Falcon Data Security Secures Data Wherever It Lives and Moves
This is critical in a world where data exposure may stem from employee negligence, malicious insider…

This is critical in a world where data exposure may stem from employee negligence, malicious insider…

By correlating runtime application behavior with cloud infrastructure findings, Application Explorer gives organizations a precise view…
Falcon Onum introduces a new paradigm for data management by allowing teams to intelligently prioritize and…
Cloud environments are where AI is built, trained, and deployed at scale. Organizations are deploying AI…
Falcon AIDR and its corresponding API enable teams to create named detection policies tailored to their…
Modern investigations demand speed, scale, and consistency — but manual workflows, swivel-chair tooling, and knowledge gaps…
Security analysts were spending the majority of their time on what leadership described as mechanical analysis….
Detect Exposures and Prioritize Threats to Connected Medical Devices The lightweight Falcon sensor will use threat…
TL;DR Scope: VMware Cloud Foundation 9.0.0.0 GA (primary platform build 24703748) and the associated 9.0 GA…
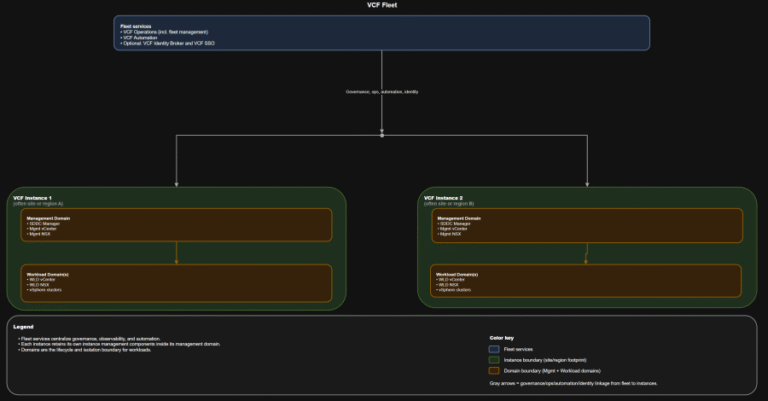
TL;DR Identity is not a “later” decision. It is a boundary decision. The hierarchy you should…
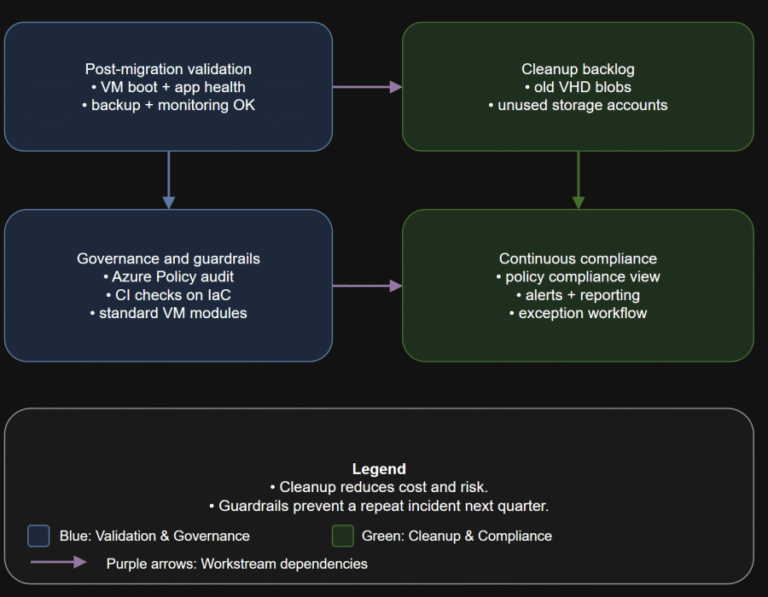
TL;DR Converting disks is not the finish line. Your real goal is a new steady state:…
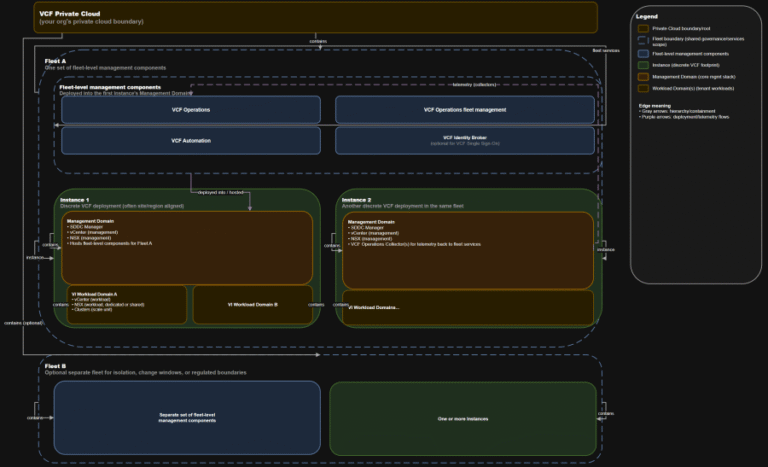
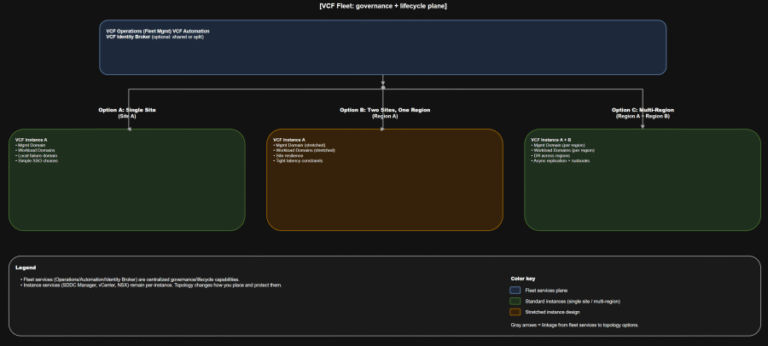
TL;DR A) One fleet, one instance, stretched where justified In VCF 9.0, identity is not a…
Insider threats pose a growing risk to organizations. Whether insiders take malicious actions, exhibit negligent behavior,…
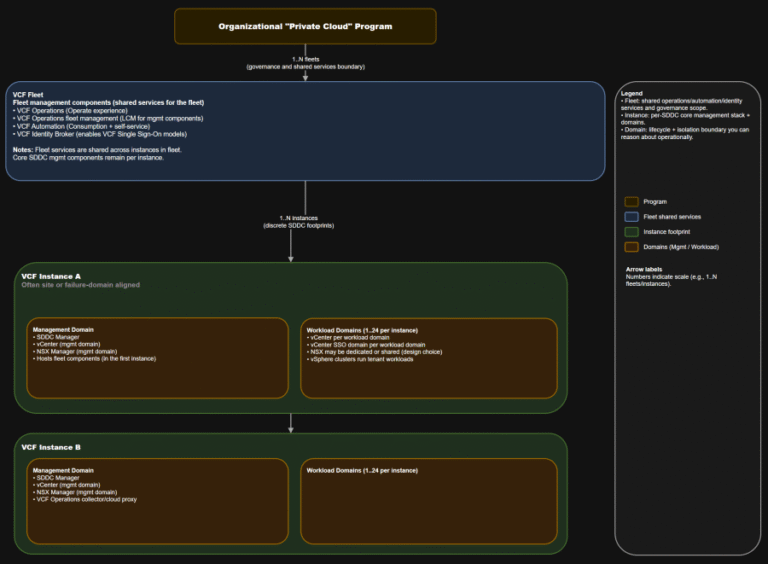
TL;DR This is the “where do we do the thing” map you want in every runbook….
As part of Falcon Cloud Security’s unified cloud-native application protection platform (CNAPP), Falcon ASPM helps organizations…