VCF 9.0 GA Mental Model Part 3: Day-0 to Day-2 Ownership Across Fleets, Instances, and Domains
TL;DR A) One fleet, one instance, stretched where justified In VCF 9.0, identity is not a…
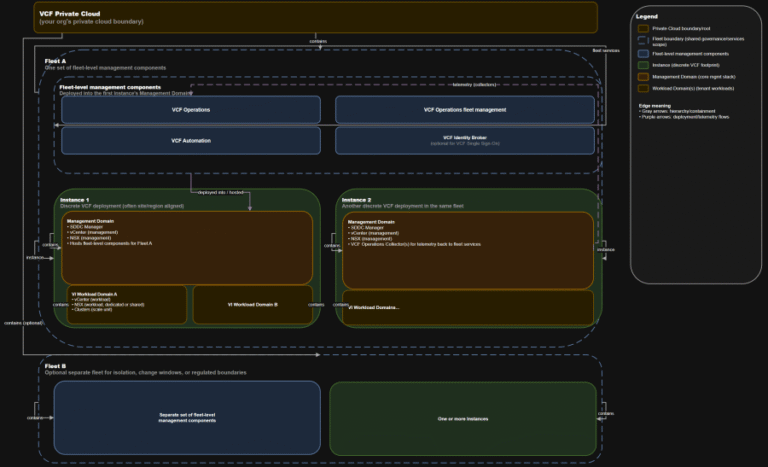
TL;DR A) One fleet, one instance, stretched where justified In VCF 9.0, identity is not a…
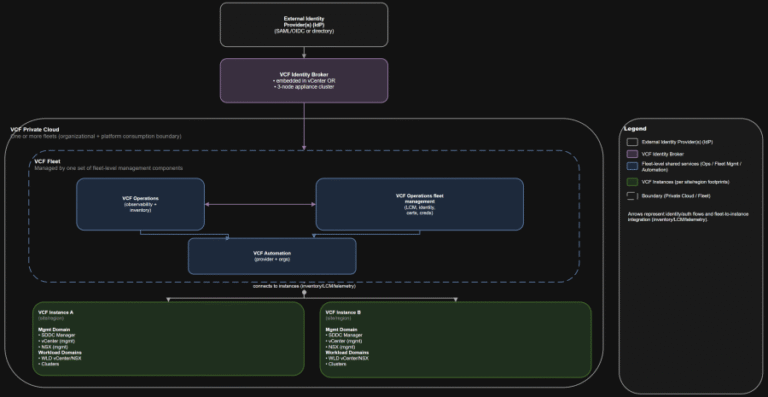
TL;DR Practical implication: if fleet services are impaired, governance and workflows degrade, but the instance-level control…
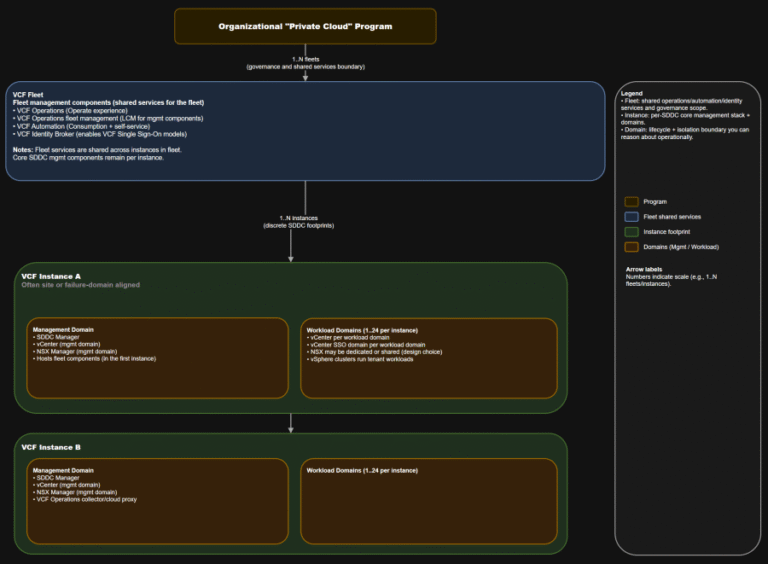
TL;DR This is the “where do we do the thing” map you want in every runbook….
