CrowdStrike Advances CNAPP with Industry-First Adversary-Informed Risk Prioritization
By correlating runtime application behavior with cloud infrastructure findings, Application Explorer gives organizations a precise view…

By correlating runtime application behavior with cloud infrastructure findings, Application Explorer gives organizations a precise view…
As part of Falcon Cloud Security’s unified cloud-native application protection platform (CNAPP), Falcon ASPM helps organizations…
Falcon Cloud Security has implemented a new approach which processes cloud logs as they stream in…
This isn’t just about saving time. It’s about enabling every stakeholder to see, understand, and act…
Charlotte AI is powered by a fully managed multi-agent architecture that orchestrates specialized agents across a…
Strengths Recognized in the Frost Radar Read the full report: 2025 Frost Radar™: Cloud Workload Protection…
For off-the-shelf capabilities like Bedrock or Vertex AI, Falcon Cloud Security identifies the APIs and services…
Container Escape Vectors Let’s review some examples of container escape vectors. The progression from initial container…
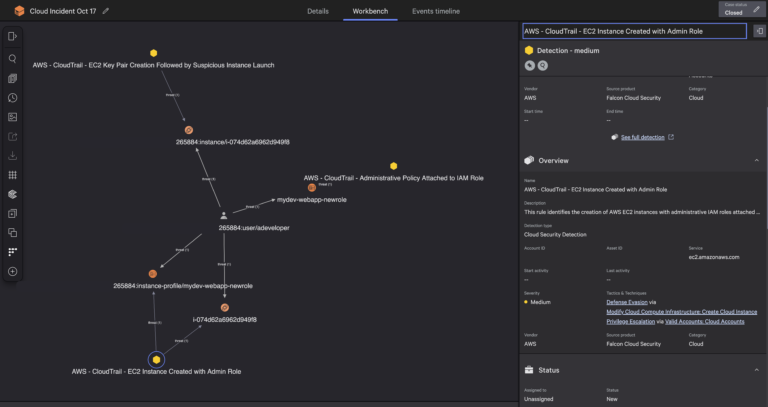
The Attack Path Analysis dashboard is the command center for identifying where defenders should focus first….
According to the IDC MarketScape: Strengths Recognized in the IDC MarketScape We believe CrowdStrike’s inclusion as…
LABYRINTH CHOLLIMA is a DPRK-nexus adversary that CrowdStrike has observed consistently targeting cloud environments.1 Below are…
With our unified platform approach, extensive threat intelligence, and proven track record of stopping breaches, CrowdStrike…
CrowdStrike’s new asset inventory collector for VMware vCenter enables organizations to see all virtual machines (VMs)…
Adversaries no longer operate in silos, and neither should defenders. Modern cross-domain attacks may start with…
Securing cloud environments at runtime is no easy feat. Unlike traditional infrastructure, cloud workloads are dynamic,…