16 Microsoft Teams Alternatives for Linux Users in 2026
In this guide, we explore the best Microsoft Teams alternatives for Linux that you can use…
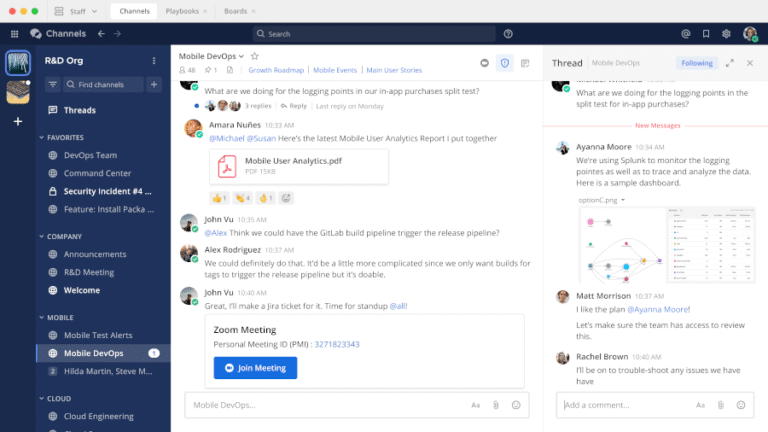
In this guide, we explore the best Microsoft Teams alternatives for Linux that you can use…
For example, teams can identify when sensitive data such as PII appears within a pipeline, even…
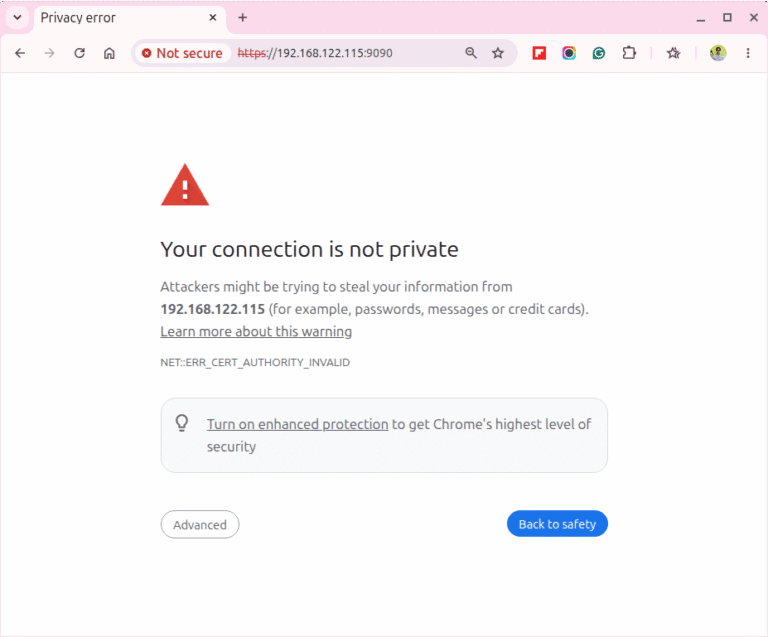
Cockpit ships pre-installed on Rocky Linux 10 and gives you a browser-based dashboard for managing your…

Rocky Linux 10 replaced VNC with RDP (Remote Desktop Protocol) for remote graphical installations, so if…
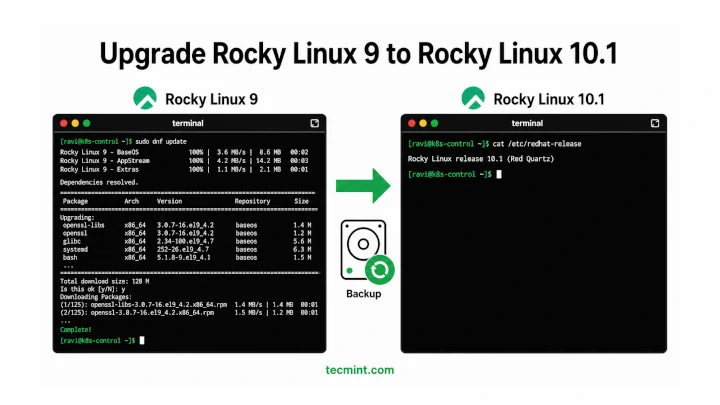
