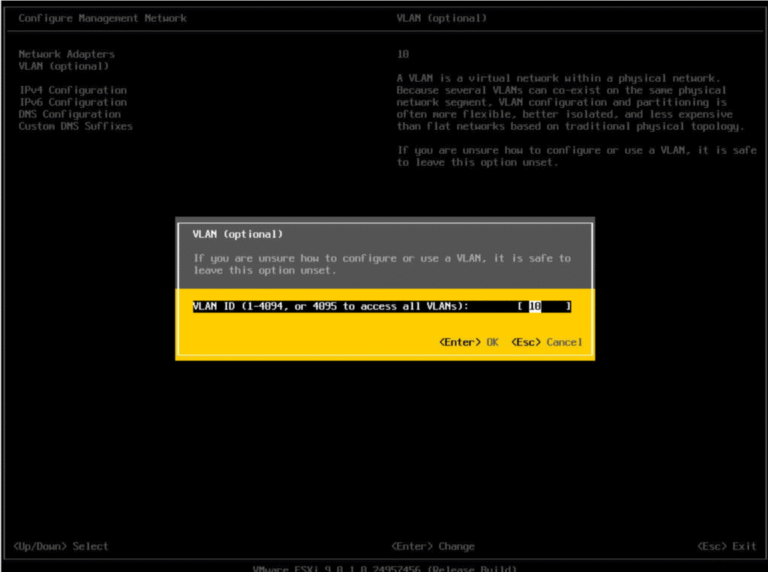
May 5, 2026 Automated Steps For VCF Host Provisioning What Are We Solving Here? As you…
In our Technical Risk Assessments, we consistently find that this external footprint is larger and more…
As discovery becomes faster and more automated, the ability to validate exposure and act on it…
Exploited Zero-Day Vulnerability in Microsoft SharePoint Server CVE-2026-23666 is a Critical denial-of-service (DoS) vulnerability affecting the…
A recommended execution cadence is weekly or monthly to maintain posture awareness and support audit requirements.While…

By correlating runtime application behavior with cloud infrastructure findings, Application Explorer gives organizations a precise view…
This milestone underscores our commitment to protecting the federal government’s most critical systems from modern threats. …

Stopping compromised access at login is essential, but identity risk doesn’t end there. CrowdStrike acquired SGNL…