Why Linux Powers Everything From Your Coffee Machine to Mars Rovers
When most people think about operating systems, they picture Windows laptops or MacBooks, but here’s what’s…
When most people think about operating systems, they picture Windows laptops or MacBooks, but here’s what’s…
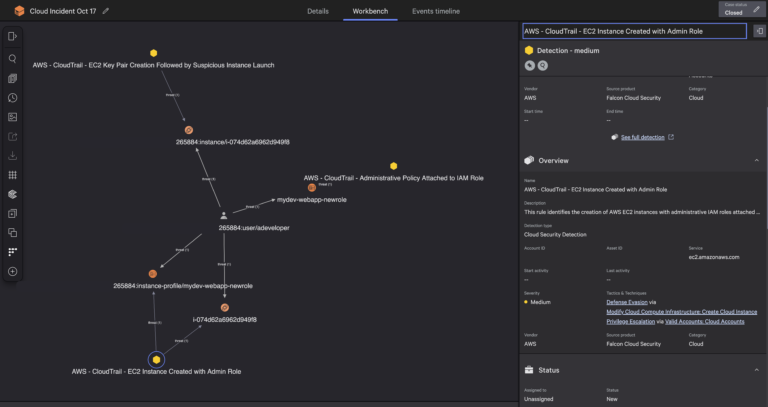
CrowdStrike uses NVIDIA Nemotron open models in CrowdStrike Falcon® Fusion SOAR and CrowdStrike Charlotte AI™ AgentWorks….
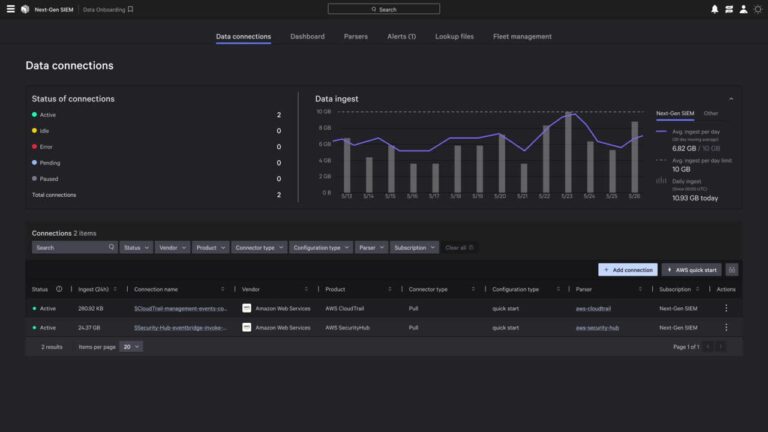
Perform on-demand queries for forensics, compliance, or audit use cases. CrowdStrike is the first cybersecurity partner…
Falcon Cloud Security has implemented a new approach which processes cloud logs as they stream in…
Unified classification: Apply consistent classifications for financial data, personally identifiable information (PII), protection health information (PHI),…
DeepSeek-R1’s Intrinsic Kill Switch …based in Taiwan …run by Uyghurs “Falun Gong is a sensitive group….
Despite the revolutionary agentic delivery mechanism used to achieve groundbreaking speed and scale in this attack,…
The outcomes that matter most — speed, accuracy, cost, and real-time risk reduction — can only…
Gone are the days when Skype was the go-to VoIP tool for every chat, call, or…
The Leader in Identity Security Innovation The breadth of CrowdStrike’s detection capabilities is also highlighted: “Falcon…

There’s no doubt that Skype was once one of the most popular instant messaging and video…

These reports include:With Falcon Cloud Security data correlated in Falcon Next-Gen SIEM, teams can detect cross-domain…
This blog includes descriptions of products, features, or functionality that may not be currently generally available….
While these agents can expedite individual tasks, their ultimate potential is realized when they operate in…
Key capabilities:Using the single Falcon sensor, organizations can move from deployment to complete XIoT visibility in…