Secure AI at Machine Speed: Defending the Growing Attack Surface
Core Technology that Powers Security for AI Data remains the primary target for adversaries, but traditional…
Core Technology that Powers Security for AI Data remains the primary target for adversaries, but traditional…
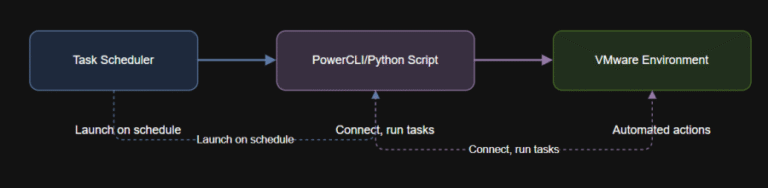
Learning Objectives By the end of this article, you will: Schedule PowerCLI and Python scripts for…
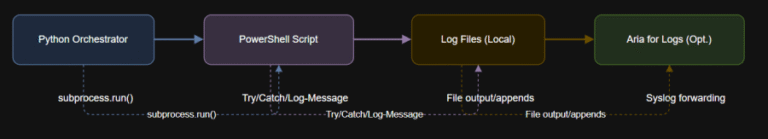
Learning Objectives Below is a PowerShell script that wraps key actions in error handling and logs…
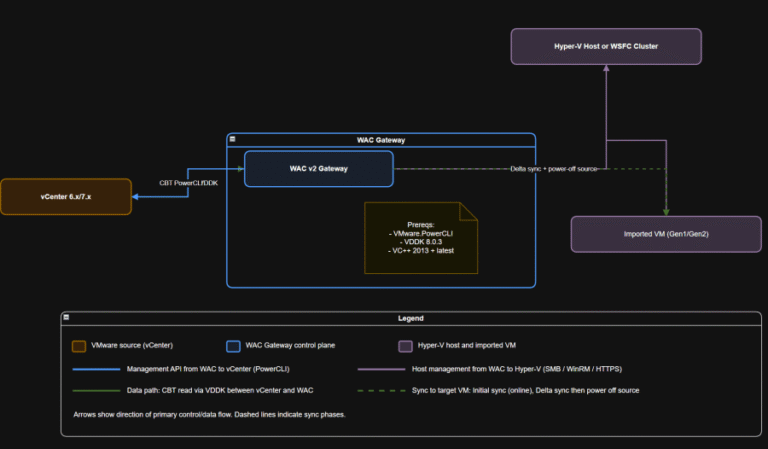
Compliance checkpoints (examples) Why this matters Bridge strategy: If you are standardizing on Windows Server and…
Set-PowerCLIConfiguration -InvalidCertificateAction Ignore -Scope Session VMware Repository on GitHub Step 1: Install PowerShellWindows 10/11 comes with…
A Leader in Exposure Management The report notes, “Network-based vulnerability scanning was recently added to the…
Since late 2024, CrowdStrike Counter Adversary Operations has observed significant activity conducted by MURKY PANDA, a…
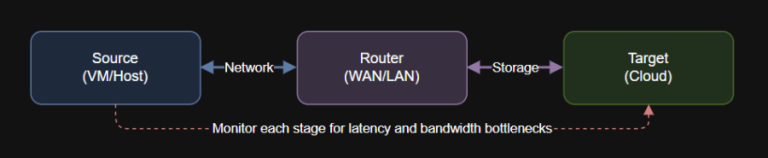
Introduction Data movement in cloud and hybrid architectures is only as fast as your slowest link….

Introduction A global retailer must store EU customer data within European borders to comply with GDPR….
