cloud-init: How to Set Up Ubuntu 26.04 Servers Automatically
Installing and configuring cloud-init on Ubuntu 26.04 makes it much easier to automate server setup, especially…
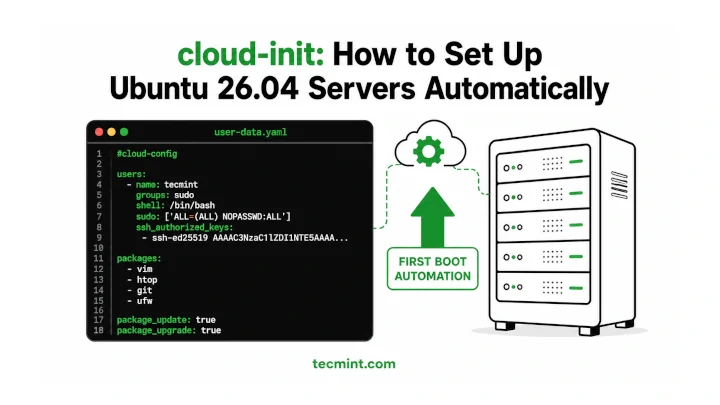
Installing and configuring cloud-init on Ubuntu 26.04 makes it much easier to automate server setup, especially…

Netplan is the default network configuration tool on Ubuntu since 18.04, replacing the older ifupdown system…

A self-signed SSL certificate lets you run Apache over HTTPS on Ubuntu 26.04 without buying a…
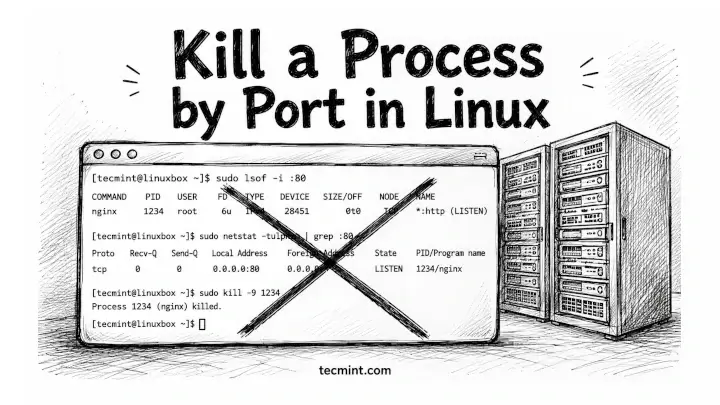
You’ve got a server refusing to start because something’s already sitting on port 8080, and you…
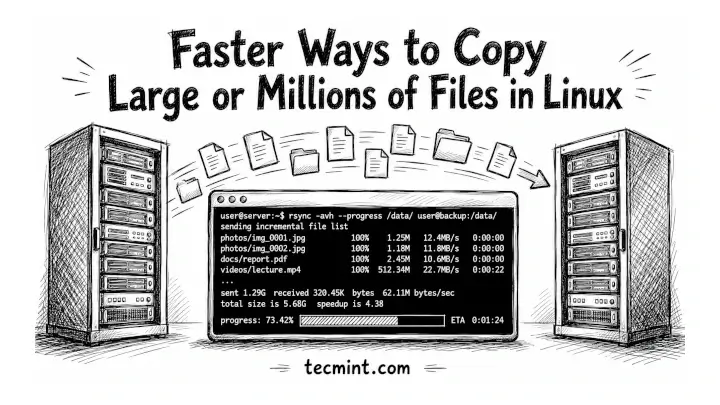
