CrowdStrike 2026 Technology Threat Landscape Report: China’s Ambitions Fuel Attacks
The CrowdStrike 2026 Technology Threat Landscape Report, based on intelligence from the CrowdStrike Counter Adversary Operations…
The CrowdStrike 2026 Technology Threat Landscape Report, based on intelligence from the CrowdStrike Counter Adversary Operations…

A rule configured in Falcon Next-Gen Identity Security’s CAEP Hub triggers a risk level change event,…
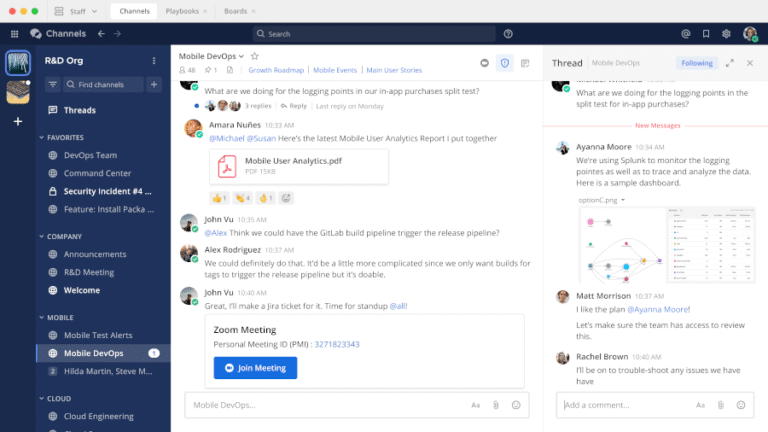
In this guide, we explore the best Microsoft Teams alternatives for Linux that you can use…
Organizations need to treat AI agents as privileged identities from Day One. This means enforcing least-privilege…
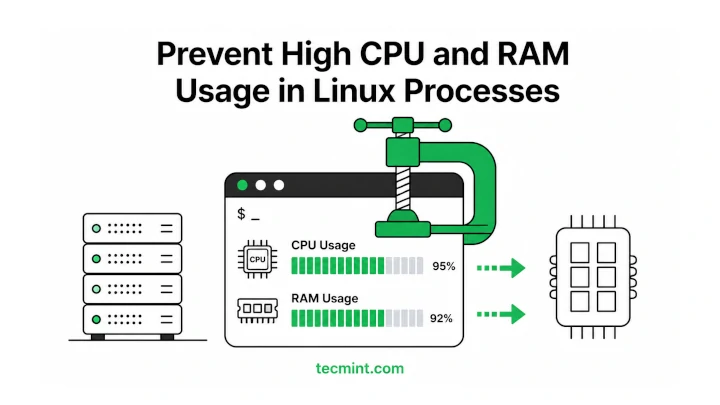
A process suddenly consuming 99% of your CPU at 2 AM can turn a stable server…
For example, teams can identify when sensitive data such as PII appears within a pipeline, even…
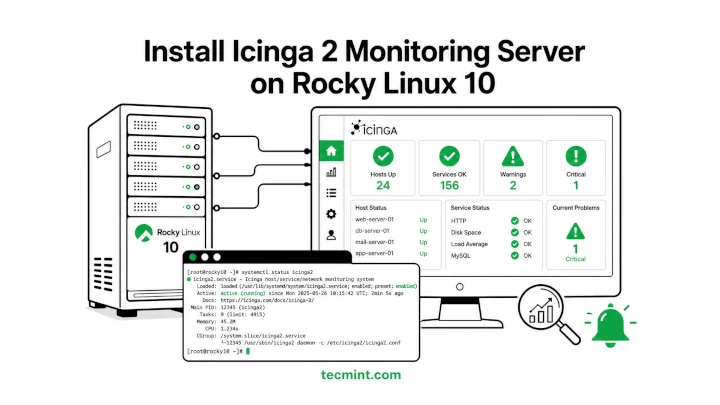
Icinga 2 is a free and open-source monitoring tool that helps you keep an eye on…
After all the configuration is validated and you kick off the workflow, it stops / errors…
Cockpit ships pre-installed on Rocky Linux 10 and gives you a browser-based dashboard for managing your…
Employees may unknowingly input sensitive information into AI chatbots, GenAI tools, or third-party platforms. Once the…

Rocky Linux 10 replaced VNC with RDP (Remote Desktop Protocol) for remote graphical installations, so if…
This content includes discussion of unreleased services or features. Any references to unreleased features reflect our…
Closing the gap between exposure and remediation requires AI that can reason across the entire environment,…
Falcon for IT delivers broad visibility into the systems and activity that define enterprise infrastructure, including…
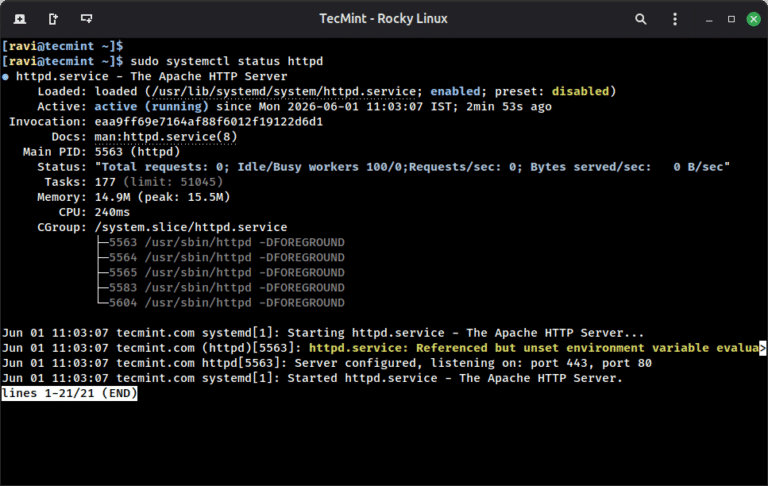
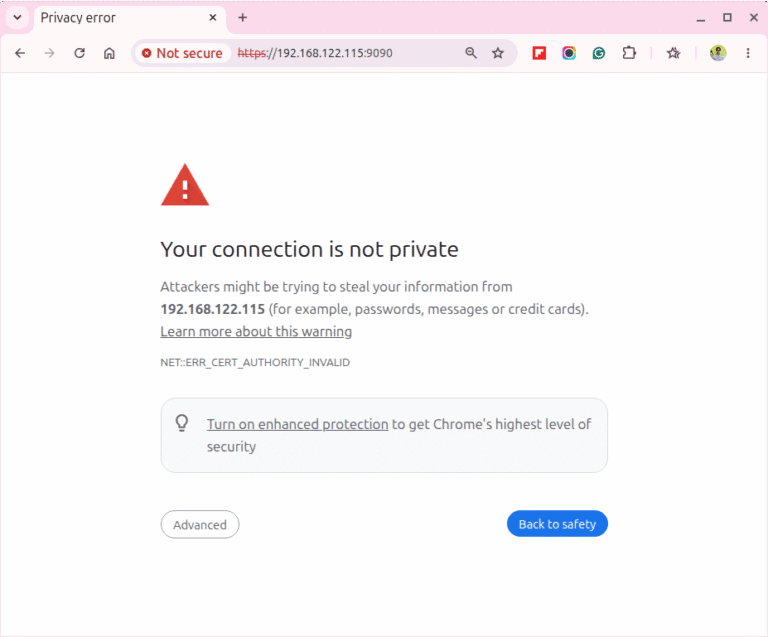
A self-signed SSL certificate lets you run Apache over HTTPS on Rocky Linux 10 without buying…