How to Use Fedora Toolbx for Isolated Development Environments
Modern Linux development has moved beyond the traditional approach of installing everything directly on your system….
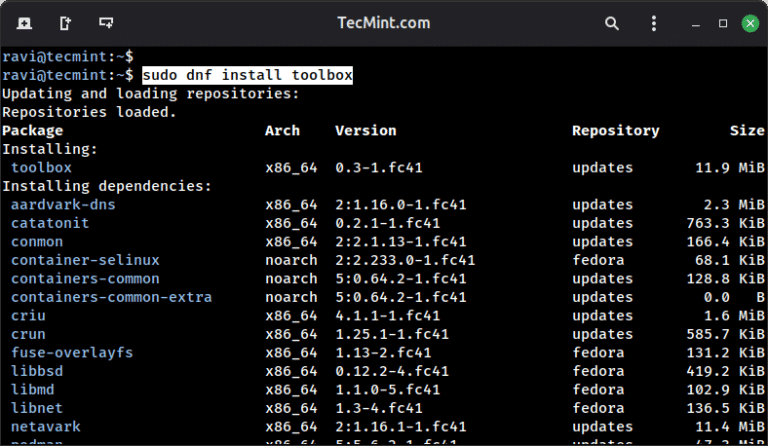
Modern Linux development has moved beyond the traditional approach of installing everything directly on your system….
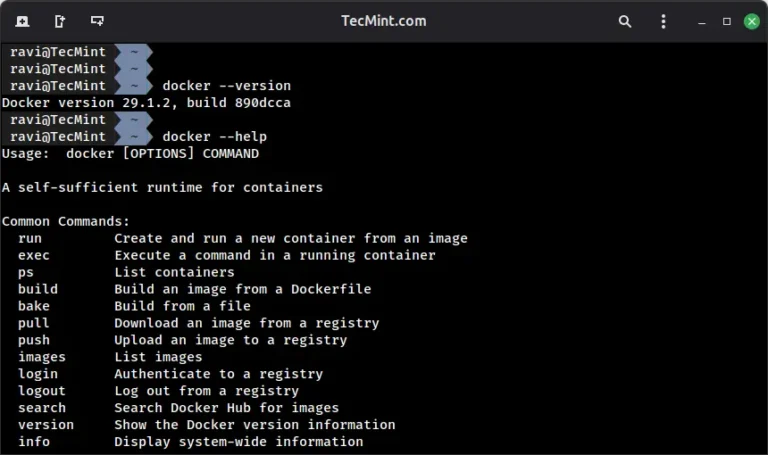
If you’re looking to get started with Docker, understanding how to work with its command-line interface…
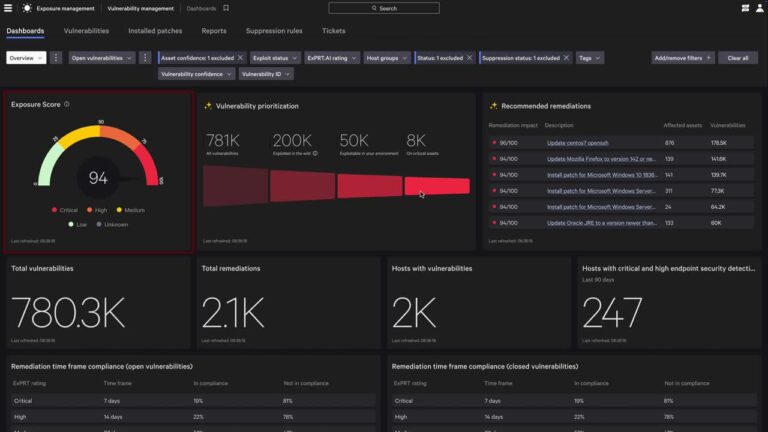
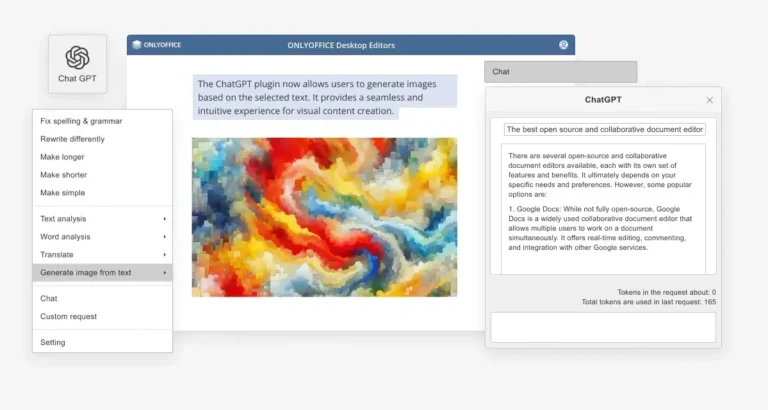
It’s fully embedded in the Falcon platform, so there’s no need to deploy a separate AI…