You’ve been copying files with cp for years, and if you’re moving a 50GB backup or…
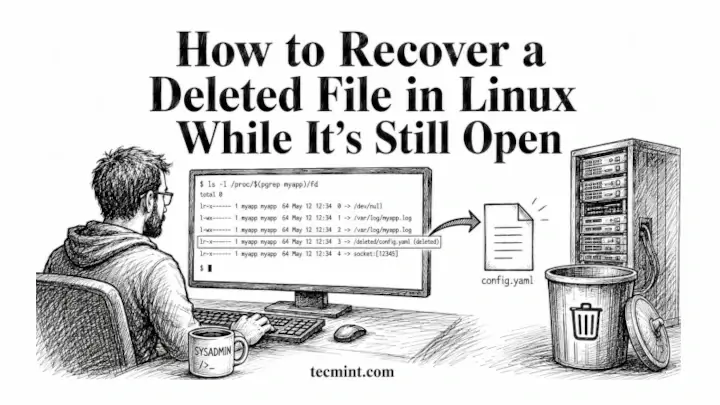
You deleted a log file mid-session, a running process is still writing to it, and ls…
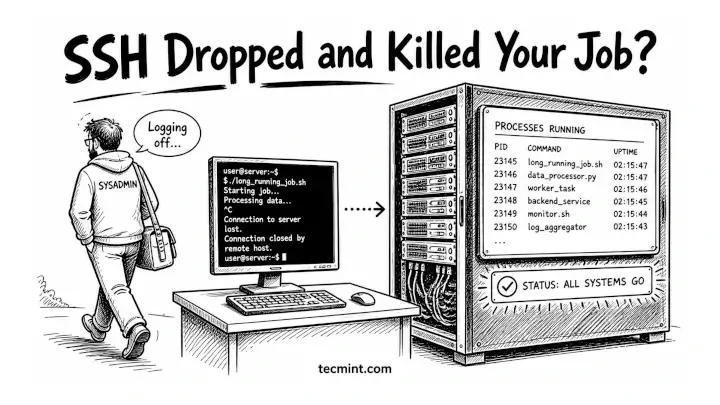
You’ve been running a long rsync job or a Python script on a remote server only…
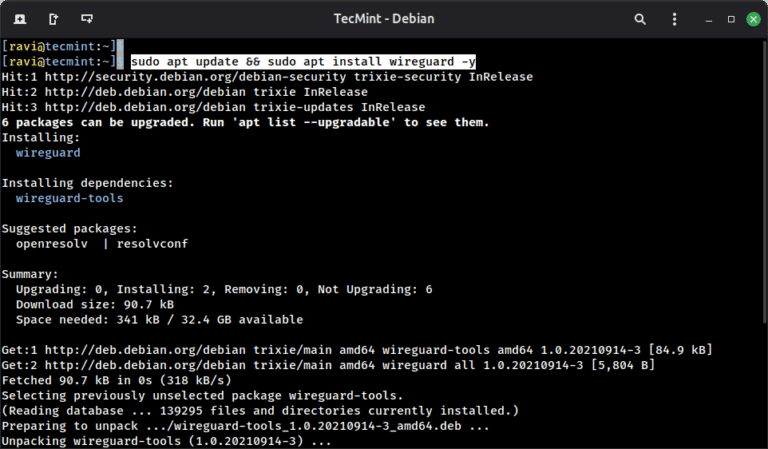
WireGuard is a modern VPN protocol built directly into the Linux kernel since version 5.6, and…
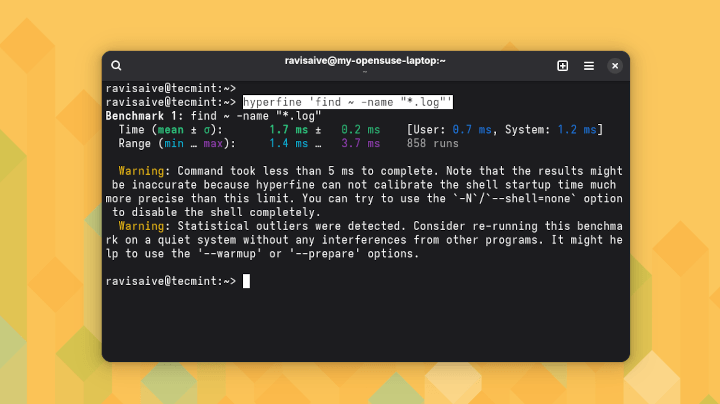
hyperfine is a command-line benchmarking tool that runs your commands repeatedly, collects timing data across multiple…
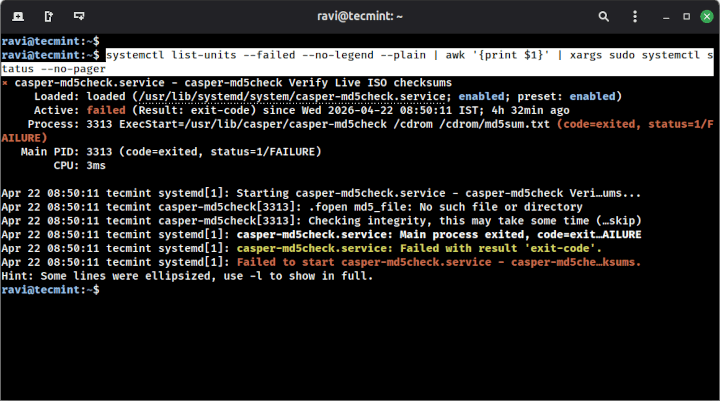
Learn how to use systemctl with the –failed flag to instantly spot broken services on your…
