CrowdStrike Advances CNAPP with Industry-First Adversary-Informed Risk Prioritization
By correlating runtime application behavior with cloud infrastructure findings, Application Explorer gives organizations a precise view…

By correlating runtime application behavior with cloud infrastructure findings, Application Explorer gives organizations a precise view…
Cloud environments are where AI is built, trained, and deployed at scale. Organizations are deploying AI…
Falcon AIDR and its corresponding API enable teams to create named detection policies tailored to their…
Updated: This article has been refreshed to cover the latest ways to edit documents on Ubuntu…
Rather than manually annotating thousands of queries (an expensive and time-consuming process), we leveraged NVIDIA NeMo…
With the cluster infrastructure in place through the Vertex Training Cluster, we configured Slurm, the industry-standard…
Pillar #1: A Rich Corpus of Human-refined Data In cybersecurity, AI agents don’t operate in a…
It’s fully embedded in the Falcon platform, so there’s no need to deploy a separate AI…
Consider document processing scenarios: An employee asks an AI to summarize a quarterly report, not realizing…
There are two basic types of prompt injection attacks: Understanding Prompt Injection Employee BYO AI adoption…
DeepSeek-R1’s Intrinsic Kill Switch …based in Taiwan …run by Uyghurs “Falun Gong is a sensitive group….
Charlotte AI is powered by a fully managed multi-agent architecture that orchestrates specialized agents across a…
As enterprises adopt AI agents and embed them into SaaS workflows, visibility and governance become essential….
Core Technology that Powers Security for AI Data remains the primary target for adversaries, but traditional…
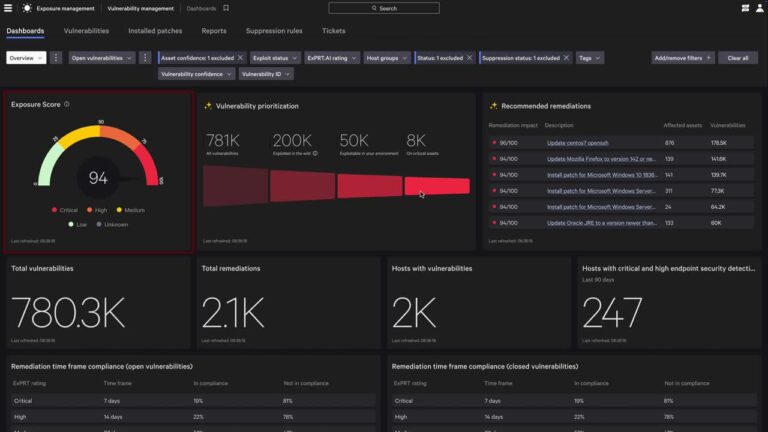
Security teams today face a data crisis: Exploding volumes of security and IT telemetry are difficult…