15 Useful “ifconfig” Commands to Configure Network Interface in Linux
In this article, you will learn how to list, configure, enable, disable, and troubleshoot network interfaces…
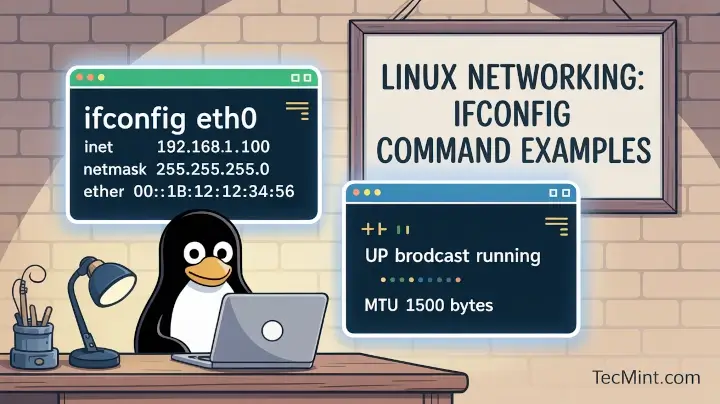
In this article, you will learn how to list, configure, enable, disable, and troubleshoot network interfaces…
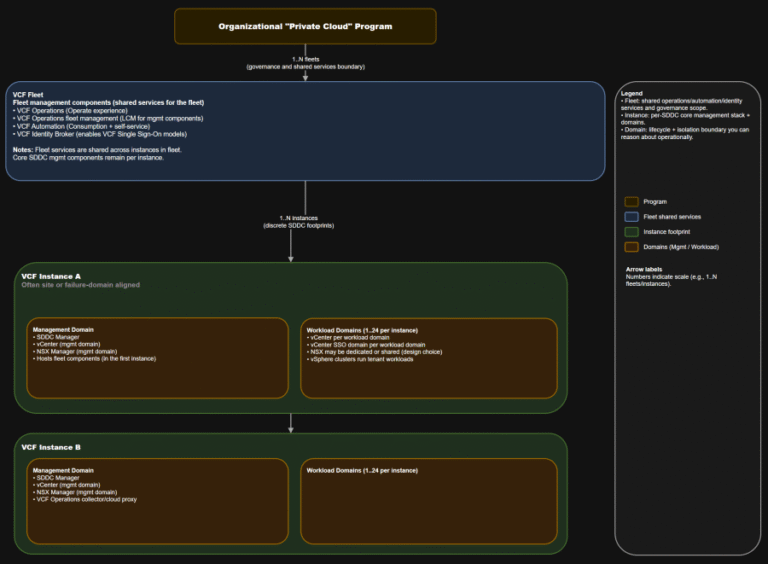
TL;DR This is the “where do we do the thing” map you want in every runbook….
