Shadow AI: The Hidden Risk Expanding Across the Enterprise
Enterprises face new AI-specific attacks. For example, prompt injection techniques can manipulate models into exposing information,…
Enterprises face new AI-specific attacks. For example, prompt injection techniques can manipulate models into exposing information,…
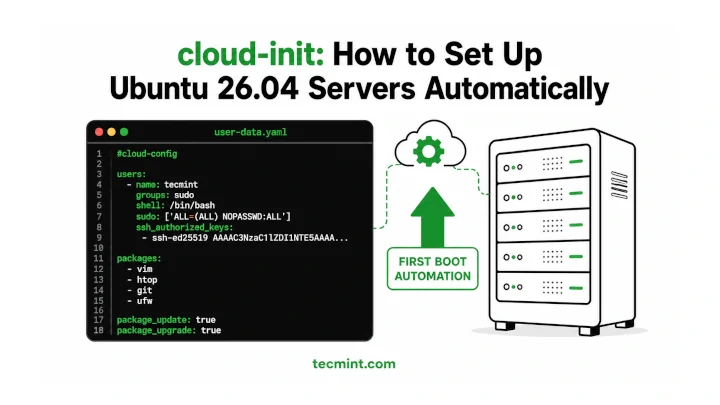
Installing and configuring cloud-init on Ubuntu 26.04 makes it much easier to automate server setup, especially…
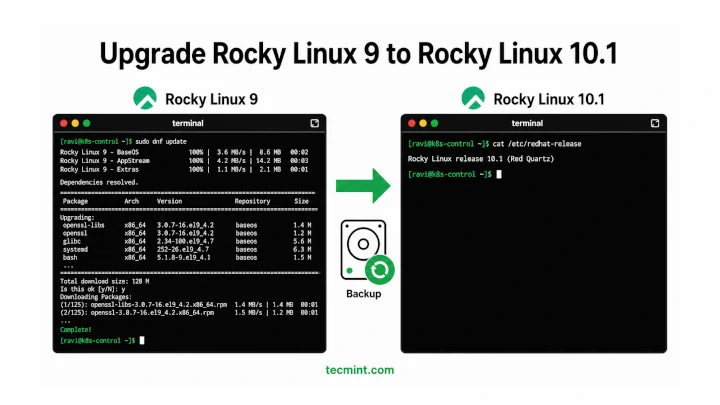
In this article, we’ll show you how to move from Rocky Linux 9 to Rocky Linux…

Testing different offers now can help you identify:Summer shoppers are often traveling and browsing from their…

Netplan is the default network configuration tool on Ubuntu since 18.04, replacing the older ifupdown system…
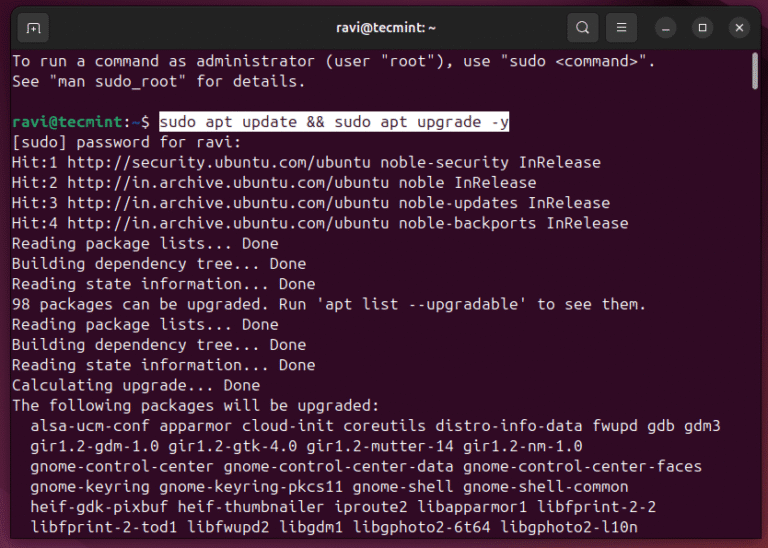
Ubuntu 26.04 LTS “Resolute Raccoon” shipped on April 23, 2026, and if you’re still on 24.04,…

A self-signed SSL certificate lets you run Apache over HTTPS on Ubuntu 26.04 without buying a…
The analysis emphasizes CrowdStrike’s ability to deliver: Frost & Sullivan has named CrowdStrike its 2026 Company…
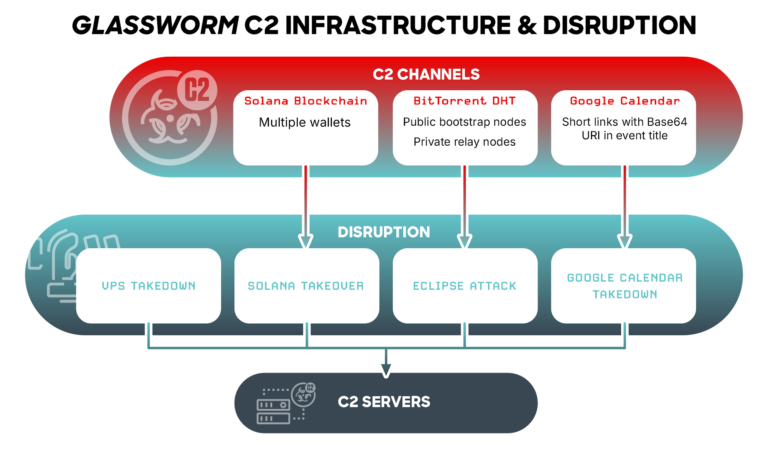
This case demonstrates: rule CrowdStrike_GlasswormRat_01 : glassworm glasswormrat { meta: copyright = “(c) 2026 CrowdStrike Inc.”…
C is one of the most important programming languages and the base for many modern technologies….
What it measures: The percentage of employees using approved AI tools, how frequently they use them,…
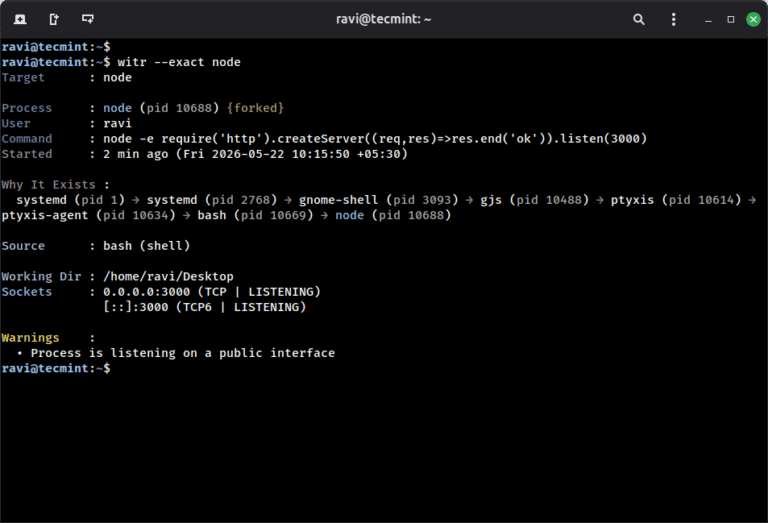
ps aux shows you what is running on your system, but witr goes a step further…
AI is among the fastest-growing and most privileged application categories in the enterprise — and one…
If you’re building a CMS, a documentation portal, or any web app where users type formatted…
Financial LossesThe impact of an infostealer attack can be devastating. Because infostealers quietly extract sensitive data,…