11 Open-Source WYSIWYG Editors Worth Using in 2026
If you’re building a CMS, a documentation portal, or any web app where users type formatted…
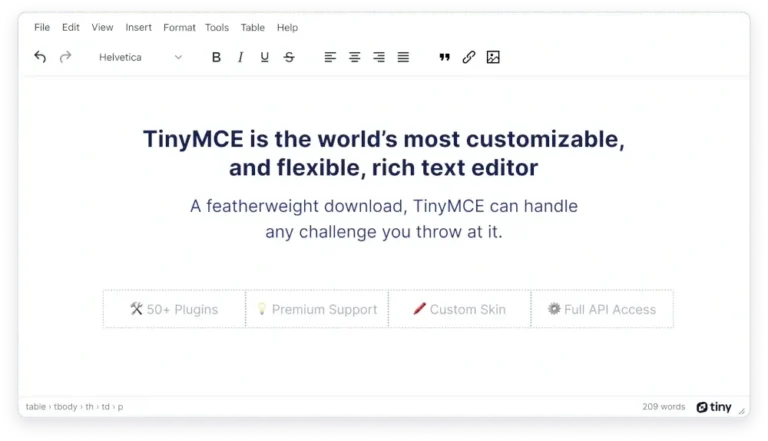
If you’re building a CMS, a documentation portal, or any web app where users type formatted…
Financial LossesThe impact of an infostealer attack can be devastating. Because infostealers quietly extract sensitive data,…
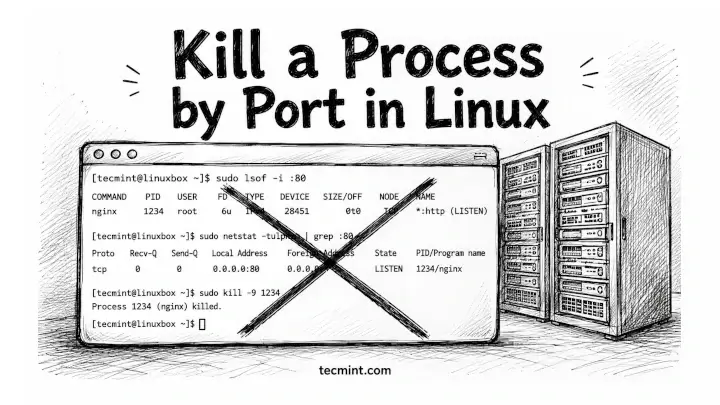
You’ve got a server refusing to start because something’s already sitting on port 8080, and you…
Learn more: Download the CrowdStrike 2026 Financial Services Threat Landscape Report The trends outlined in this…
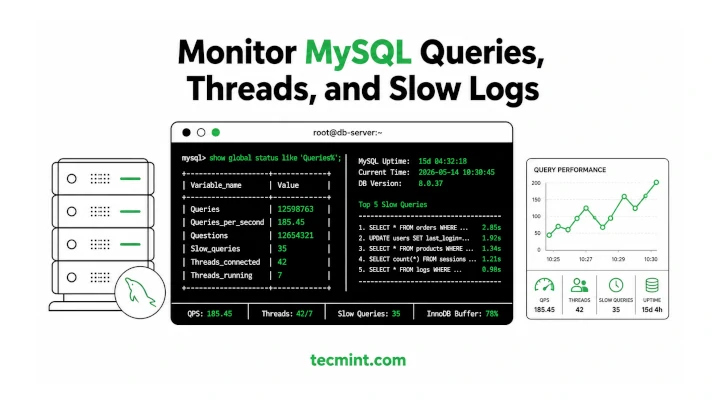
MySQL ships with decent built-in diagnostics, but when your database is slowing down under load, you…
Falcon AIDR analyzes these prompts and responses at runtime through OpenAI API calls captured by the…
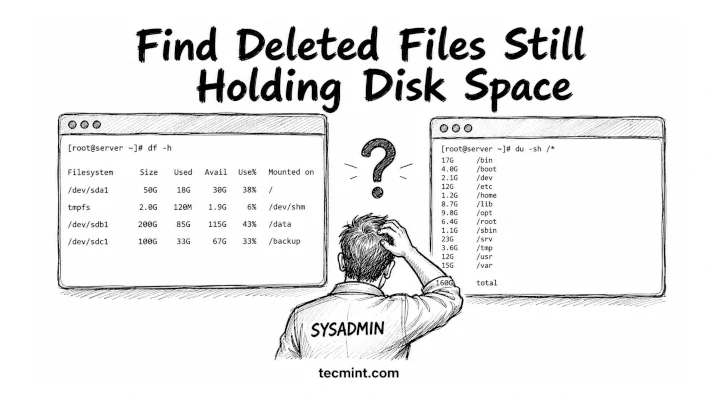
df says your disk is 80% full, but du says you’re barely using half, so one…
