How to Use fsck to Check and Repair Linux Filesystem Errors
Linux filesystems are responsible for organizing how data is stored and retrieved. Over time – due…
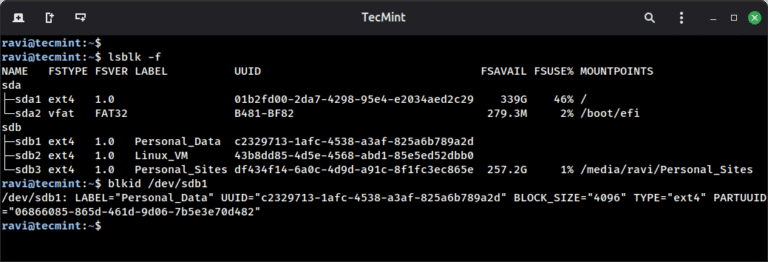
Linux filesystems are responsible for organizing how data is stored and retrieved. Over time – due…

Legacy SIEMs, fragmented toolchains, and manual workflows cannot keep up with the scale and complexity of…
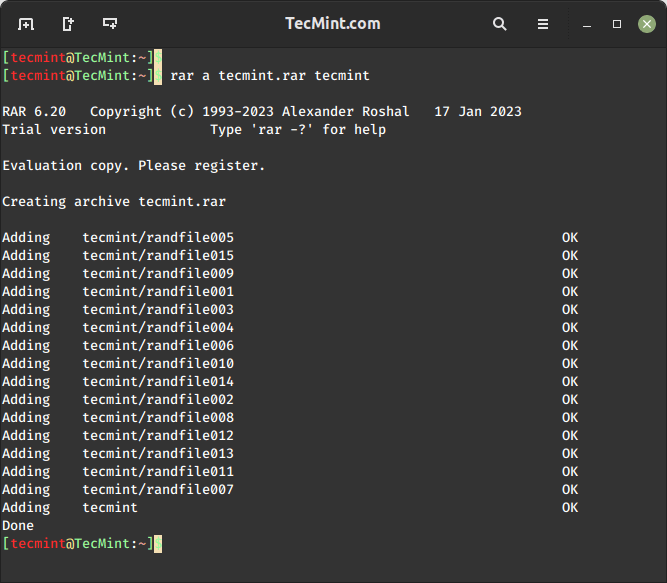
RAR files, a common compressed file format, are widely used to store and share large amounts…
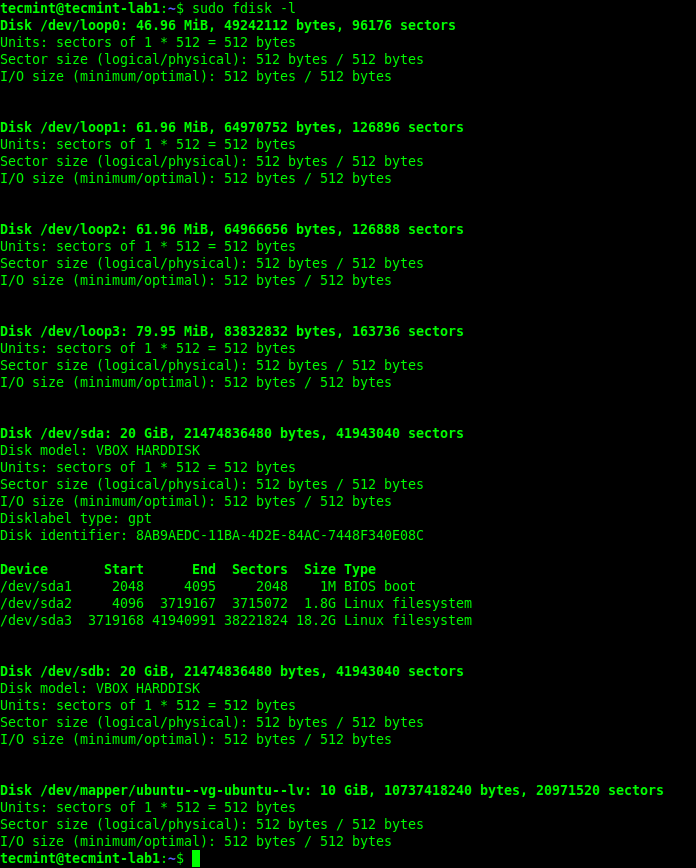
Whether you’re troubleshooting boot issues, preparing to format a drive, or setting up a new disk,…
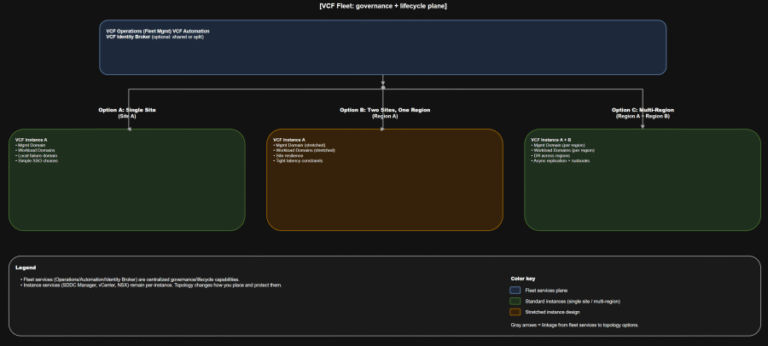
