Install Rocky Linux 10 Remotely via RDP on a Headless Server
Rocky Linux 10 replaced VNC with RDP (Remote Desktop Protocol) for remote graphical installations, so if…

Rocky Linux 10 replaced VNC with RDP (Remote Desktop Protocol) for remote graphical installations, so if…
Closing the gap between exposure and remediation requires AI that can reason across the entire environment,…
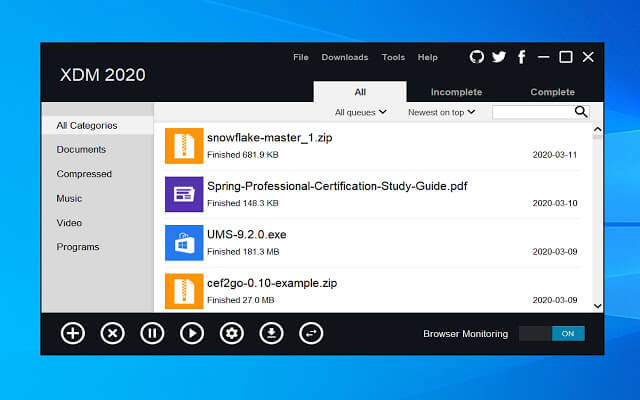
One thing many people miss after switching from Windows to Linux is a good download manager….
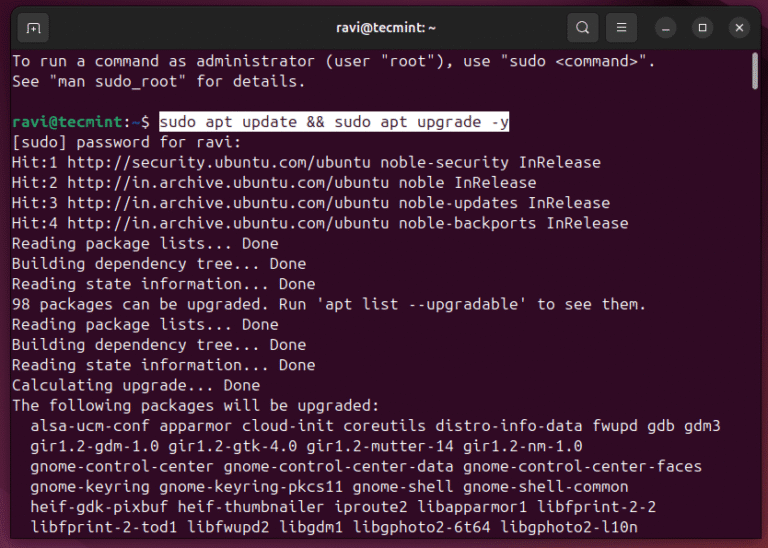
Ubuntu 26.04 LTS “Resolute Raccoon” shipped on April 23, 2026, and if you’re still on 24.04,…
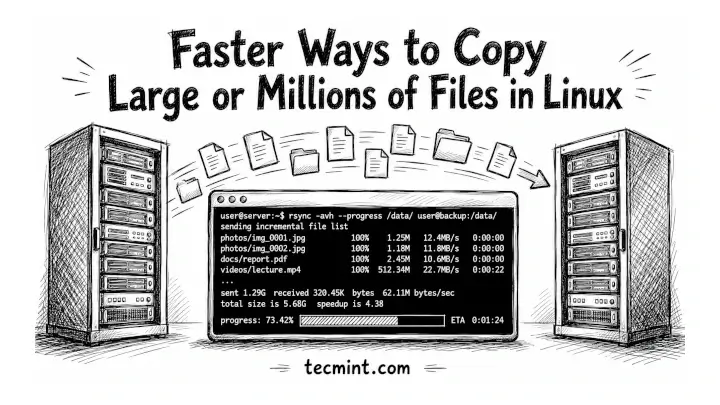
You’ve been copying files with cp for years, and if you’re moving a 50GB backup or…
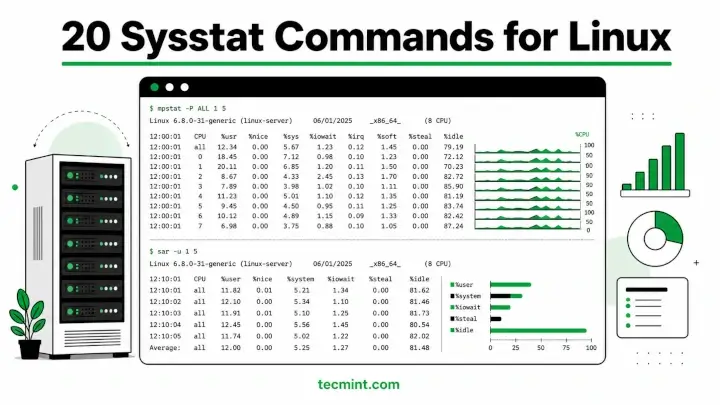
Sysstat is a collection of performance monitoring utilities for Linux that includes mpstat, pidstat, iostat, and…

Durable revenue comes from merchants who stay, grow, and succeed over time. Not just those who…
