Flexible by Design: Why Ecommerce Platforms Must Adapt to Merchants
What often gets overlooked is how rarely those early platform choices evolve with the business. What…
What often gets overlooked is how rarely those early platform choices evolve with the business. What…
When a high-profile vulnerability is disclosed, teams need to move quickly and with confidence in the…
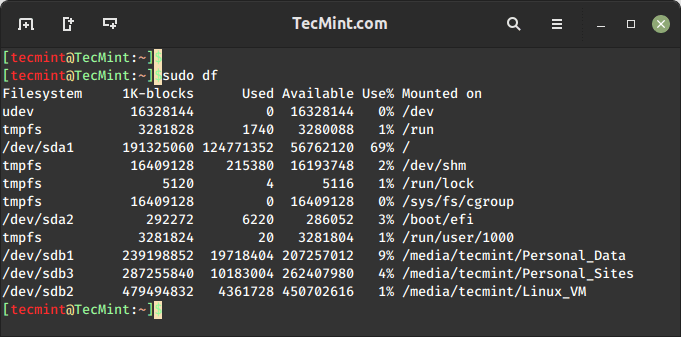
On the internet, you will find plenty of tools for checking disk space usage in Linux….
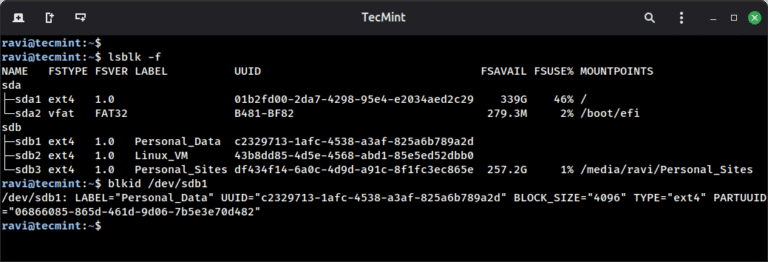
Linux filesystems are responsible for organizing how data is stored and retrieved. Over time – due…

Legacy SIEMs, fragmented toolchains, and manual workflows cannot keep up with the scale and complexity of…
An initial spike on Linux platforms linked to runners was observed on March 19, 2026. The…
Falcon AIDR and its corresponding API enable teams to create named detection policies tailored to their…
This milestone underscores our commitment to protecting the federal government’s most critical systems from modern threats. …
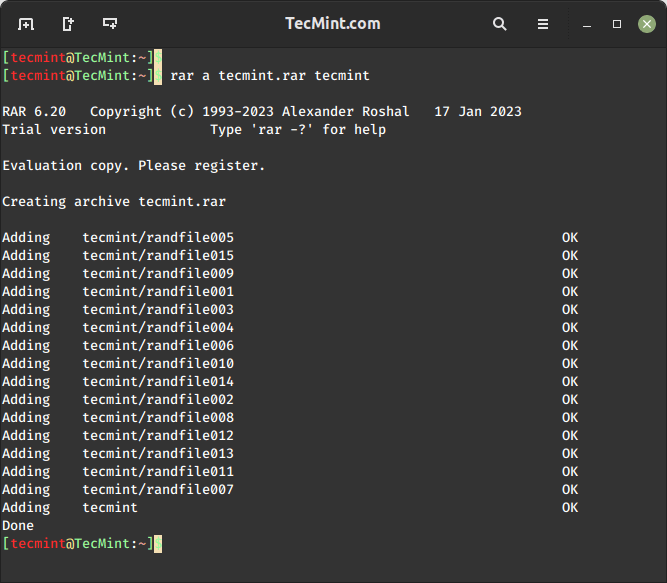
RAR files, a common compressed file format, are widely used to store and share large amounts…
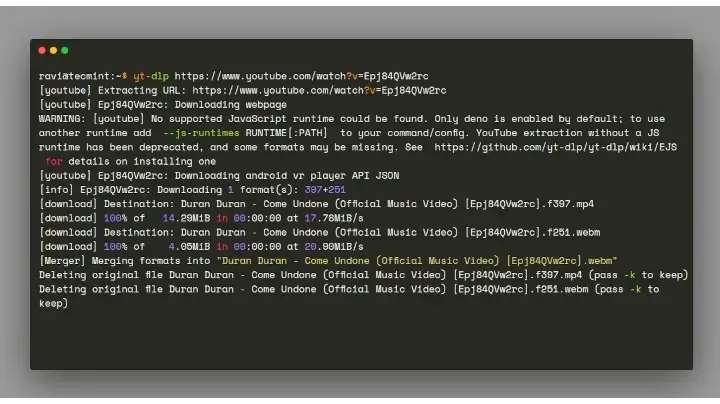
We all love listening to music and watching videos, whether it’s at the gym, at work,…
There are several ways to find out which version of Linux you’re running on your system,…
Critical Vulnerability in Microsoft Devices Pricing Program CVE-2026-23651 and CVE-2026-26124 are Critical elevation of privilege vulnerabilities…
Detect Exposures and Prioritize Threats to Connected Medical Devices The lightweight Falcon sensor will use threat…
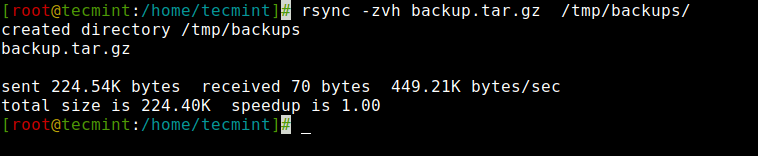
In this article, you will learn how to copy, sync, backup, and transfer files locally and…
This milestone comes as the UK places increased emphasis on cyber resilience, operational assurance, and incident…