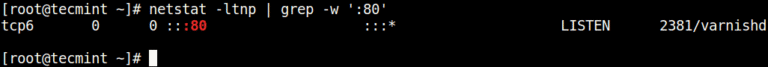
In this article, you will learn how to find which process or service is listening on…
Actively Exploited Zero-Day Vulnerability in Windows Remote Desktop The vulnerability allows local attackers with no privileges…
– System Engineer, IT Services “Overall, it’s been a valuable and eye-opening experience. The tool has helped…
Indirect prompt injection significantly amplifies this risk by allowing adversaries to influence OpenClaw’s behavior through data…
SE Labs employed both direct attacks and deep attacks. Test results and the feedback of third-party…
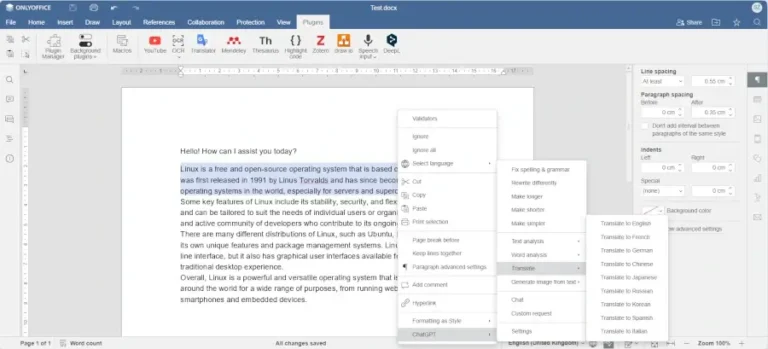
In this article, you will discover the best software tools powered by AI that you can…
As AI adoption accelerated, WEX® — a global commerce platform that supports business operations primarily for…
As an example, consider a legitimate send_email tool that’s been thoroughly reviewed. An attacker publishes a…
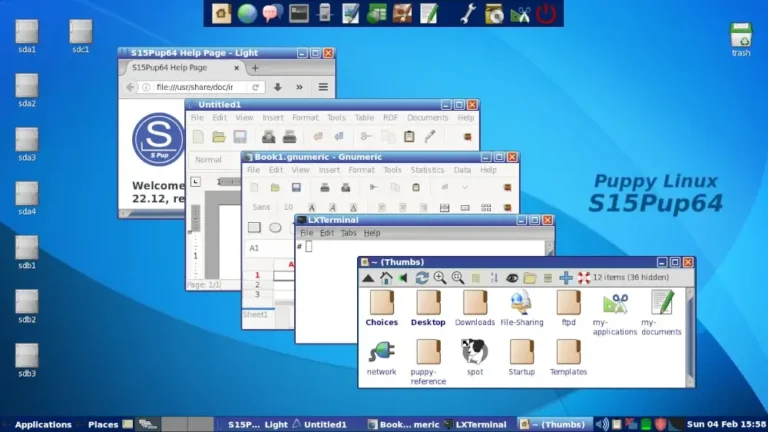
In this guide, we feature some of the best Linux distributions that you can install on…
Christoph Bausewein is Assistant General Counsel for Data Protection and Policy at CrowdStrike.This creates a new…
– System Security Manager, Services (non-Government) IndustryThe truest assessment of the Falcon platform comes from the…
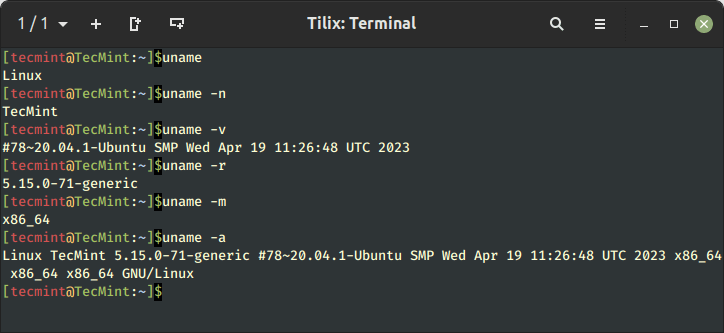
Learn 11 essential Linux commands to check hardware info including CPU, RAM, disk, USB, and PCI…
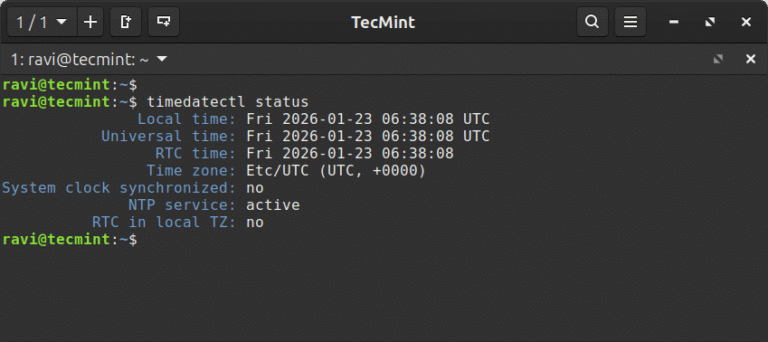
In this article, learn how to set time, timezone, and synchronize your Linux system clock with…