VCF 9.0 GA Mental Model Part 1: Fleets, Instances, Domains, and the Fleet Management Layer
TL;DR This is the “where do we do the thing” map you want in every runbook….
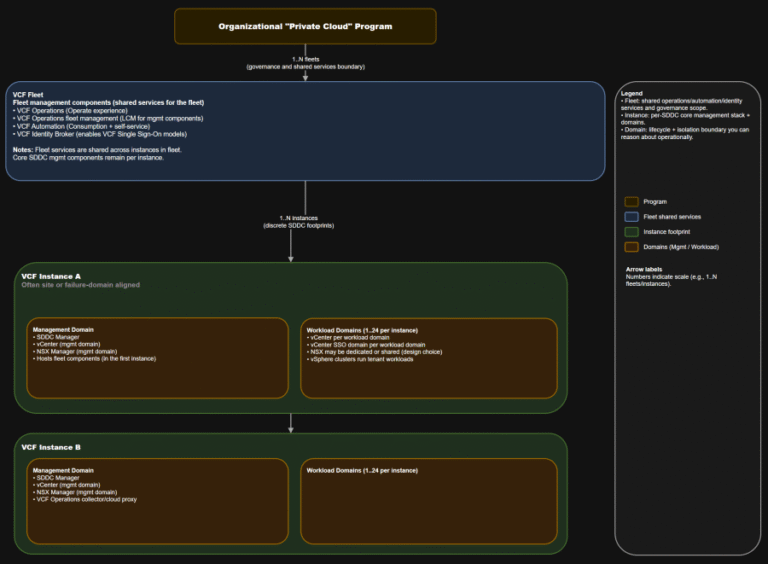
TL;DR This is the “where do we do the thing” map you want in every runbook….
CrowdStrike Falcon Identity Protection — A Great Tool to Gain Visibility We remain committed to innovating…
– System Engineer, IT Services “Overall, it’s been a valuable and eye-opening experience. The tool has helped…
Indirect prompt injection significantly amplifies this risk by allowing adversaries to influence OpenClaw’s behavior through data…
As AI adoption accelerated, WEX® — a global commerce platform that supports business operations primarily for…
As an example, consider a legitimate send_email tool that’s been thoroughly reviewed. An attacker publishes a…
Christoph Bausewein is Assistant General Counsel for Data Protection and Policy at CrowdStrike.This creates a new…
– System Security Manager, Services (non-Government) IndustryThe truest assessment of the Falcon platform comes from the…
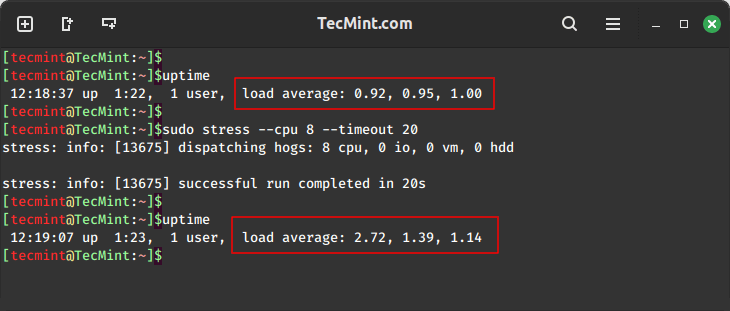
In this guide, we will explore two important tools, stress and stress-ng, for conducting comprehensive stress…
Types of AI Tool Poisoning Attacks Consider a scenario where an attacker publishes a tool with…
Under the Hood: How It Works Step 3: Dynamic behavioral analysis Step 5: Similar sample identification…
These content packs span multiple categories including application resilience, file discovery, Linux device control, and asset…
Pillar #1: A Rich Corpus of Human-refined Data In cybersecurity, AI agents don’t operate in a…
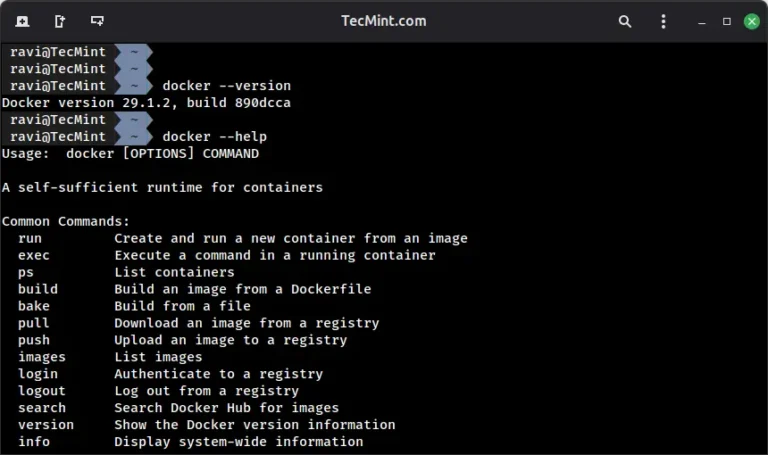
If you’re looking to get started with Docker, understanding how to work with its command-line interface…

In the MUSTANG PANDA scenario, the adversary embedded encoded shellcode within their malware in an attempt…