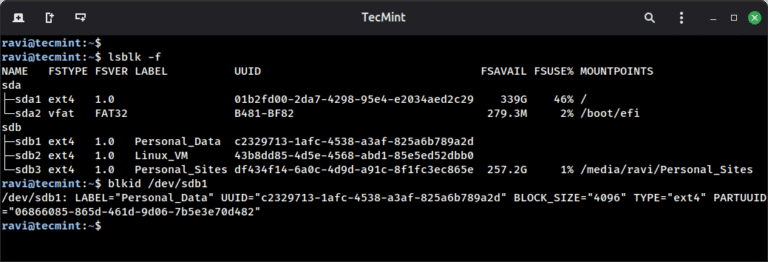
Linux filesystems are responsible for organizing how data is stored and retrieved. Over time – due…
Cloud environments are where AI is built, trained, and deployed at scale. Organizations are deploying AI…
This milestone underscores our commitment to protecting the federal government’s most critical systems from modern threats. …
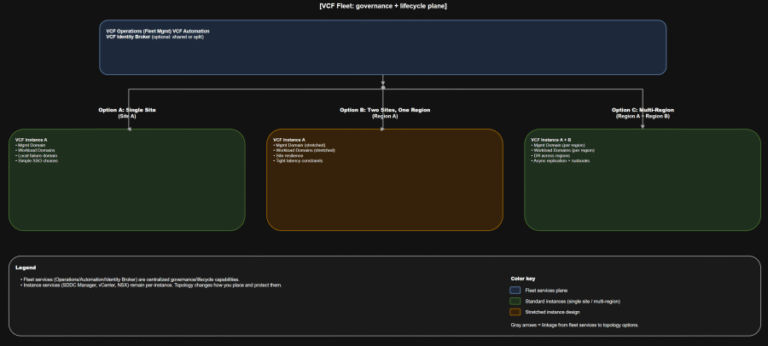
TL;DR Scope: VMware Cloud Foundation 9.0.0.0 GA (primary platform build 24703748) and the associated 9.0 GA…
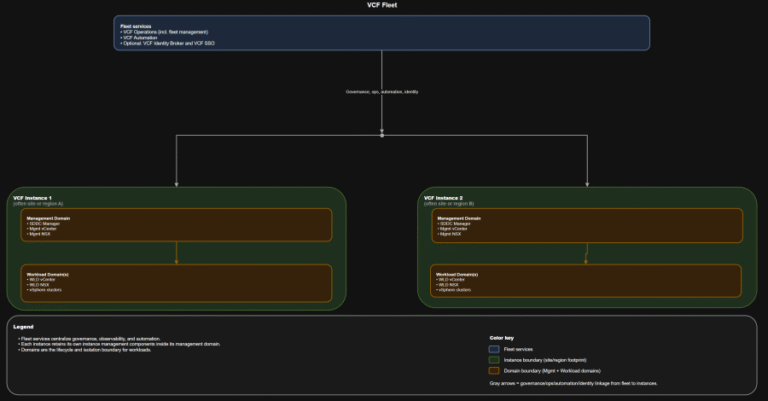
TL;DR Identity is not a “later” decision. It is a boundary decision. The hierarchy you should…
CrowdStrike Falcon Identity Protection — A Great Tool to Gain Visibility We remain committed to innovating…
GOLDEN CHOLLIMA Shared infrastructure elements and tool cross-pollination indicate these units maintain close coordination. All three…
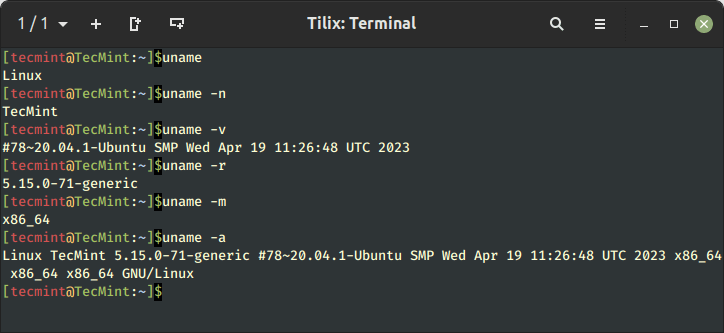
Learn 11 essential Linux commands to check hardware info including CPU, RAM, disk, USB, and PCI…