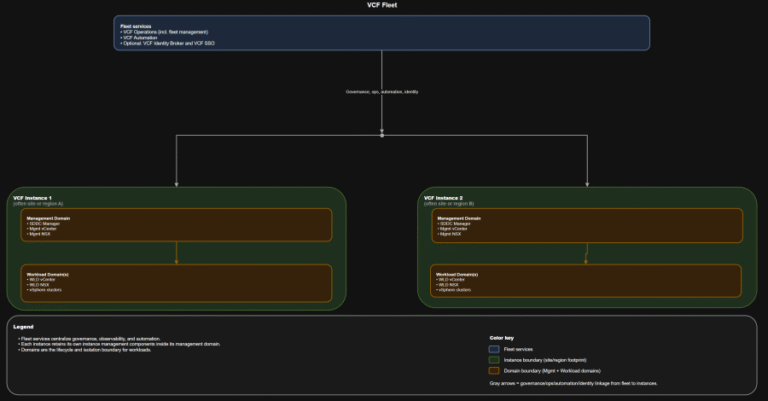
TL;DR Scope: VMware Cloud Foundation 9.0.0.0 GA (primary platform build 24703748) and the associated 9.0 GA…
TL;DR Identity is not a “later” decision. It is a boundary decision. The hierarchy you should…
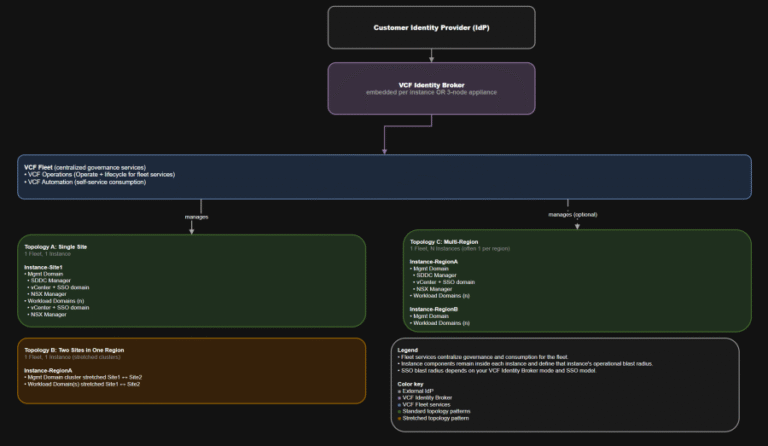
TL;DR This post targets VCF 9.0 GA only: VCF 9.0 (17 JUN 2025) build 24755599, with…
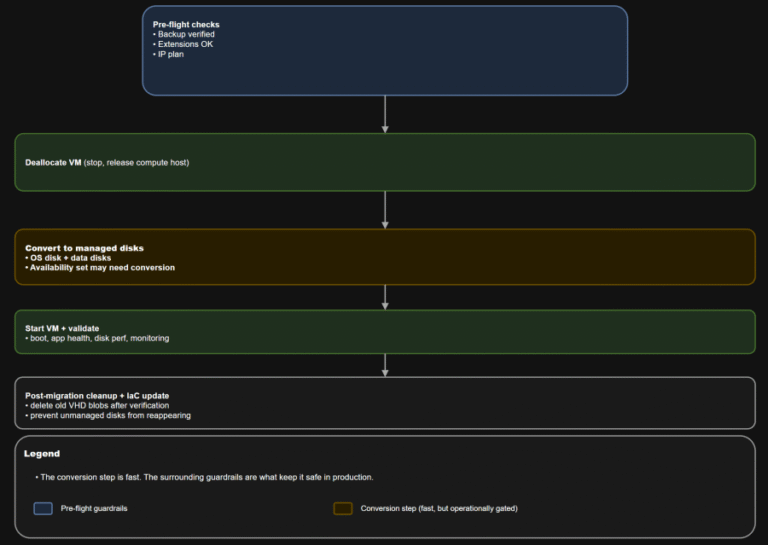
TL;DR Converting a VM to managed disks is usually operationally straightforward: deallocate, convert, start, validate. The…
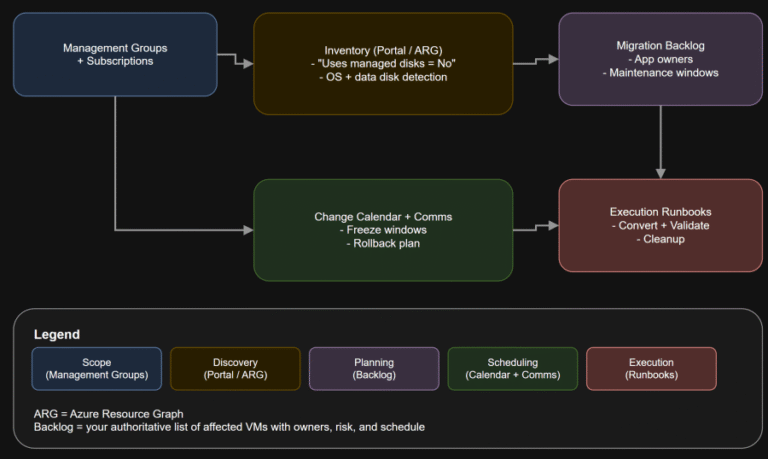
TL;DR If any Azure IaaS VM in your estate still uses unmanaged disks, it is on…
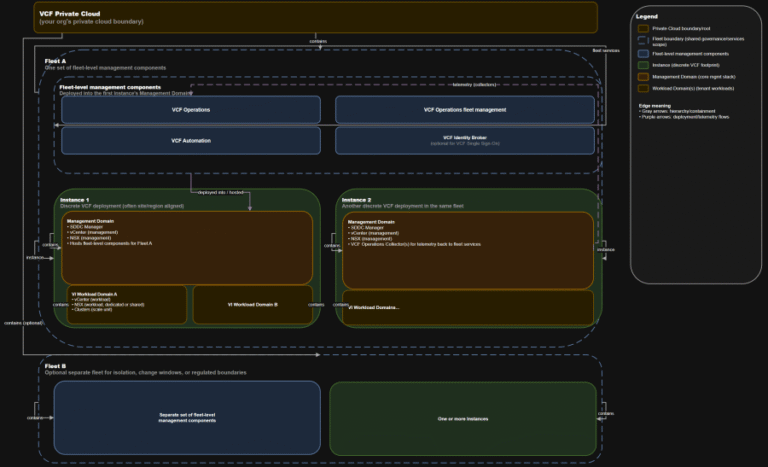
