Inside the Human-AI Feedback Loop Powering CrowdStrike’s Agentic Security
The Human-AI Feedback Loop in Action Expert-Annotated Data Enables Analyst Grade AI 2 Time savings represents…
The Human-AI Feedback Loop in Action Expert-Annotated Data Enables Analyst Grade AI 2 Time savings represents…
SE Labs employed both direct attacks and deep attacks. Test results and the feedback of third-party…
As an example, consider a legitimate send_email tool that’s been thoroughly reviewed. An attacker publishes a…
Christoph Bausewein is Assistant General Counsel for Data Protection and Policy at CrowdStrike.This creates a new…
– System Security Manager, Services (non-Government) IndustryThe truest assessment of the Falcon platform comes from the…
Precise device access: Security teams can allow, restrict, or block removable media based on device attributes,…
Expert Agents: Native AI Reasoning Across the Falcon Platform Effective threat triage requires correlating evidence across…
I’m delighted to announce CrowdStrike’s intent to acquire Seraphic, the leader in browser runtime security. With…
SGNL provides the runtime access enforcement layer that sits between modern identity providers and the SaaS…
Pillar #1: A Rich Corpus of Human-refined Data In cybersecurity, AI agents don’t operate in a…
The AI era is here — and it’s redefining cybersecurity. Organizations around the globe are adopting…
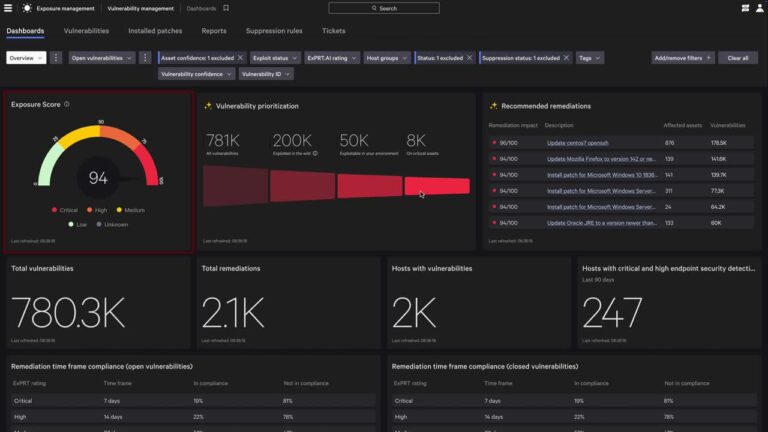
Organizations are under pressure to protect more devices, users, and distributed workloads than ever — while…
Traditional security tools were never built to protect AI assets across domains or the new AI…
It’s fully embedded in the Falcon platform, so there’s no need to deploy a separate AI…

In the MUSTANG PANDA scenario, the adversary embedded encoded shellcode within their malware in an attempt…