CrowdStrike Achieves NCSC CIR Assurance for Incident Response
This milestone comes as the UK places increased emphasis on cyber resilience, operational assurance, and incident…
This milestone comes as the UK places increased emphasis on cyber resilience, operational assurance, and incident…
TL;DR Scope: VMware Cloud Foundation 9.0.0.0 GA (primary platform build 24703748) and the associated 9.0 GA…
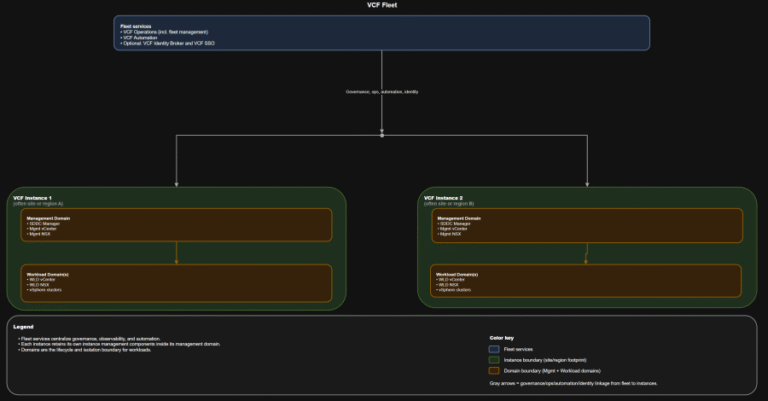
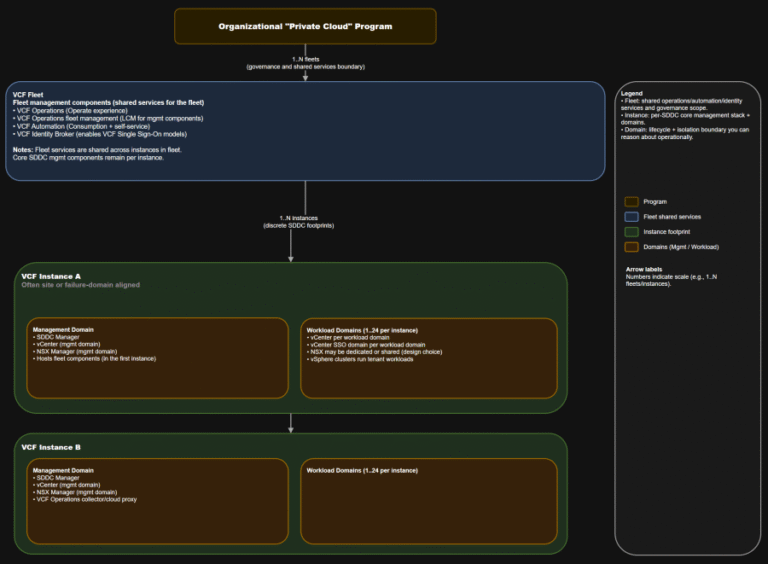
TL;DR Identity is not a “later” decision. It is a boundary decision. The hierarchy you should…
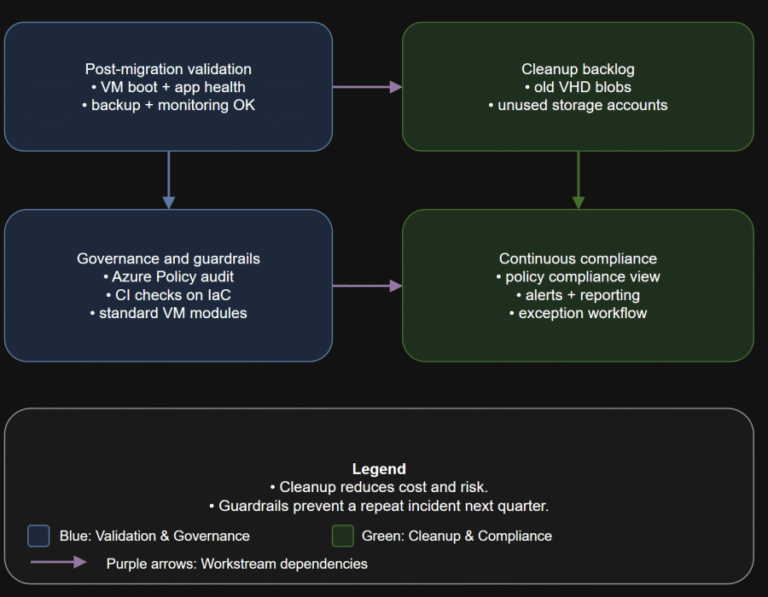
TL;DR Converting disks is not the finish line. Your real goal is a new steady state:…
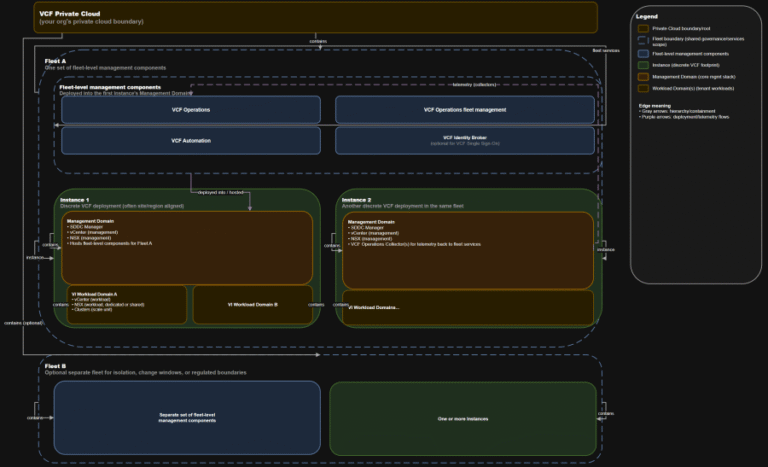
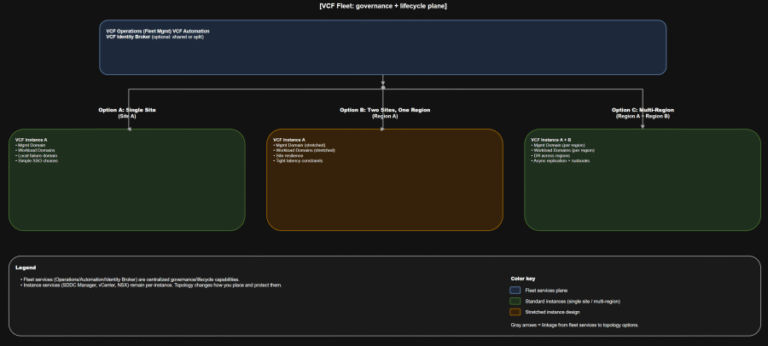
TL;DR A) One fleet, one instance, stretched where justified In VCF 9.0, identity is not a…
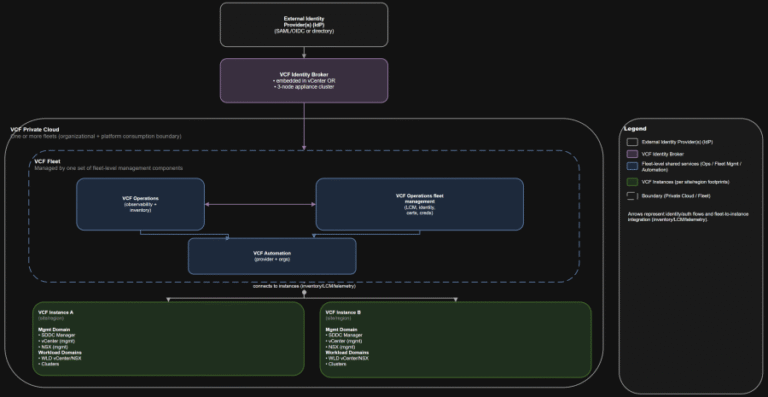
TL;DR Practical implication: if fleet services are impaired, governance and workflows degrade, but the instance-level control…
