Falcon Platform for Government Now Offers Falcon for XIoT to Secure Connected Assets
This milestone underscores our commitment to protecting the federal government’s most critical systems from modern threats. …
This milestone underscores our commitment to protecting the federal government’s most critical systems from modern threats. …
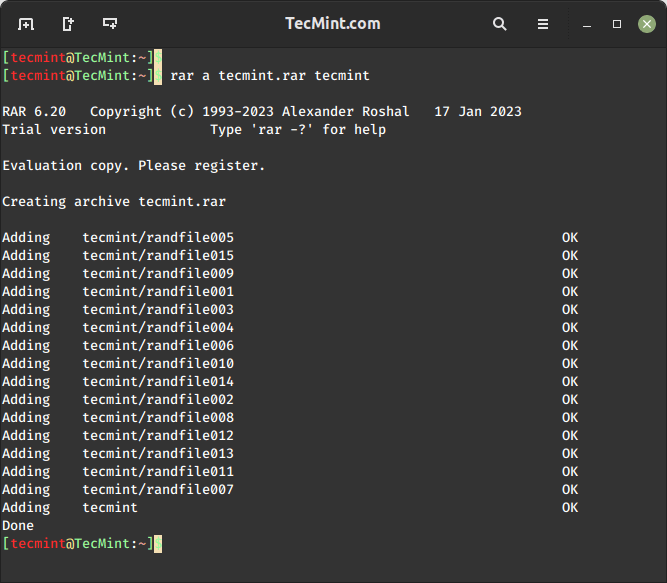
RAR files, a common compressed file format, are widely used to store and share large amounts…
To help merchants meet modern checkout expectations, Volusion Payments powered by Stripe* is Volusion’s preferred payment…
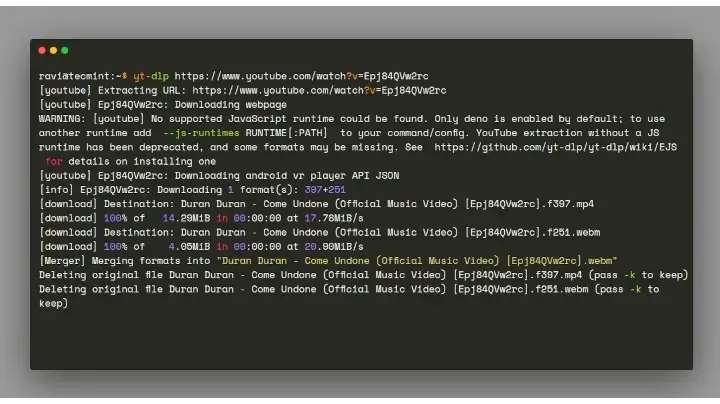
We all love listening to music and watching videos, whether it’s at the gym, at work,…
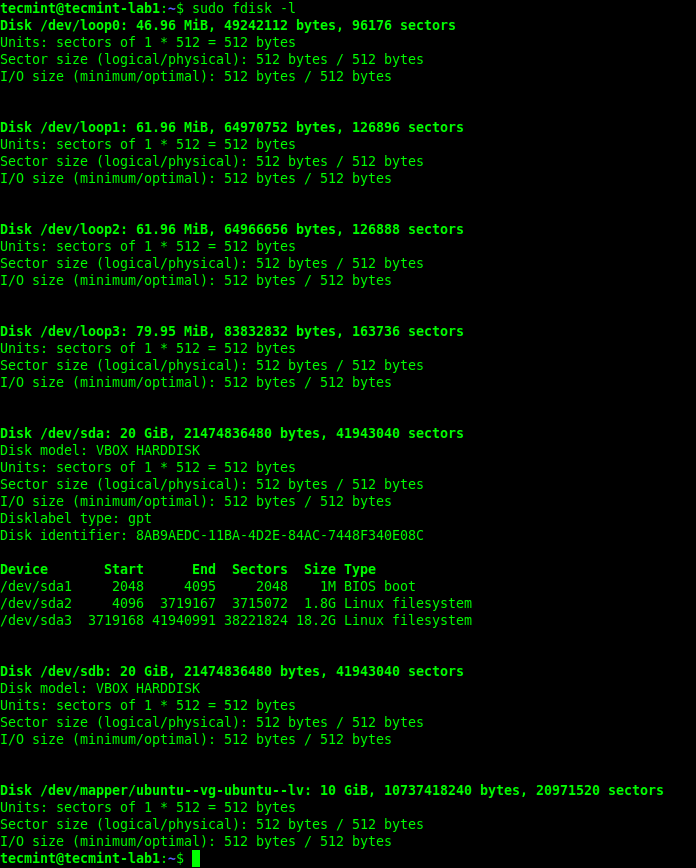
Whether you’re troubleshooting boot issues, preparing to format a drive, or setting up a new disk,…
Security analysts were spending the majority of their time on what leadership described as mechanical analysis….
There are several ways to find out which version of Linux you’re running on your system,…
SOCKS5 At launch, Enhanced Network Visibility will support parsing of plaintext HTTP requests and responses and…
Critical Vulnerability in Microsoft Devices Pricing Program CVE-2026-23651 and CVE-2026-26124 are Critical elevation of privilege vulnerabilities…
Detect Exposures and Prioritize Threats to Connected Medical Devices The lightweight Falcon sensor will use threat…
The log collector itself focuses exclusively on ingesting third-party and external log data, complementing native CrowdStrike…
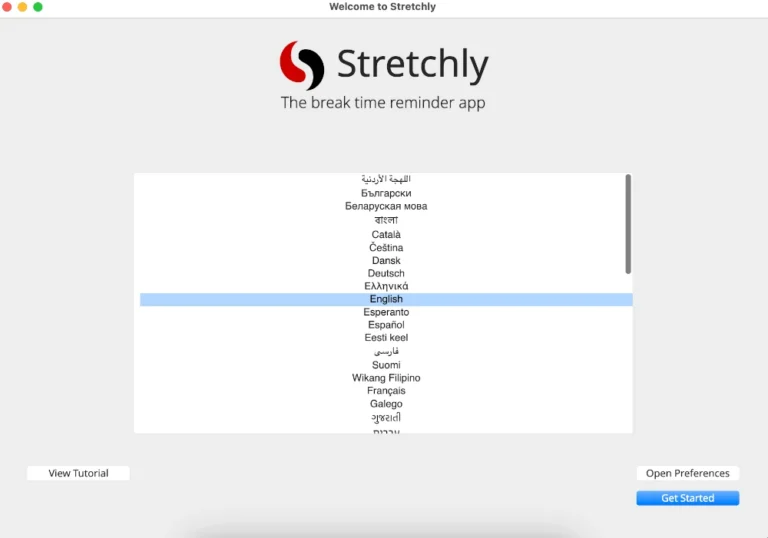
In this article, you will discover 3 excellent break reminder apps for Linux that help prevent…
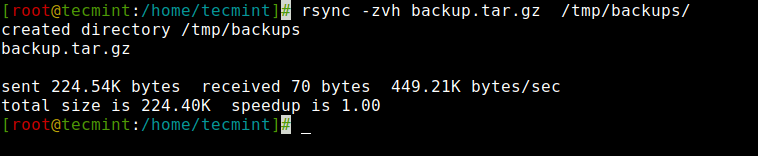
In this article, you will learn how to copy, sync, backup, and transfer files locally and…
This milestone comes as the UK places increased emphasis on cyber resilience, operational assurance, and incident…

Stopping compromised access at login is essential, but identity risk doesn’t end there. CrowdStrike acquired SGNL…