How to Stop Linux Processes from Using Excessive CPU and RAM
A process suddenly consuming 99% of your CPU at 2 AM can turn a stable server…
A process suddenly consuming 99% of your CPU at 2 AM can turn a stable server…
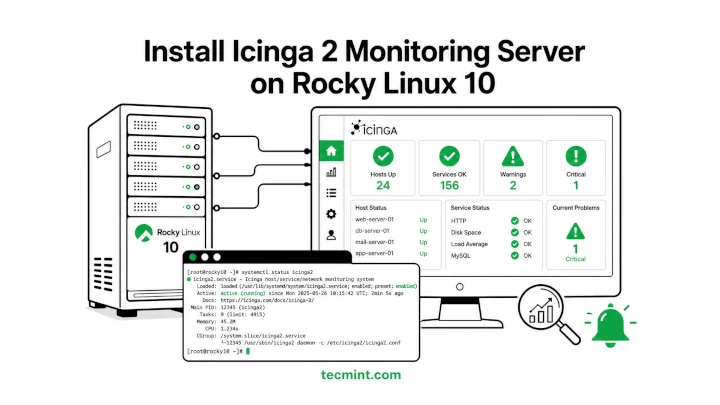
Icinga 2 is a free and open-source monitoring tool that helps you keep an eye on…
Cockpit ships pre-installed on Rocky Linux 10 and gives you a browser-based dashboard for managing your…
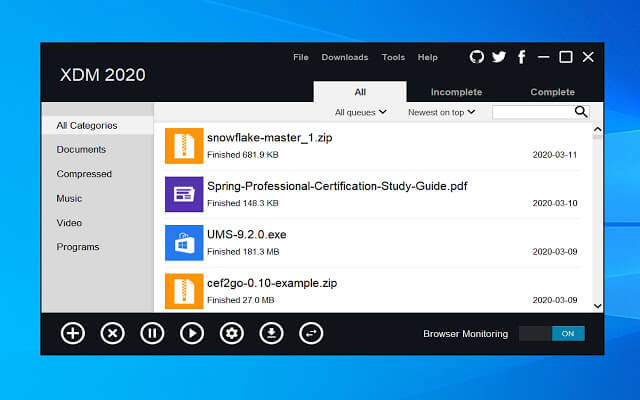
One thing many people miss after switching from Windows to Linux is a good download manager….

CrowdStrike has once again been named a Leader in the 2026 Gartner® Magic Quadrant™ for Endpoint…
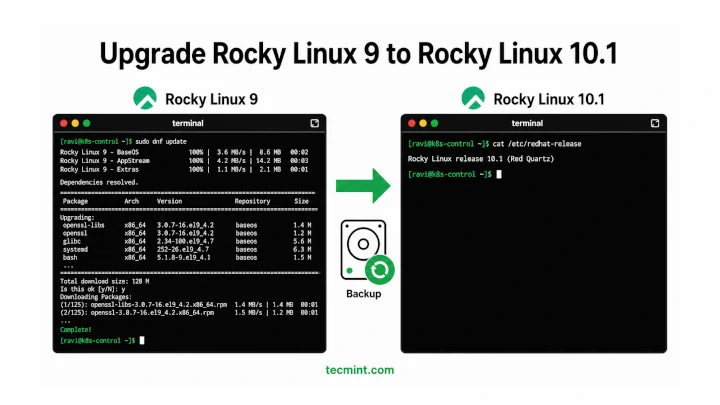
In this article, we’ll show you how to move from Rocky Linux 9 to Rocky Linux…
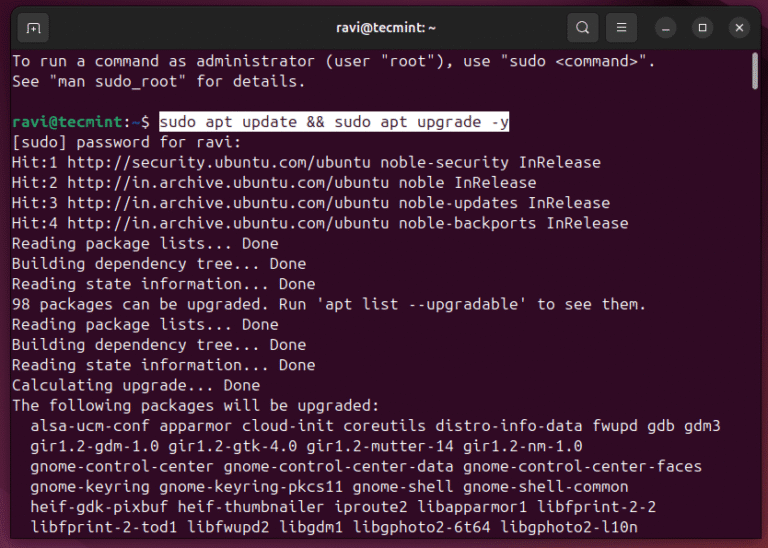
Ubuntu 26.04 LTS “Resolute Raccoon” shipped on April 23, 2026, and if you’re still on 24.04,…
C is one of the most important programming languages and the base for many modern technologies….
