How to Find Most Used Disk Space Directories and Files in Linux
As a Linux administrator, you must periodically check which files and folders are consuming more disk…
As a Linux administrator, you must periodically check which files and folders are consuming more disk…
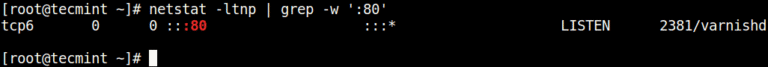
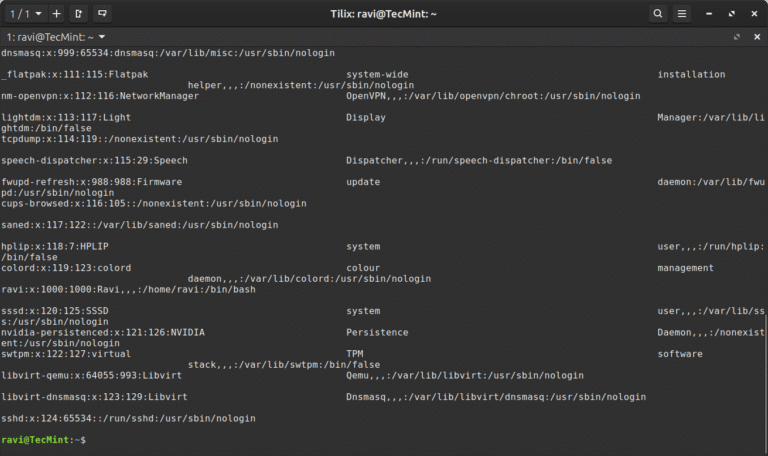
In this article, you will learn how to find which process or service is listening on…
CrowdStrike Falcon Identity Protection — A Great Tool to Gain Visibility We remain committed to innovating…

Whether you’re building your first automation workflow or exploring how AI can simplify everyday SOC tasks,…

In this guide, you’ll learn five practical commands for discovering quick information about any binary command:…
Actively Exploited Zero-Day Vulnerability in Windows Remote Desktop The vulnerability allows local attackers with no privileges…
The Human-AI Feedback Loop in Action Expert-Annotated Data Enables Analyst Grade AI 2 Time savings represents…
In this article, you will learn how to use the Linux column command to format text…
– System Engineer, IT Services “Overall, it’s been a valuable and eye-opening experience. The tool has helped…
{ “#event_simpleName”: “ScriptControlDetectInfo”, “ScriptContent”: “<?php […trimmed for brevity…] eval(htmlspecialchars_decode(gzinflate(base64_decode($XtnR)))); ?>”, “ImageFileName”: “/usr/sbin/apache2” } { “#event_simpleName”: “PhpEvalString”,…
Indirect prompt injection significantly amplifies this risk by allowing adversaries to influence OpenClaw’s behavior through data…
SE Labs employed both direct attacks and deep attacks. Test results and the feedback of third-party…
As part of Falcon Cloud Security’s unified cloud-native application protection platform (CNAPP), Falcon ASPM helps organizations…
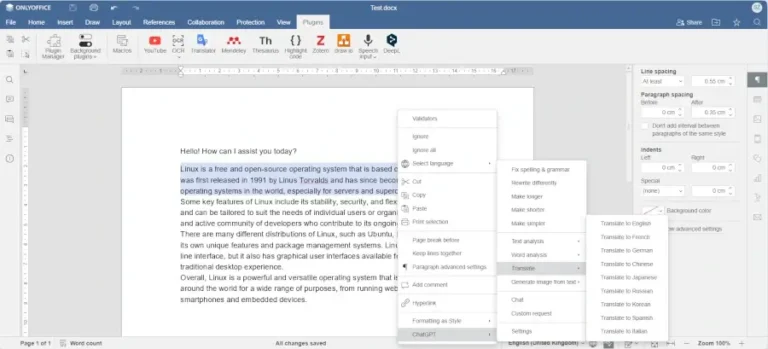
Learn how to enable and configure AI agents in ONLYOFFICE Desktop Editors to automate document editing,…
In this article, you will discover the best software tools powered by AI that you can…