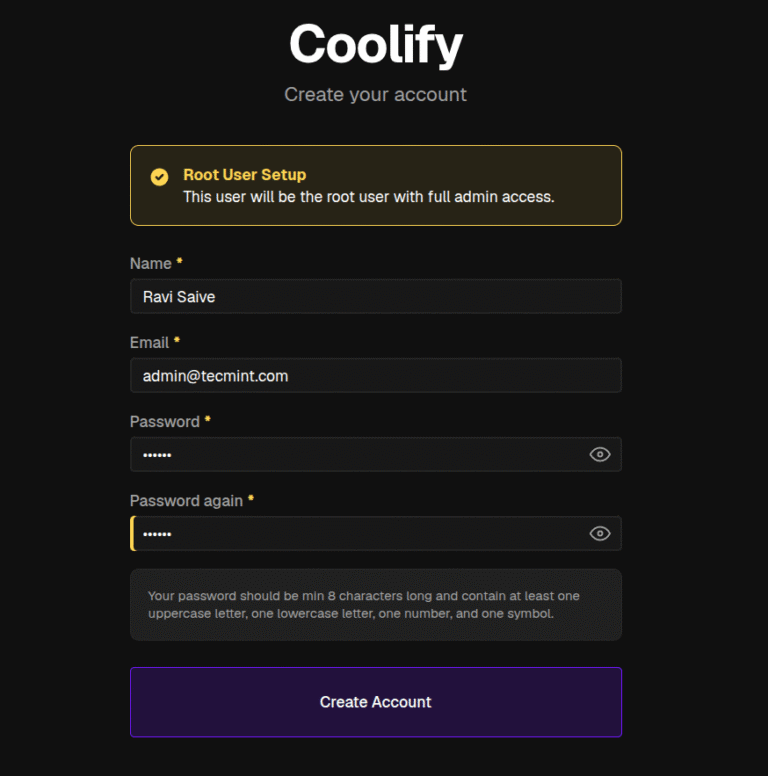
Coolify is an open-source, self-hosted platform that deploys web apps, databases, and services on your own…
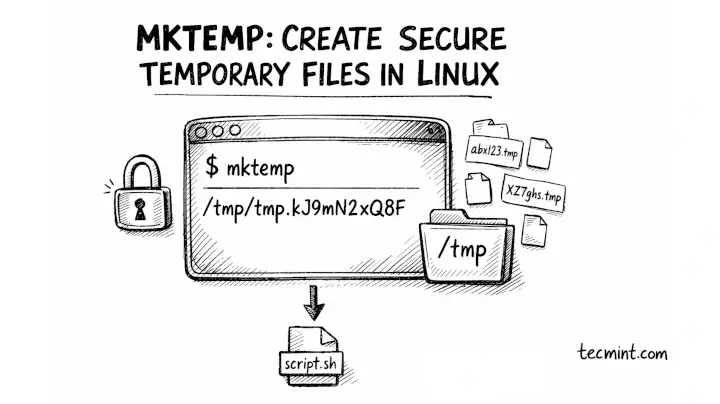
The mktemp command in Linux creates temporary files and directories with unique, unpredictable names, which is…
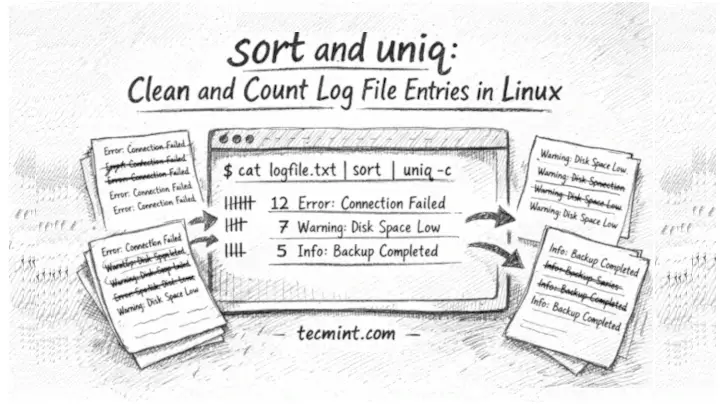
In this guide, we’ll show you how to use sort and uniq together to deduplicate, count,…
A recommended execution cadence is weekly or monthly to maintain posture awareness and support audit requirements.While…
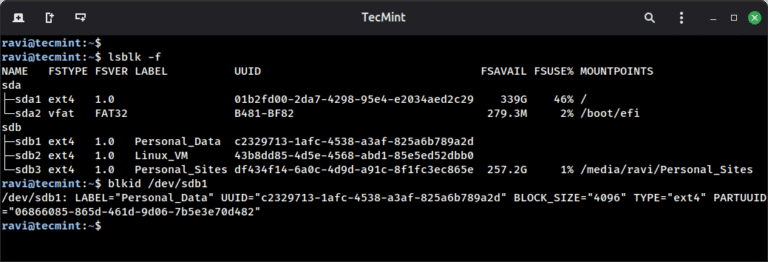
Linux filesystems are responsible for organizing how data is stored and retrieved. Over time – due…