CrowdStrike Named a Leader in Identity Threat Detection and Response
The analysis emphasizes CrowdStrike’s ability to deliver: Frost & Sullivan has named CrowdStrike its 2026 Company…
The analysis emphasizes CrowdStrike’s ability to deliver: Frost & Sullivan has named CrowdStrike its 2026 Company…
A frontier model is the engine. Data is the fuel. The platform is how you operationalize…
Cloud environments are where AI is built, trained, and deployed at scale. Organizations are deploying AI…
Falcon AIDR and its corresponding API enable teams to create named detection policies tailored to their…
The Human-AI Feedback Loop in Action Expert-Annotated Data Enables Analyst Grade AI 2 Time savings represents…
Indirect prompt injection significantly amplifies this risk by allowing adversaries to influence OpenClaw’s behavior through data…
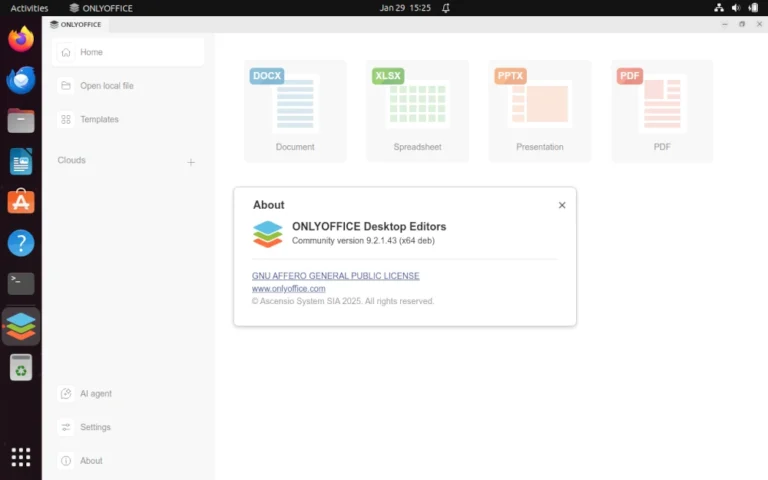
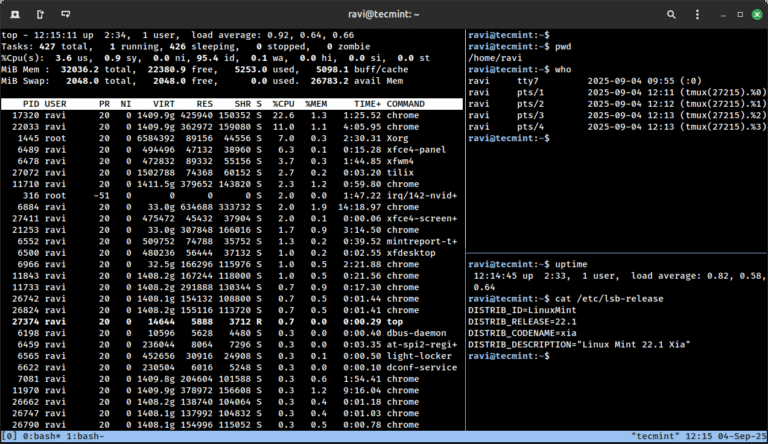
Learn how to enable and configure AI agents in ONLYOFFICE Desktop Editors to automate document editing,…
As an example, consider a legitimate send_email tool that’s been thoroughly reviewed. An attacker publishes a…
Types of AI Tool Poisoning Attacks Consider a scenario where an attacker publishes a tool with…
SGNL provides the runtime access enforcement layer that sits between modern identity providers and the SaaS…
Identity has become a key battleground of modern cybersecurity. In 2024, 79% of CrowdStrike detections were…
DeepSeek-R1’s Intrinsic Kill Switch …based in Taiwan …run by Uyghurs “Falun Gong is a sensitive group….
Despite the revolutionary agentic delivery mechanism used to achieve groundbreaking speed and scale in this attack,…
The fundamental shift we’re seeing is moving security professionals from operators to orchestrators. Today, we have…
It is time once again to share a list of the best free and open-source software…