Consider document processing scenarios: An employee asks an AI to summarize a quarterly report, not realizing…
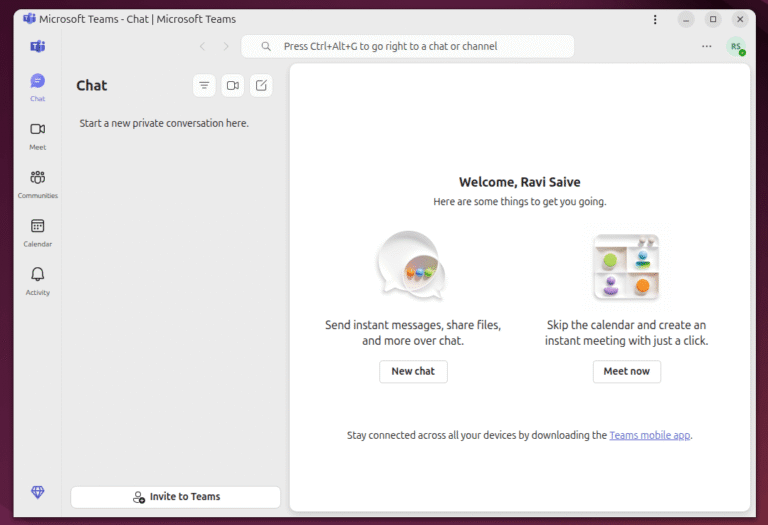
Gone are the days when Skype was the go-to VoIP tool for every chat, call, or…

There’s no doubt that Skype was once one of the most popular instant messaging and video…
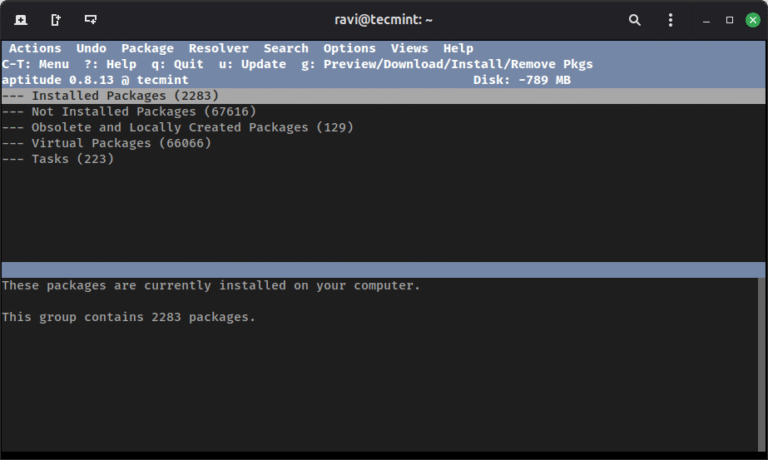
Debian offers several tools for managing software packages, each serving a specific purpose in the package…
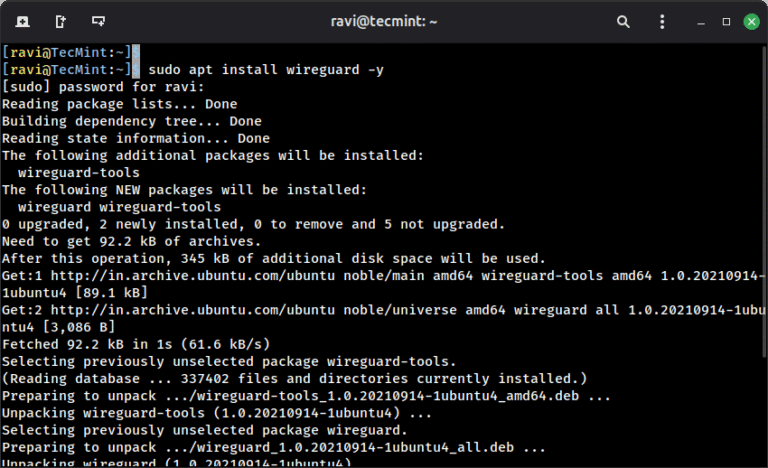
When you connect to a coffee shop’s WiFi or access the internet from any public network,…
Earlier this year, in testing against ransomware attacks, SE Labs employed realistic scenarios using tactics and…
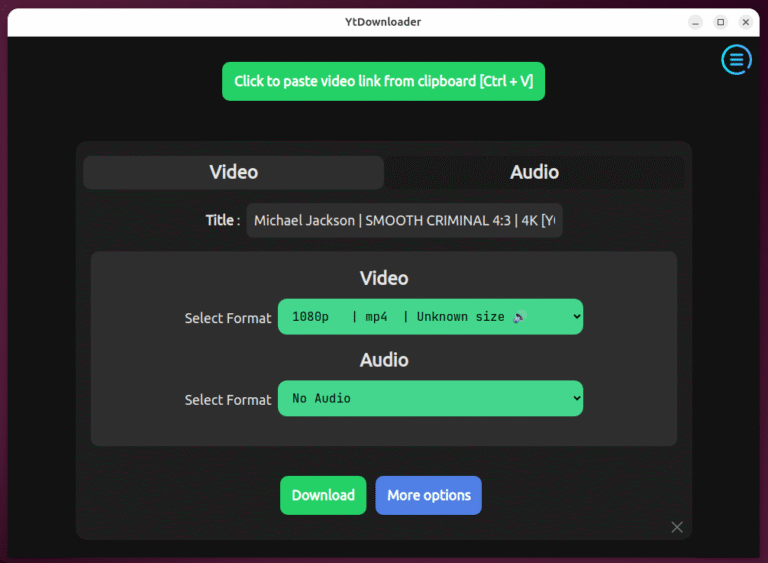
Earlier, I wrote about yt-dlp, the powerful command-line tool for downloading videos from hundreds of websites,…
Unsupported operating systems have historically become adversary targets. The longer a system remains unsupported, the more…

Unauthorized use of RMM tools has become especially dangerous: Throughout 2024, eCrime actors frequently used RMM…
Linux is an open-source operating system whose use is increasing these days as a result of…

SSH (Secure Shell) is one of the most important tools for Linux system administrators and developers,…
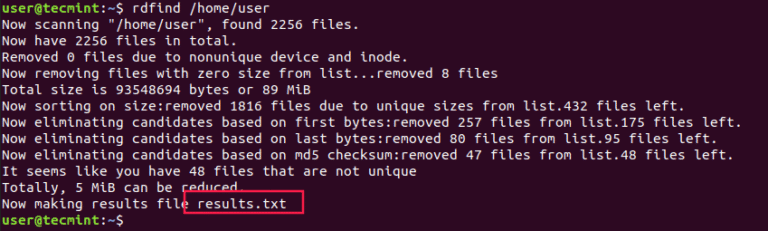
Organizing your home directory or even system can be particularly hard if you have the habit…