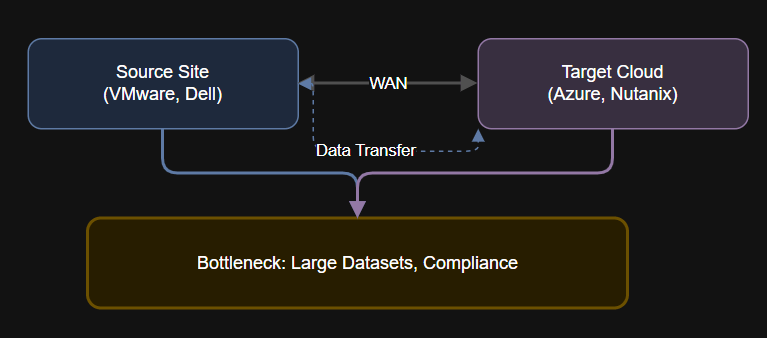
Introduction Even the best-planned cloud and hybrid migrations can be derailed by data gravity. When large…
Publicly Disclosed Zero-Day Vulnerability in Windows Kerberos As we have learned with other notable vulnerabilities, such…
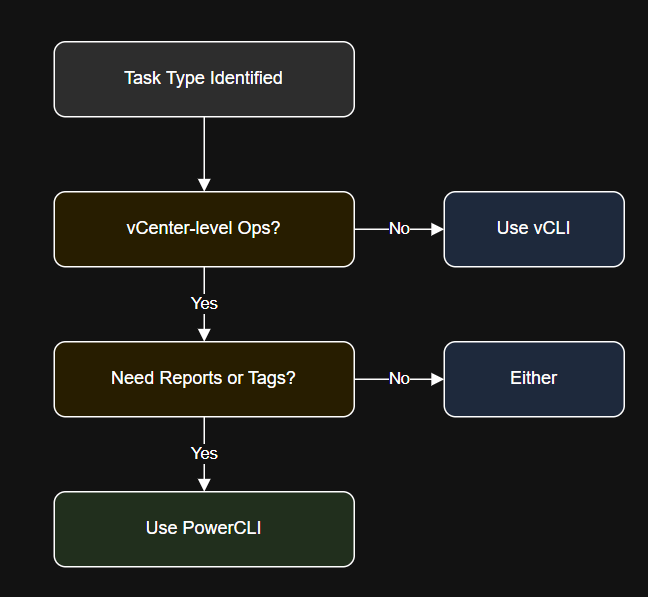
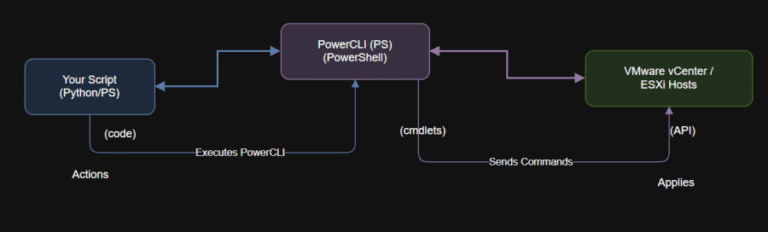
Introduction In this article, you’ll learn: Install using VMware downloads or use the VMA (vSphere Management…
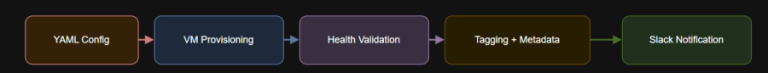
Introduction – name: Enterprise Nutanix VM Provisioninghosts: localhostgather_facts: falsecollections:- nutanix.ncpvars_files:- nutanix_credentials.yml- enterprise_vm_config.ymlvars:slack_webhook: “https://hooks.slack.com/services/XXXX/YYYY/ZZZZ”tasks:TASK [Check VM health]ok:…

File Transfer Protocol (FTP) was once a widely used method for transferring files or data remotely….
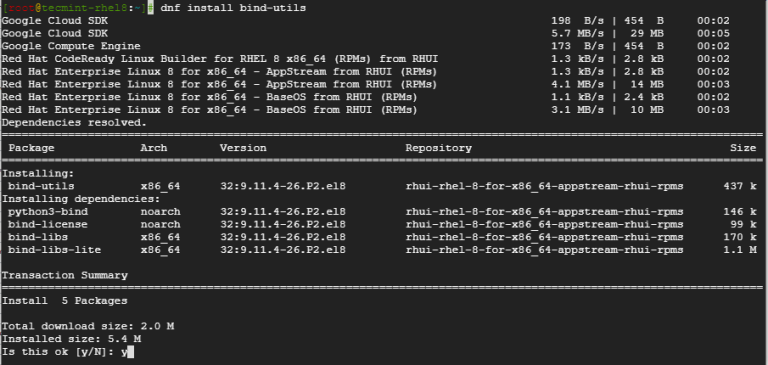
If you’re working with networks, managing domains, or troubleshooting connectivity issues, two essential tools you’ll come…