How the CrowdStrike Falcon Platform Drove the Germany-Singapore Team to Success at NATO Locked Shields 2025
The Germany-Singapore team was composed of experts from the German Bundeswehr, Singapore’s Digital and Intelligence Service…
The Germany-Singapore team was composed of experts from the German Bundeswehr, Singapore’s Digital and Intelligence Service…
SCATTERED SPIDER, an eCrime adversary, has recently broadened its target scope to include the aviation sector,…
Organizations in the expanding healthcare ecosystem are under mounting pressure to balance business growth, regulatory compliance,…
Today, I’m going to show you a simple but effective way to automatically block suspicious IPs…
If you’ve spent any time managing Linux systems, you already know how repetitive and time-consuming some…
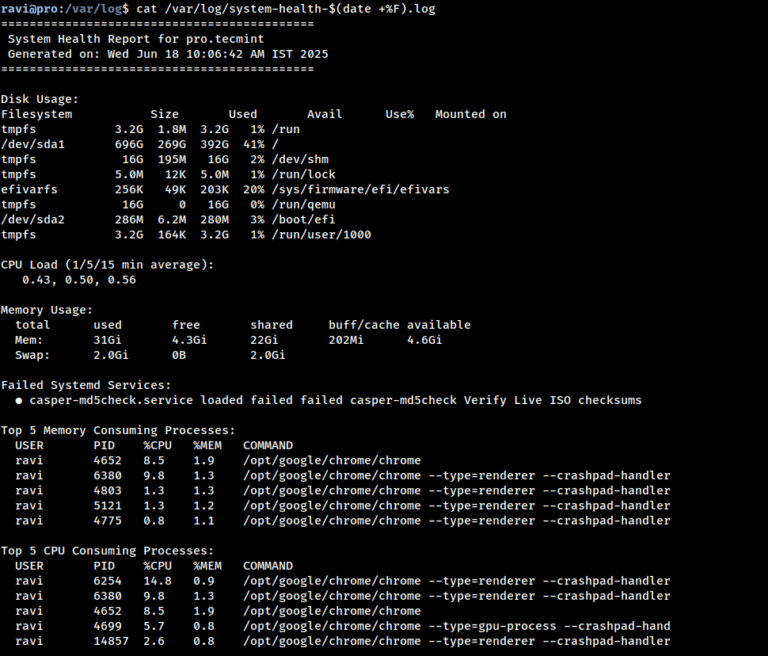
Managing Linux servers daily can be fun and stressful, especially when you’re dealing with unexpected downtimes…
However, the memory patching approach is quite noisy from an attacker perspective because it can raise…
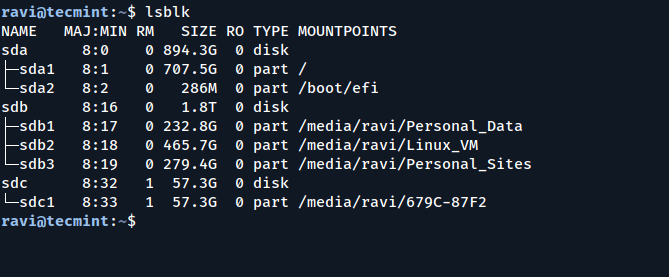
If you’ve ever plugged in a USB stick on a Linux machine and found that you…
Actively Exploited Zero-Day Vulnerability in Web Distributed Authoring and Versioning While exploitation requires the attacker to…
Today’s adversaries have their sights set on identities. They’re using stolen credentials and social engineering techniques…
Today, CrowdStrike and Microsoft announced a strategic alliance to bring clarity and coordination to the way…
CrowdStrike has enhanced ExPRT.AI, our Expert Prediction Rating AI model, with XIoT-specific asset and adversary context…

FTP stands for File Transfer Protocol and is one of the most widely used and standard…
Adversary-driven approach: GigaOm praised CrowdStrike’s adversary-centric approach to identity security: “Utilizing threat intelligence, it enriches alerts…
Introduction Effective collaboration is essential when confronting today’s sophisticated cyber adversaries, particularly those operating with state…