VCF 9.0 GA Mental Model Part 2: Fleet Services vs Instance Management Planes (and Who Owns What)
TL;DR Practical implication: if fleet services are impaired, governance and workflows degrade, but the instance-level control…
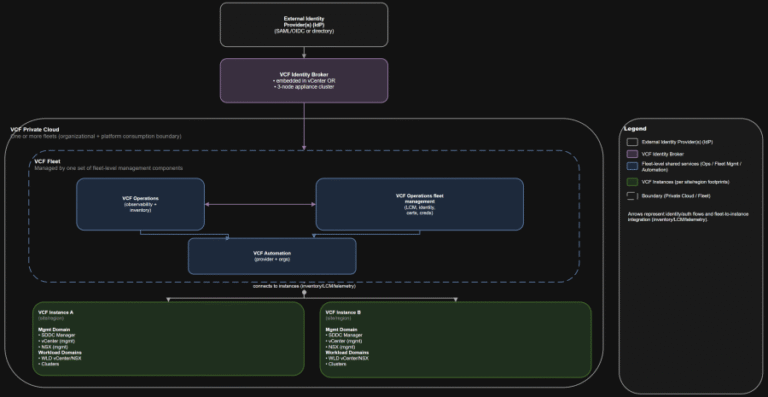
TL;DR Practical implication: if fleet services are impaired, governance and workflows degrade, but the instance-level control…
CrowdStrike Falcon Identity Protection — A Great Tool to Gain Visibility We remain committed to innovating…

Whether you’re building your first automation workflow or exploring how AI can simplify everyday SOC tasks,…
The Human-AI Feedback Loop in Action Expert-Annotated Data Enables Analyst Grade AI 2 Time savings represents…
Actively Exploited Zero-Day Vulnerability in Windows Remote Desktop The vulnerability allows local attackers with no privileges…
– System Engineer, IT Services “Overall, it’s been a valuable and eye-opening experience. The tool has helped…
Indirect prompt injection significantly amplifies this risk by allowing adversaries to influence OpenClaw’s behavior through data…
As part of Falcon Cloud Security’s unified cloud-native application protection platform (CNAPP), Falcon ASPM helps organizations…
SE Labs employed both direct attacks and deep attacks. Test results and the feedback of third-party…
As AI adoption accelerated, WEX® — a global commerce platform that supports business operations primarily for…
As an example, consider a legitimate send_email tool that’s been thoroughly reviewed. An attacker publishes a…
In this guide, we feature some of the best Linux distributions that you can install on…
Christoph Bausewein is Assistant General Counsel for Data Protection and Policy at CrowdStrike.This creates a new…
– System Security Manager, Services (non-Government) IndustryThe truest assessment of the Falcon platform comes from the…
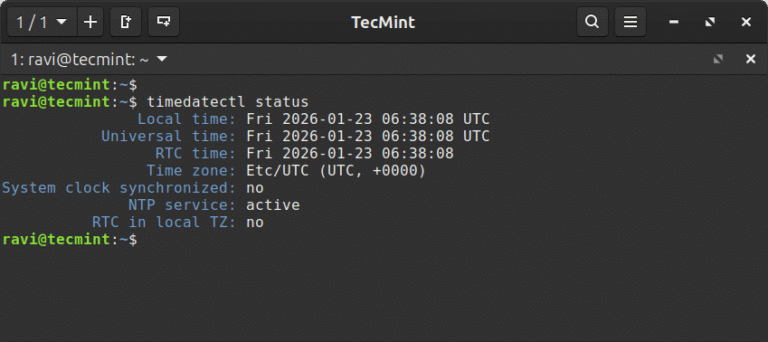
In this article, learn how to set time, timezone, and synchronize your Linux system clock with…