In this article, we’ll show you how to move from Rocky Linux 9 to Rocky Linux…
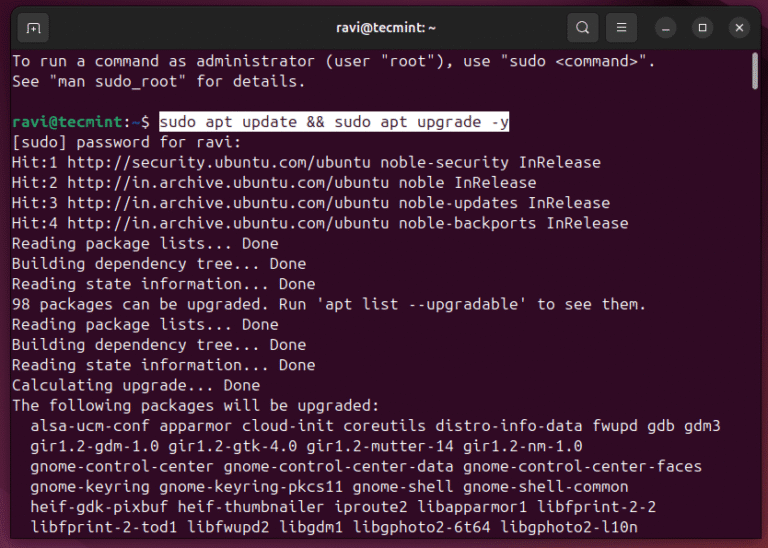
Ubuntu 26.04 LTS “Resolute Raccoon” shipped on April 23, 2026, and if you’re still on 24.04,…
Financial LossesThe impact of an infostealer attack can be devastating. Because infostealers quietly extract sensitive data,…
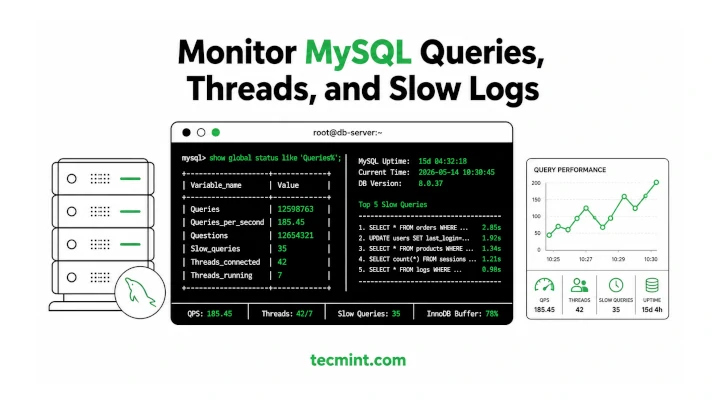
MySQL ships with decent built-in diagnostics, but when your database is slowing down under load, you…
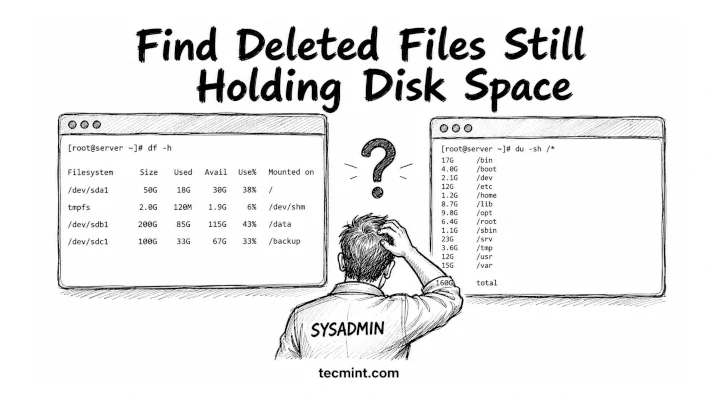
df says your disk is 80% full, but du says you’re barely using half, so one…
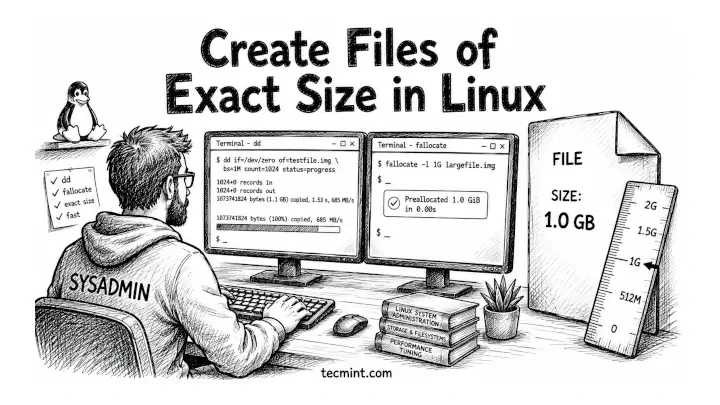
You need a 1GB test file to benchmark your disk, fill a partition to a specific…