Critical Vulnerability in Azure DevOps CVE-2026-33823 is a Critical information disclosure vulnerability affecting the Microsoft Teams…
Improving detection is a core driver for the CrowdStrike Advanced Research team, which is behind the…
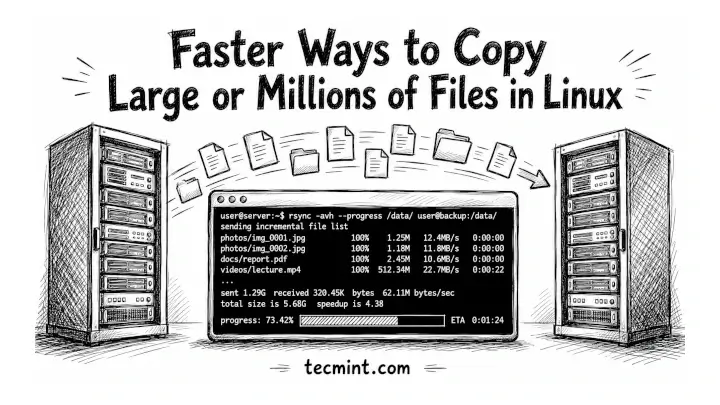
You’ve been copying files with cp for years, and if you’re moving a 50GB backup or…
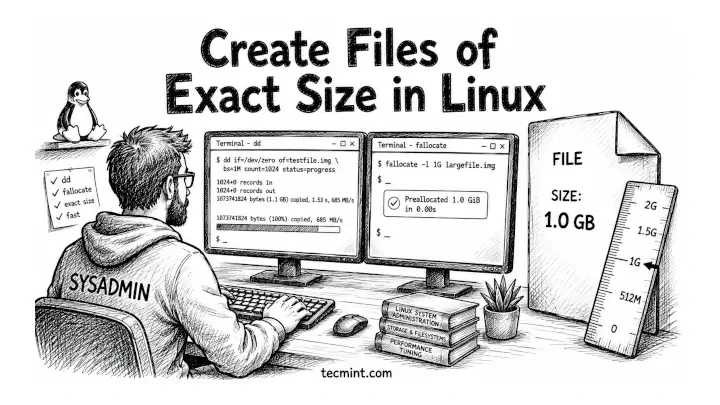
You need a 1GB test file to benchmark your disk, fill a partition to a specific…

Threat Intelligence for the AI Era Today’s adversaries are using AI to accelerate their speed, scale,…
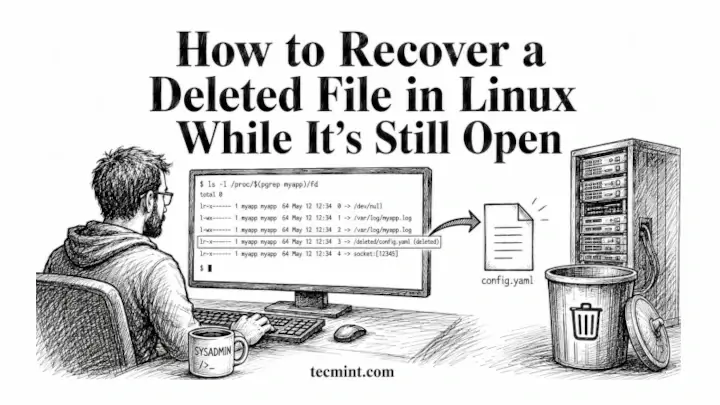
You deleted a log file mid-session, a running process is still writing to it, and ls…

Falcon OverWatch for Defender builds on CrowdStrike’s open approach to Microsoft environments. With the lightweight Falcon…
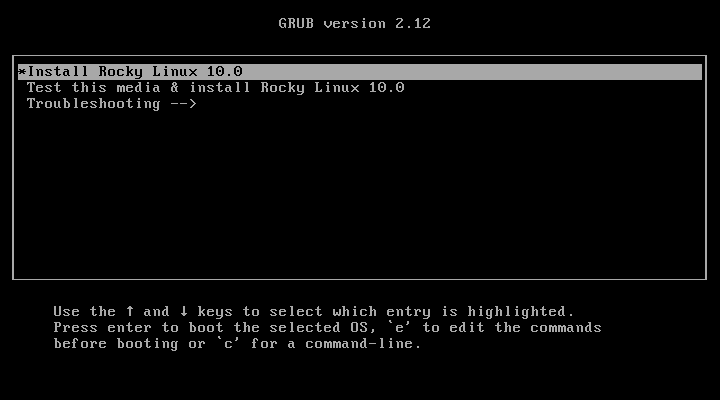
Rocky Linux 10 is the latest stable, community-driven enterprise Linux distribution built as a downstream rebuild…