In this article, you will learn how to list, configure, enable, disable, and troubleshoot network interfaces…
TL;DR This is the “where do we do the thing” map you want in every runbook….
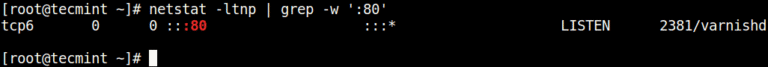
In this article, you will learn how to find which process or service is listening on…
CrowdStrike Falcon Identity Protection — A Great Tool to Gain Visibility We remain committed to innovating…

In this guide, you’ll learn five practical commands for discovering quick information about any binary command:…
The Human-AI Feedback Loop in Action Expert-Annotated Data Enables Analyst Grade AI 2 Time savings represents…
Actively Exploited Zero-Day Vulnerability in Windows Remote Desktop The vulnerability allows local attackers with no privileges…
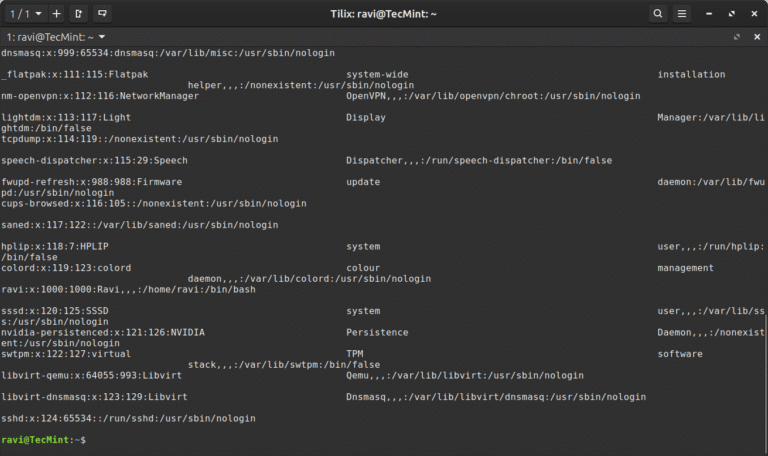
In this article, you will learn how to use the Linux column command to format text…
Indirect prompt injection significantly amplifies this risk by allowing adversaries to influence OpenClaw’s behavior through data…