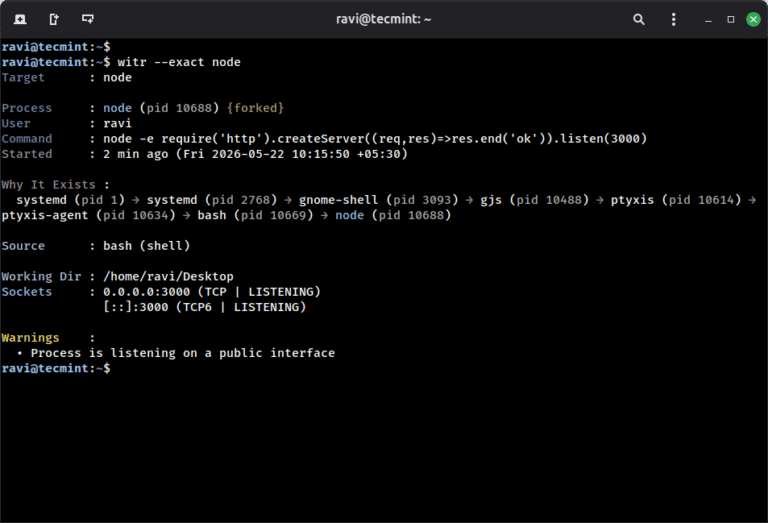
ps aux shows you what is running on your system, but witr goes a step further…
AI is among the fastest-growing and most privileged application categories in the enterprise — and one…
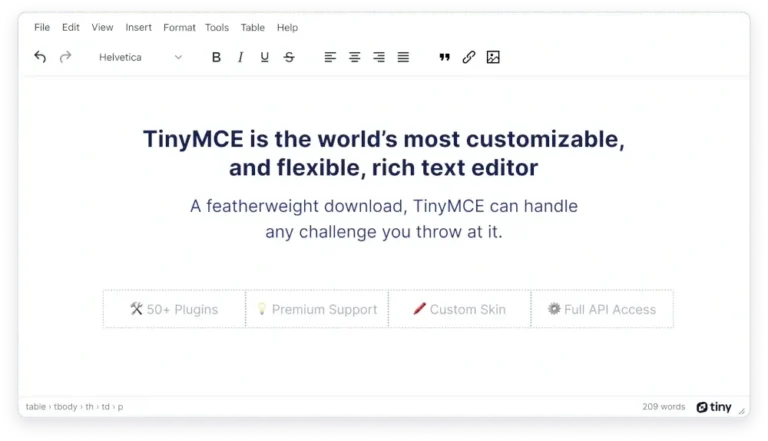
If you’re building a CMS, a documentation portal, or any web app where users type formatted…
Falcon AIDR analyzes these prompts and responses at runtime through OpenAI API calls captured by the…
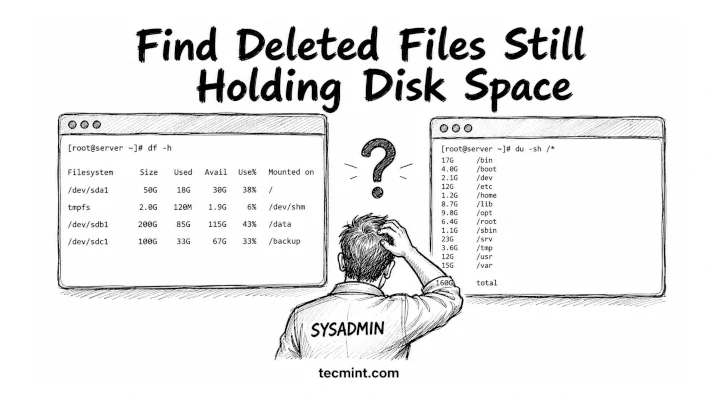
df says your disk is 80% full, but du says you’re barely using half, so one…
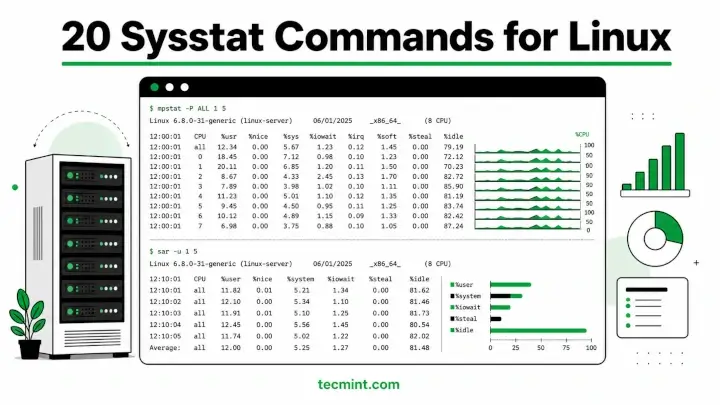
Sysstat is a collection of performance monitoring utilities for Linux that includes mpstat, pidstat, iostat, and…
Innovation and Growth Recognized by Frost & Sullivan Our investment in AI security extends beyond automation…