TL;DR A) One fleet, one instance, stretched where justified In VCF 9.0, identity is not a…
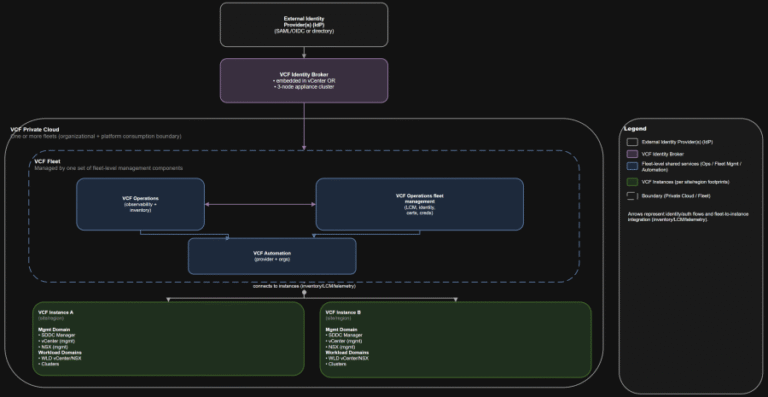
TL;DR Practical implication: if fleet services are impaired, governance and workflows degrade, but the instance-level control…
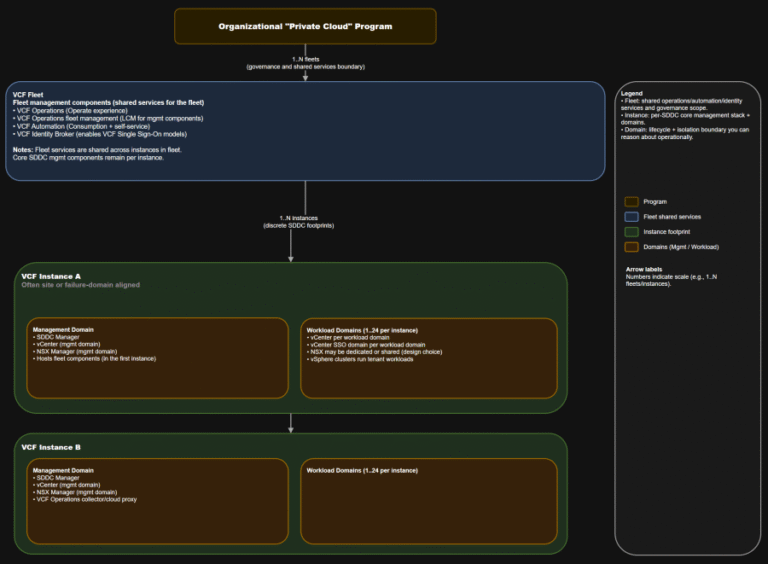
TL;DR This is the “where do we do the thing” map you want in every runbook….
SE Labs employed both direct attacks and deep attacks. Test results and the feedback of third-party…
The Leader in Identity Security Innovation The breadth of CrowdStrike’s detection capabilities is also highlighted: “Falcon…
AI-enhanced social engineering poses particular challenges. Attackers use generative AI to craft contextually appropriate phishing emails…