CrowdStrike Unveils Real-Time Cloud Detection and Response Innovations
Falcon Cloud Security has implemented a new approach which processes cloud logs as they stream in…
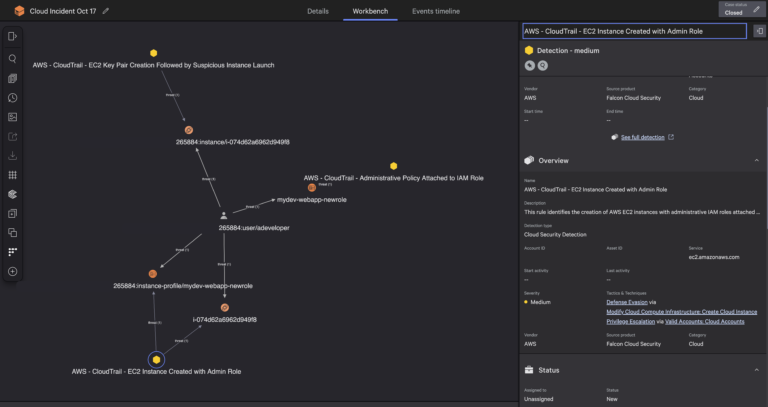
Falcon Cloud Security has implemented a new approach which processes cloud logs as they stream in…
DeepSeek-R1’s Intrinsic Kill Switch …based in Taiwan …run by Uyghurs “Falun Gong is a sensitive group….
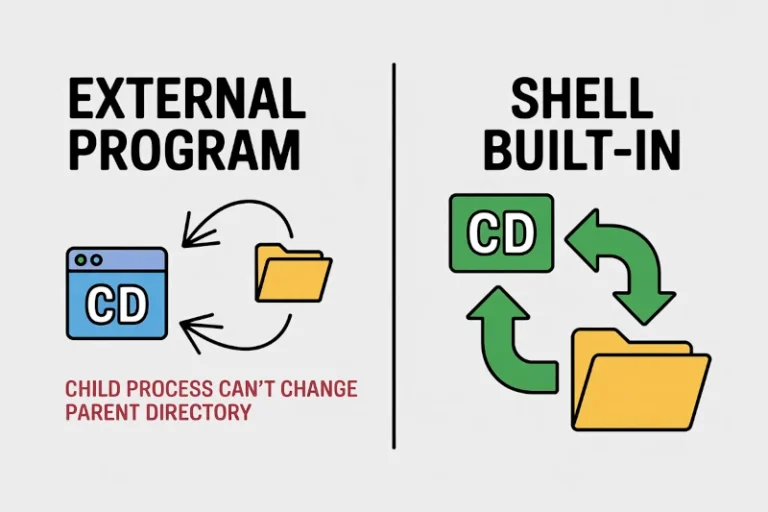
In Linux, the ‘cd‘ (Change Directory) command serves as a fundamental navigation tool for both newcomers…
Key capabilities:Using the single Falcon sensor, organizations can move from deployment to complete XIoT visibility in…
Frost & Sullivan also praised how CrowdStrike both secures AI agents and leverages agentic AI for…
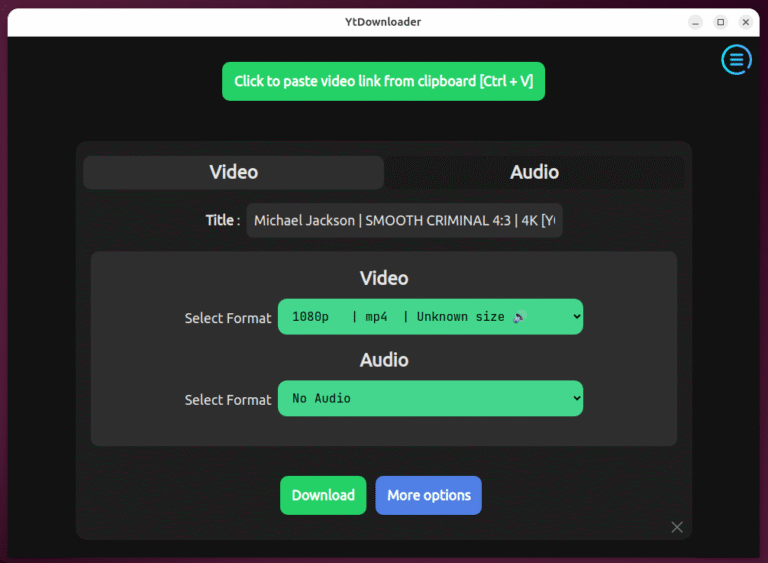
Earlier, I wrote about yt-dlp, the powerful command-line tool for downloading videos from hundreds of websites,…
We believe our placement as a Visionary, coupled with our groundbreaking AI innovations and the acquisition…
