How to Keep Remote SSH Processes Alive Even When Disconnected
SSH or Secure Shell in simple terms is a way by which a person can remotely…
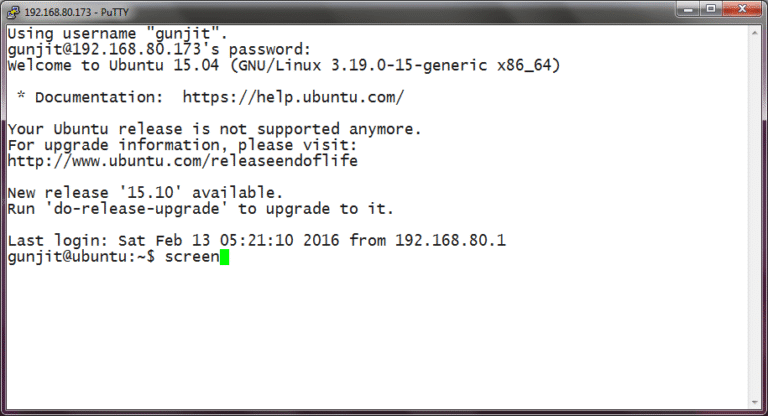
SSH or Secure Shell in simple terms is a way by which a person can remotely…
Identity has become a key battleground of modern cybersecurity. In 2024, 79% of CrowdStrike detections were…
There are two basic types of prompt injection attacks: Understanding Prompt Injection Employee BYO AI adoption…
WARP PANDA demonstrates a high level of stealth and almost certainly focuses on maintaining persistent, long-term,…
When most people think about operating systems, they picture Windows laptops or MacBooks, but here’s what’s…

When someone visits your website, their browser and your server exchange information back and forth. Without…
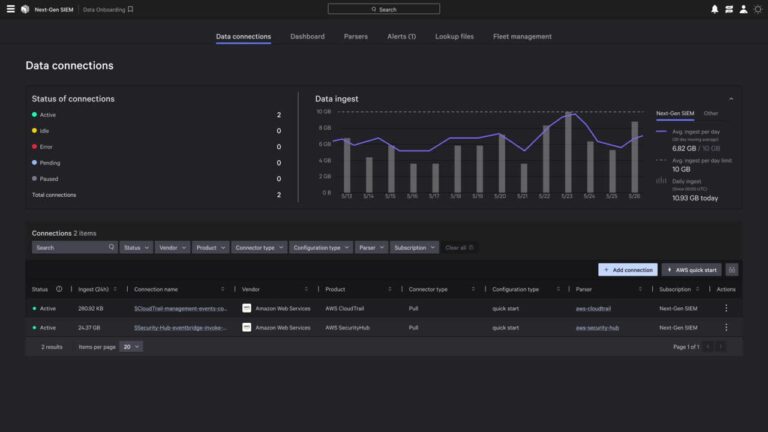
Perform on-demand queries for forensics, compliance, or audit use cases. CrowdStrike is the first cybersecurity partner…
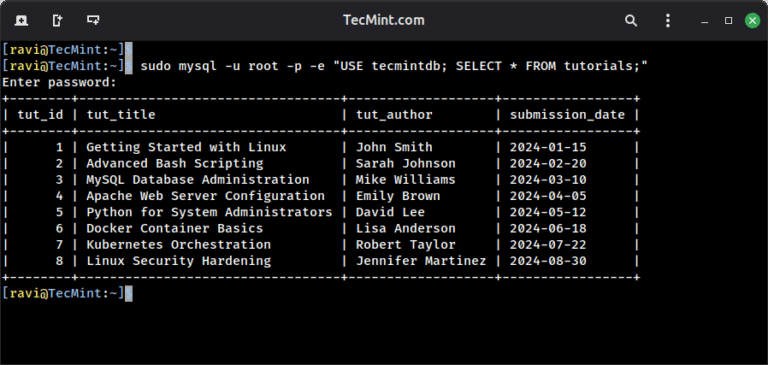
