CrowdStrike and Zscaler Bring Continuous Identity to Zero Trust Access
A rule configured in Falcon Next-Gen Identity Security’s CAEP Hub triggers a risk level change event,…

A rule configured in Falcon Next-Gen Identity Security’s CAEP Hub triggers a risk level change event,…
Closing the gap between exposure and remediation requires AI that can reason across the entire environment,…
The analysis emphasizes CrowdStrike’s ability to deliver: Frost & Sullivan has named CrowdStrike its 2026 Company…
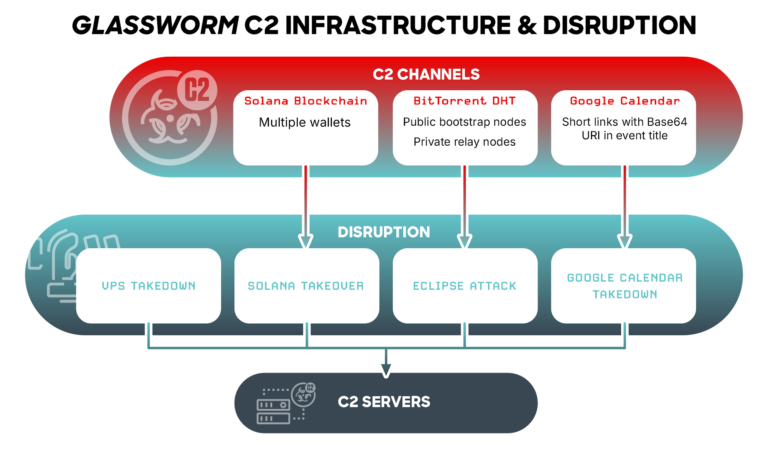
This case demonstrates: rule CrowdStrike_GlasswormRat_01 : glassworm glasswormrat { meta: copyright = “(c) 2026 CrowdStrike Inc.”…
AI is among the fastest-growing and most privileged application categories in the enterprise — and one…
Learn more: Download the CrowdStrike 2026 Financial Services Threat Landscape Report The trends outlined in this…

Threat Intelligence for the AI Era Today’s adversaries are using AI to accelerate their speed, scale,…

Falcon OverWatch for Defender builds on CrowdStrike’s open approach to Microsoft environments. With the lightweight Falcon…

The key shift isn’t replacing human creativity, it’s enhancing it. AI handles the heavy lifting, while…
In our Technical Risk Assessments, we consistently find that this external footprint is larger and more…
“I’ve been saying since November, we’re looking at three to nine months until a massive influx…

Complexity has become a defining security challenge as organizations expand across hybrid and multi-cloud environments. In…
As discovery becomes faster and more automated, the ability to validate exposure and act on it…
Frontier labs drive AI innovation. CrowdStrike delivers the intelligence, protection, and governance to put it to…
A frontier model is the engine. Data is the fuel. The platform is how you operationalize…