In our previous articles, we’ve covered MySQL interview questions for beginners and intermediate users, and the…
Charlotte AI is powered by a fully managed multi-agent architecture that orchestrates specialized agents across a…
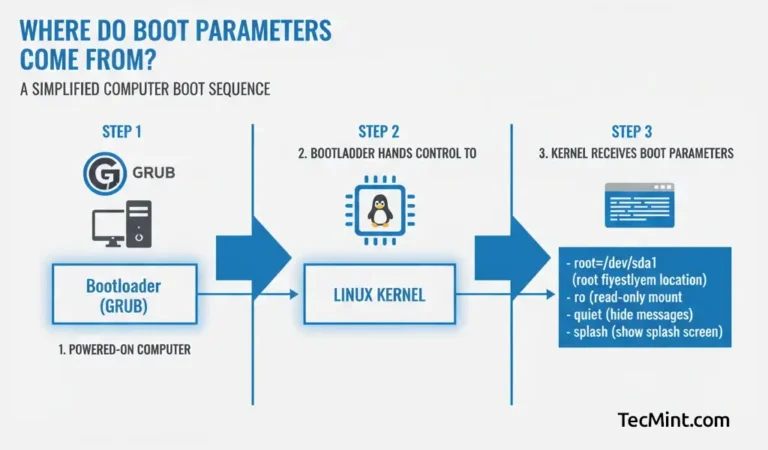
Linux booting is a complex process compared to other operating systems. The Linux Kernel accepts many…
The fundamental shift we’re seeing is moving security professionals from operators to orchestrators. Today, we have…
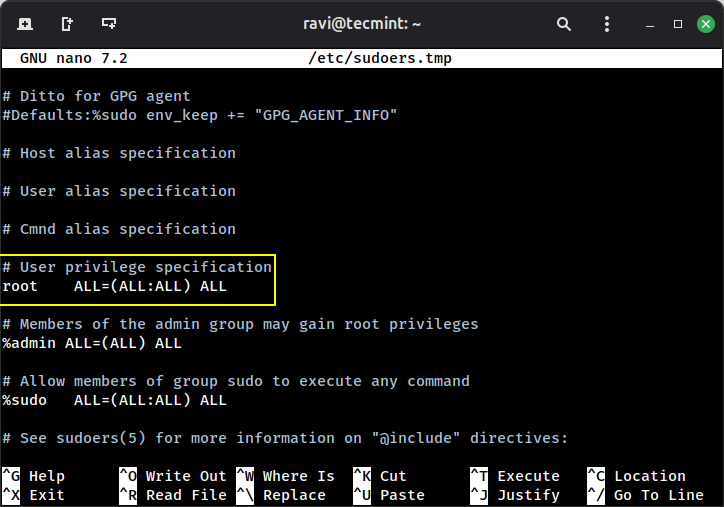
Linux is generally more secure than many other operating systems. A key part of this security…
As enterprises adopt AI agents and embed them into SaaS workflows, visibility and governance become essential….

Do you feel like your Ubuntu desktop turns messy the moment you open more than a…
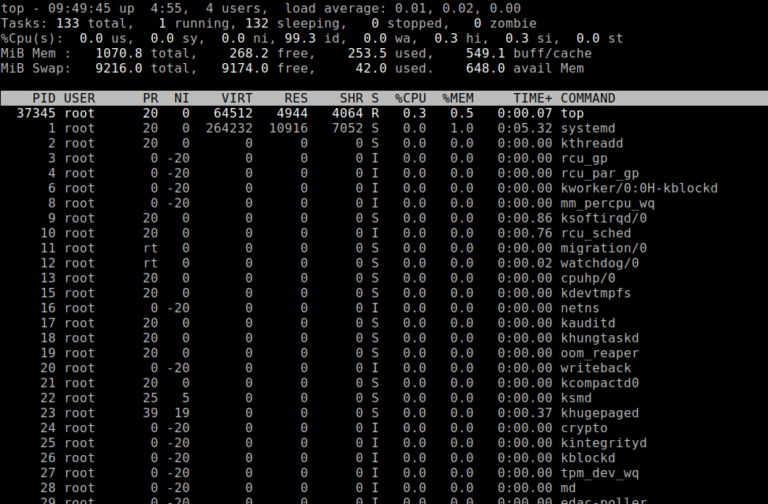
Being a System or Network administrator tasked with monitoring and debugging Linux system performance problems on…