STARDUST CHOLLIMA Likely Compromises Axios npm Package
Since the end of Q4 2025, STARDUST CHOLLIMA’s operational tempo has surged and has continued at…
Since the end of Q4 2025, STARDUST CHOLLIMA’s operational tempo has surged and has continued at…
Charlotte Agentic SOAR provides the critical components needed to operationalize an agentic defense: It brings together:…

This is critical in a world where data exposure may stem from employee negligence, malicious insider…

By correlating runtime application behavior with cloud infrastructure findings, Application Explorer gives organizations a precise view…
Falcon Onum introduces a new paradigm for data management by allowing teams to intelligently prioritize and…
Modern investigations demand speed, scale, and consistency — but manual workflows, swivel-chair tooling, and knowledge gaps…
Detect Exposures and Prioritize Threats to Connected Medical Devices The lightweight Falcon sensor will use threat…
This milestone comes as the UK places increased emphasis on cyber resilience, operational assurance, and incident…

Stopping compromised access at login is essential, but identity risk doesn’t end there. CrowdStrike acquired SGNL…
To defend themselves, security leaders need clarity on which adversaries to watch, the details of their…
Insider threats pose a growing risk to organizations. Whether insiders take malicious actions, exhibit negligent behavior,…

Whether you’re building your first automation workflow or exploring how AI can simplify everyday SOC tasks,…
The Human-AI Feedback Loop in Action Expert-Annotated Data Enables Analyst Grade AI 2 Time savings represents…
Actively Exploited Zero-Day Vulnerability in Windows Remote Desktop The vulnerability allows local attackers with no privileges…
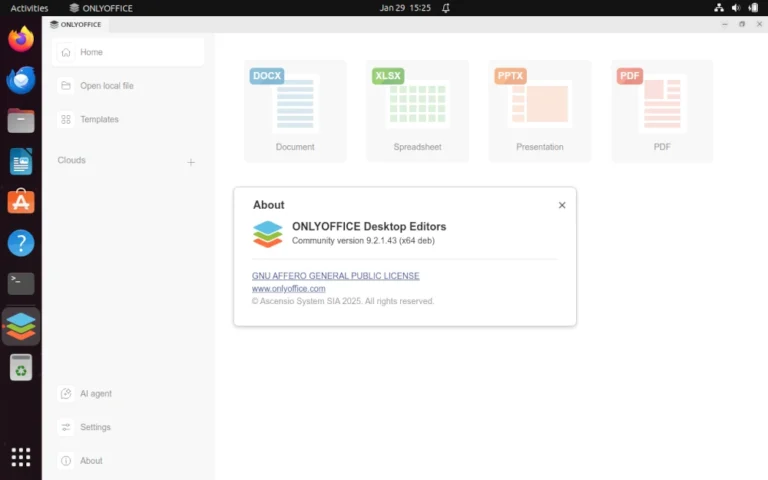
Learn how to enable and configure AI agents in ONLYOFFICE Desktop Editors to automate document editing,…