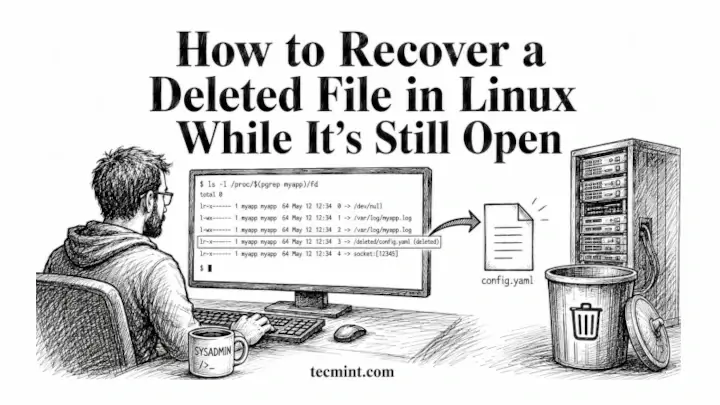
You deleted a log file mid-session, a running process is still writing to it, and ls…
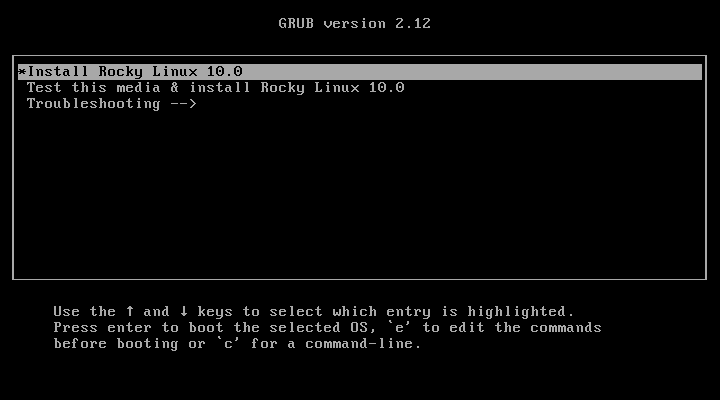
Rocky Linux 10 is the latest stable, community-driven enterprise Linux distribution built as a downstream rebuild…
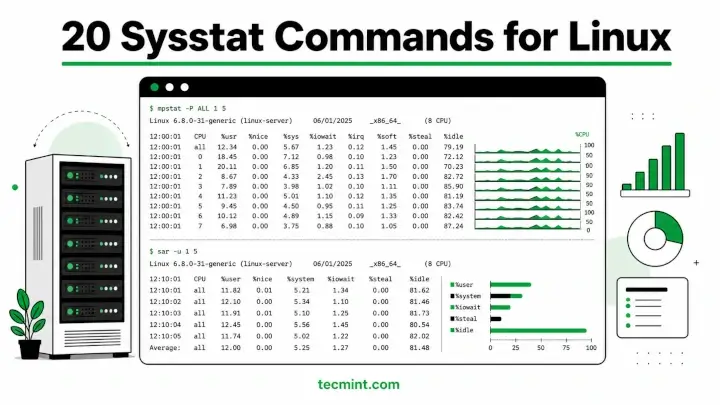
Sysstat is a collection of performance monitoring utilities for Linux that includes mpstat, pidstat, iostat, and…
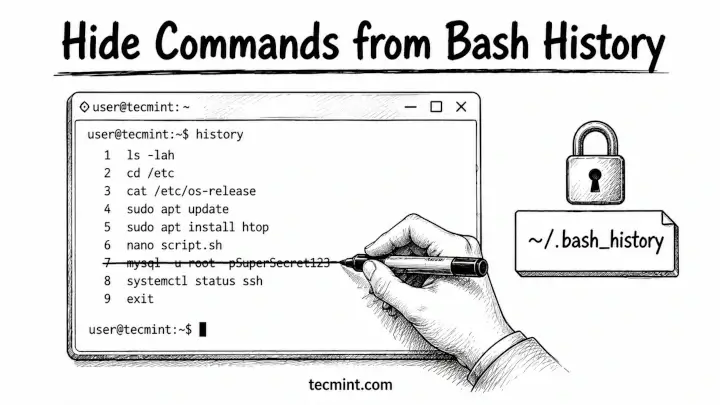
Every Linux user eventually runs a command they’d rather not preserve – a curl with a…
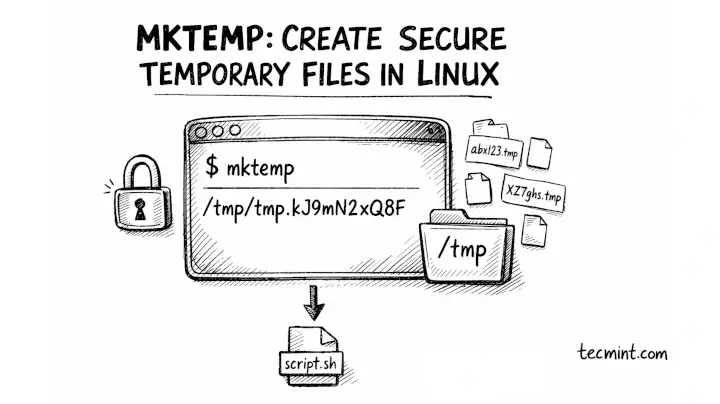
The mktemp command in Linux creates temporary files and directories with unique, unpredictable names, which is…