How to Automatically Restart a Service After Failure on SysVinit and Upstart
On systemd-based Linux distributions, managing and restarting services automatically after a failure is relatively straightforward. However,…
On systemd-based Linux distributions, managing and restarting services automatically after a failure is relatively straightforward. However,…
CrowdTour Houston | April 10From New York to Sydney, Dubai to São Paulo, London to Singapore,…
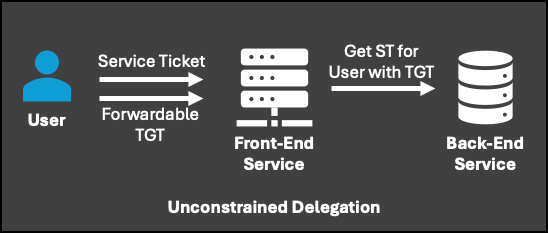
Using Certipy again, the template below would be vulnerable to ESC4.Though 2024 may be behind us,…
The rise of connected devices has fundamentally reshaped industries, enabling unprecedented levels of automation, efficiency, and…
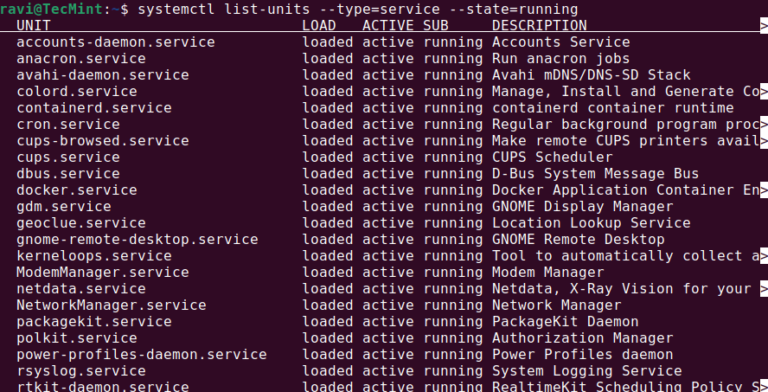
In a Linux system, services (also called daemons) play a critical role in handling various tasks…
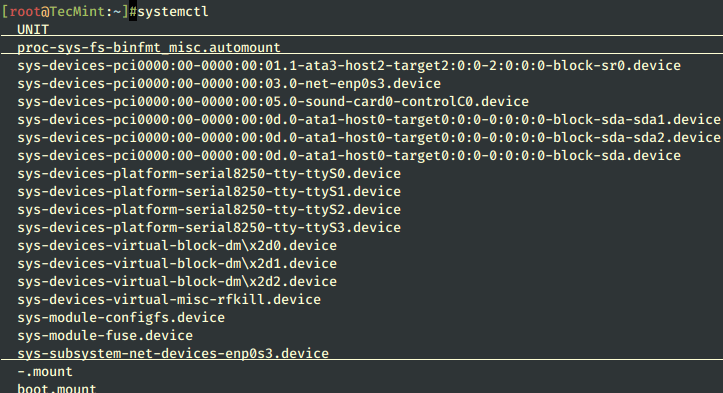
Linux systems provide a variety of system services (such as process management, login, syslog, cron, etc.)…
MangoHud is a powerful and lightweight tool designed for gamers, developers, and anyone who wants to…
Subdomain takeovers are not just about visibility — they provide adversaries with a legitimate-looking platform to…
The aforementioned processes would likely take weeks or even months when totaling hundreds of terabytes and…
Actively Exploited Zero-Day Vulnerability in Microsoft Management Console Microsoft Management Console received a patch for CVE-2025-26633,…
“By moving to Falcon Complete, we saw a drop in our operational expense on cybersecurity by…
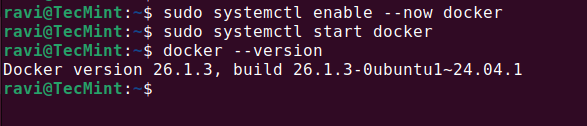
Managing Docker containers using the command line can be challenging, especially for beginners, which is why…
1. Initial Entry and Exploitation After gaining initial access, the adversary moved laterally through the network…
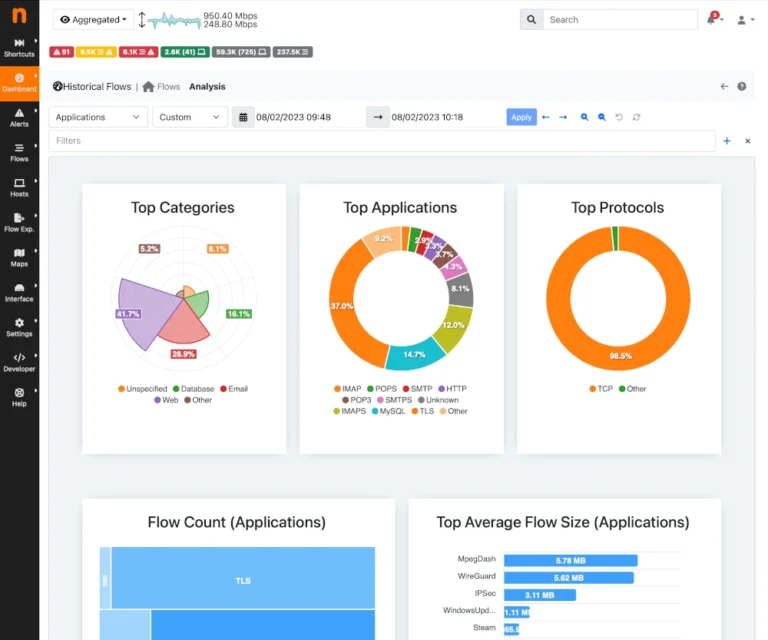
Network bandwidth monitoring is essential for system administrators to track data usage, analyze traffic patterns, and…
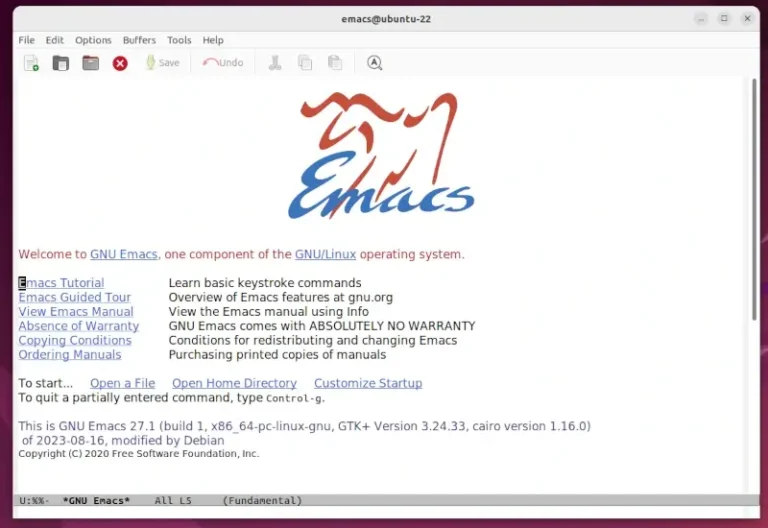
GNU Emacs is one of the oldest text editors. It was created by Richard Stallman, the…