SOCKS5
At launch, Enhanced Network Visibility will support parsing of plaintext HTTP requests and responses and TLS client hello packets.
What Is Enhanced Network Visibility?
In this blog, we provide an in-depth overview of this new capability. We showcase detection enablement and numerous threat hunting applications, now enabled by Enhanced Network Visibility for macOS, and dive into new network capabilities built to empower threat hunters and detection teams against threat actor activity.
This capability leverages the latest Apple-native content filter APIs to enable enhanced network visibility with the least possible impact on network performance. The content filter API allows the sensor to intercept the least amount of data possible, allowing data for a network flow to bypass interception completely once the traffic has been identified. This targeted approach offers significant efficiency advantages over packet-based inspection methods, minimizing system impact while maximizing detection capabilities, all the while being an opt-in feature, allowing customers the choice to enable within their environments
The much-anticipated Enhanced Network Visibility feature for macOS is now generally available in sensor version 7.29 or later. This new capability provides insight and improved visibility into network traffic occurring on macOS endpoints, creating a more sophisticated and comprehensive model of process behavior.
#event_simpleName=HttpRequest
Supported Protocols
This event contains the request type, URL, headers, and body of a plaintext HTTP request. New interesting key/value pairs for this event are outlined below:
SOCKS4
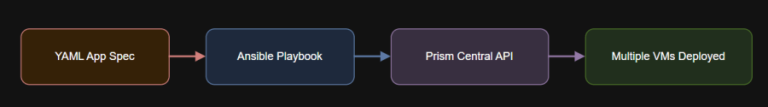
| Protocol | AppProtocol Value | Capability | Description |
| HTTP 1.x | 110 | Identify & Inspect | Plaintext HTTP requests and responses |
| TLS | 102 | Identify & Inspect | TLS client hello (client session establishment) |
| One of the new exciting features is the integration of JA4 fingerprinting (ref: https://foxio.io/). Additionally, the feature will identify the use of HTTP, TLS, SOCKS4/5, Wireguard, SSH, SMB, VNC, ARD, and DNS on any network port, emitting an AppProtocolDetected event when a process makes use of one of these protocols. Proxy visibility is also supported. |
104 | Identify & Inspect | Traffic encapsulated within a SOCKS4 or SOCKS5 proxy is supported transparently |
| Wireguard | 105 | Identify | Wireguard VPN |
| SSH | 108 | Identify | Secure shell |
| SMB | 112 | Identify | File sharing |
| VNC, ARD | 107 | Identify | Apple Remote Desktop (ARD) or VNC screen sharing |
| QUIC | 103 | Identify | IETF QUIC (and HTTP/3) traffic. Encrypted, but can process the embedded TLS client hello. |
| DNS | 100 | Identify & Inspect | Domain Name System |
New CrowdStrike Falcon Next-Gen SIEM Events
JA4 provides a summarized representation, or “signature,” of the capabilities and configuration of a specific TLS client library. This signature is derived from the TLS “client hello” packet, the first step in establishing a secure connection. JA4 can be used to differentiate between otherwise indistinguishable TLS connections, and can provide evidence of proxying, if a single process exhibits several unique signatures. JA4 was designed by FoxIO to replace JA3, which is not compatible with the TLS client extension randomized reordering employed by modern browsers and bots.
Enhanced network visibility supplements process activity monitoring with attributes derived from the contents of network traffic. Moving beyond basic network address and port data, this enhanced monitoring identifies specific application protocols, analyzes TLS (encrypted) traffic characteristics, and examines plaintext HTTP traffic attributes, further enriching the robust data set the Falcon sensor provides.