If you are in charge of managing a database server, from time to time you may…
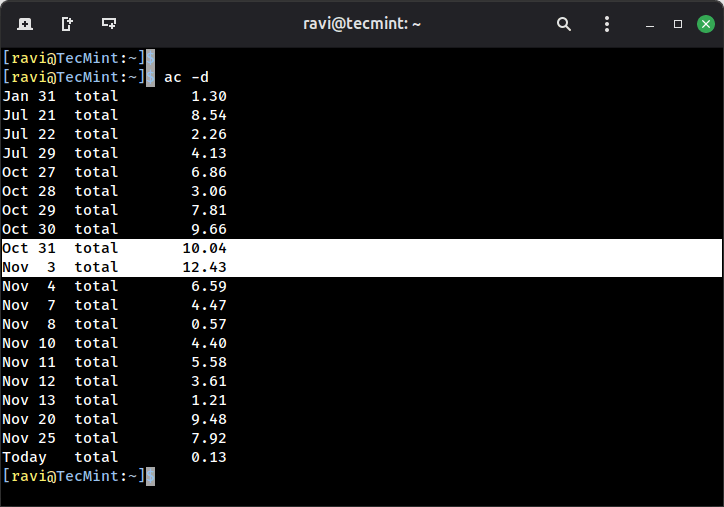
When you’re managing a Linux server, especially one with multiple users, you need visibility into what’s…
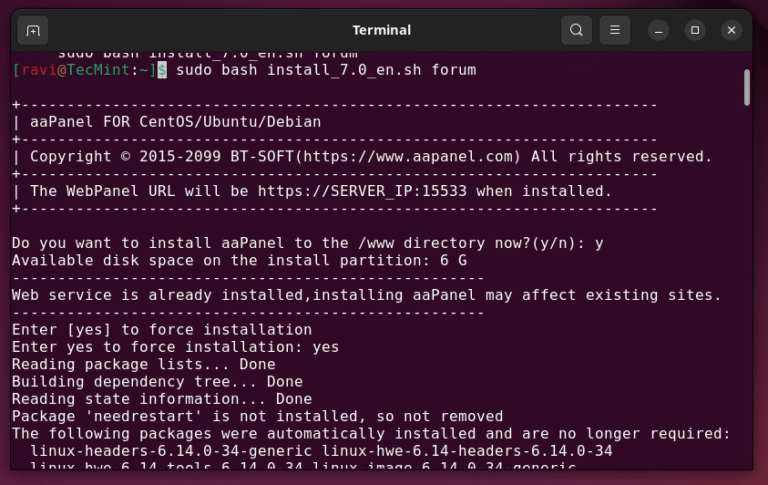
Managing a web server through command-line alone can feel like you’re juggling too many things at…
Despite the revolutionary agentic delivery mechanism used to achieve groundbreaking speed and scale in this attack,…
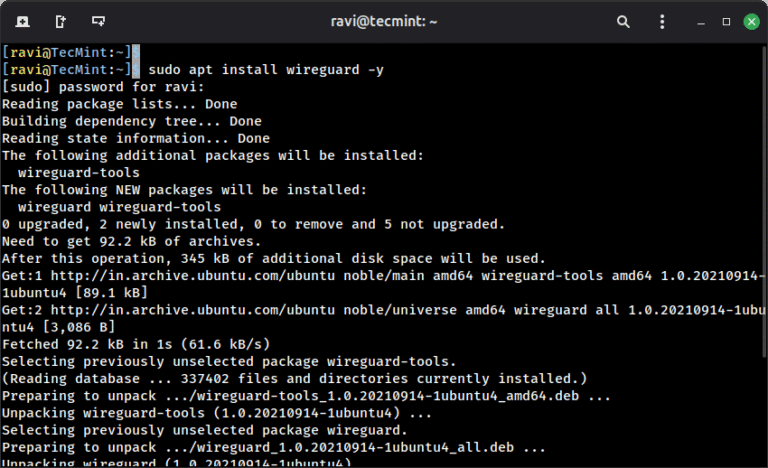
When you connect to a coffee shop’s WiFi or access the internet from any public network,…
Coerced Authentication The initial reconnaissance and setup phase requires minimal resources but careful planning. The attack…
Unsupported operating systems have historically become adversary targets. The longer a system remains unsupported, the more…

Unauthorized use of RMM tools has become especially dangerous: Throughout 2024, eCrime actors frequently used RMM…