Actively Exploited Zero-Day Vulnerability in Windows Remote Desktop The vulnerability allows local attackers with no privileges…
SE Labs employed both direct attacks and deep attacks. Test results and the feedback of third-party…
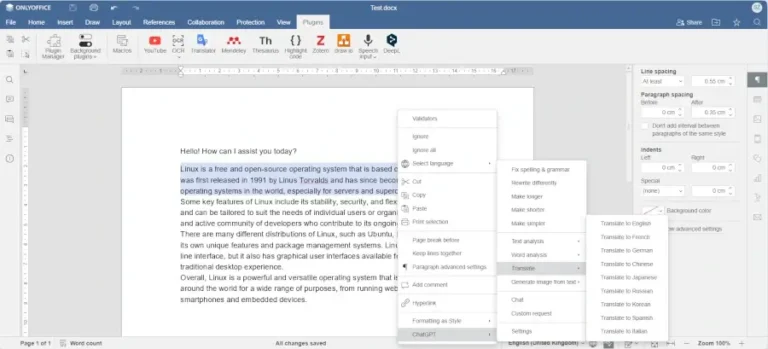
In this article, you will discover the best software tools powered by AI that you can…
GOLDEN CHOLLIMA Shared infrastructure elements and tool cross-pollination indicate these units maintain close coordination. All three…
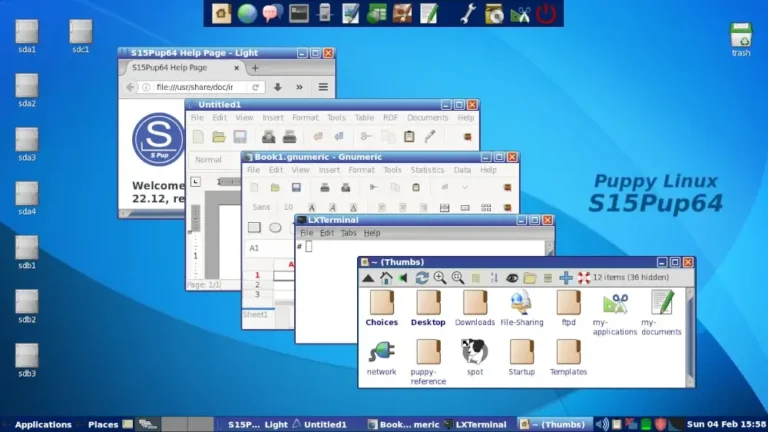
In this guide, we feature some of the best Linux distributions that you can install on…
– System Security Manager, Services (non-Government) IndustryThe truest assessment of the Falcon platform comes from the…
Actively Exploited Zero-Day Vulnerability in Windows Desktop Window Manager CVE-2026-20955 and CVE-2026-20957 are Critical remote code…
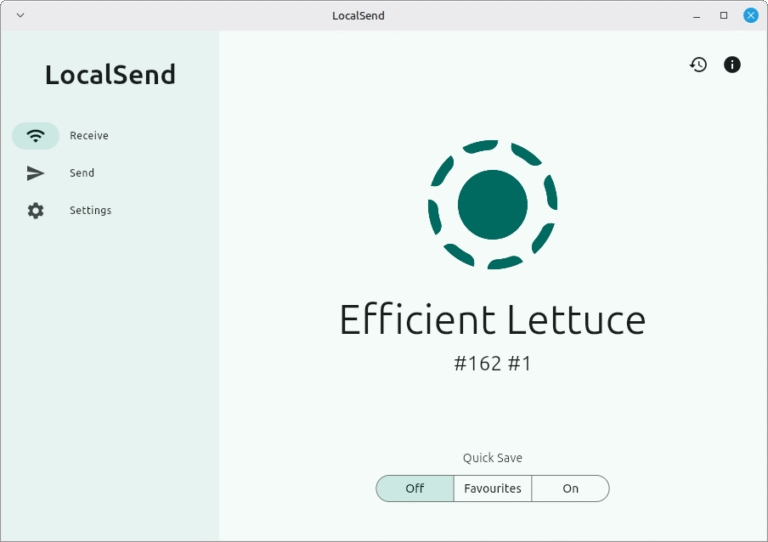
One of the most important uses of a network is for file sharing purposes, and there…
Zero-Day Vulnerability in Windows Cloud Files Mini Filter Driver The CrowdStrike Falcon platform regularly collects and…
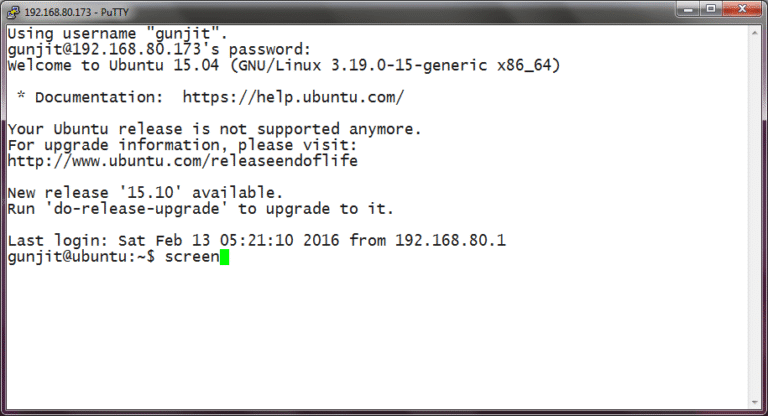
SSH or Secure Shell in simple terms is a way by which a person can remotely…
When most people think about operating systems, they picture Windows laptops or MacBooks, but here’s what’s…
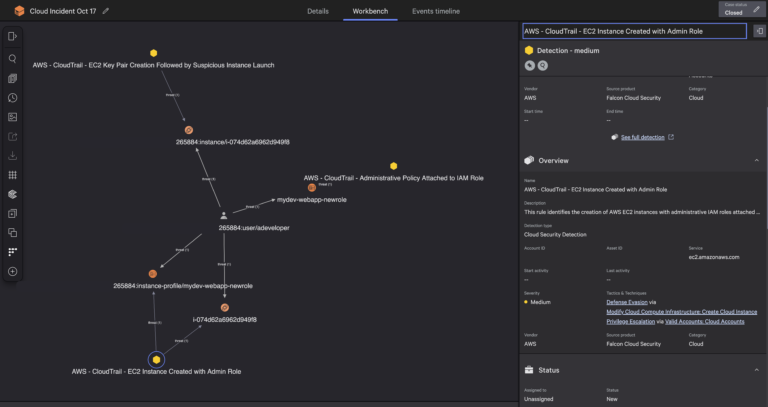
Falcon Cloud Security has implemented a new approach which processes cloud logs as they stream in…