How CrowdStrike is Accelerating Exposure Evaluation as Adversaries Gain Speed
When a high-profile vulnerability is disclosed, teams need to move quickly and with confidence in the…
When a high-profile vulnerability is disclosed, teams need to move quickly and with confidence in the…
Falcon Onum introduces a new paradigm for data management by allowing teams to intelligently prioritize and…
An initial spike on Linux platforms linked to runners was observed on March 19, 2026. The…
This milestone underscores our commitment to protecting the federal government’s most critical systems from modern threats. …
There are several ways to find out which version of Linux you’re running on your system,…
SOCKS5 At launch, Enhanced Network Visibility will support parsing of plaintext HTTP requests and responses and…
Critical Vulnerability in Microsoft Devices Pricing Program CVE-2026-23651 and CVE-2026-26124 are Critical elevation of privilege vulnerabilities…
The log collector itself focuses exclusively on ingesting third-party and external log data, complementing native CrowdStrike…
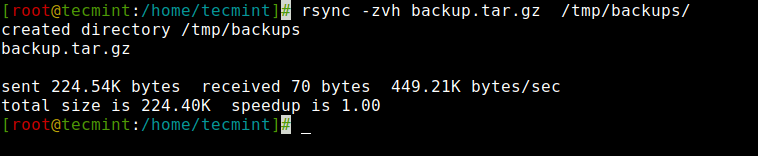
In this article, you will learn how to copy, sync, backup, and transfer files locally and…
To defend themselves, security leaders need clarity on which adversaries to watch, the details of their…
TL;DR Scope: VMware Cloud Foundation 9.0.0.0 GA (primary platform build 24703748) and the associated 9.0 GA…
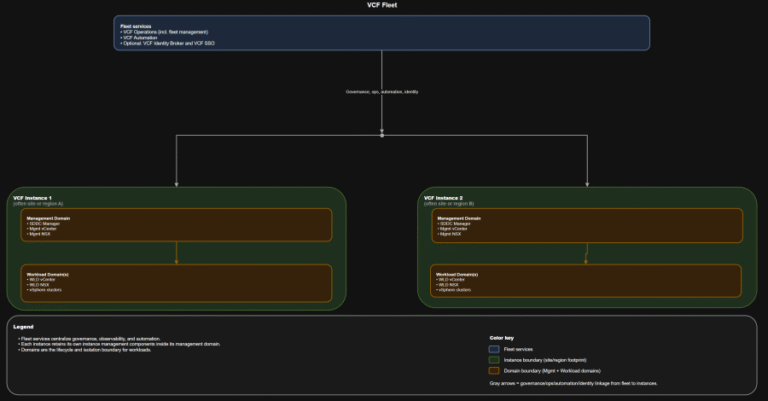
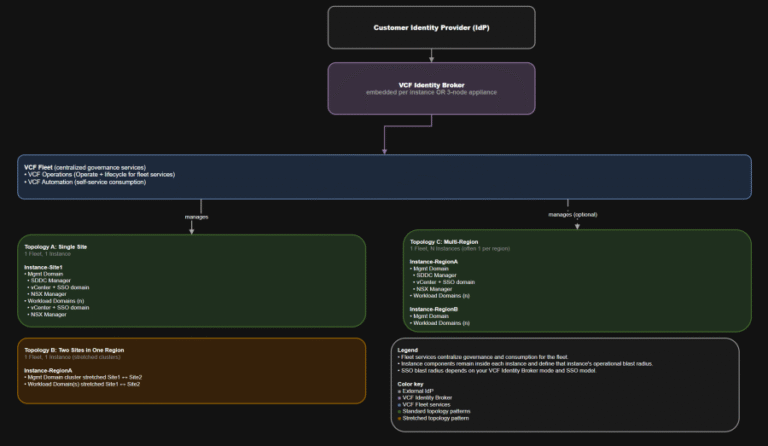
TL;DR Identity is not a “later” decision. It is a boundary decision. The hierarchy you should…
TL;DR This post targets VCF 9.0 GA only: VCF 9.0 (17 JUN 2025) build 24755599, with…
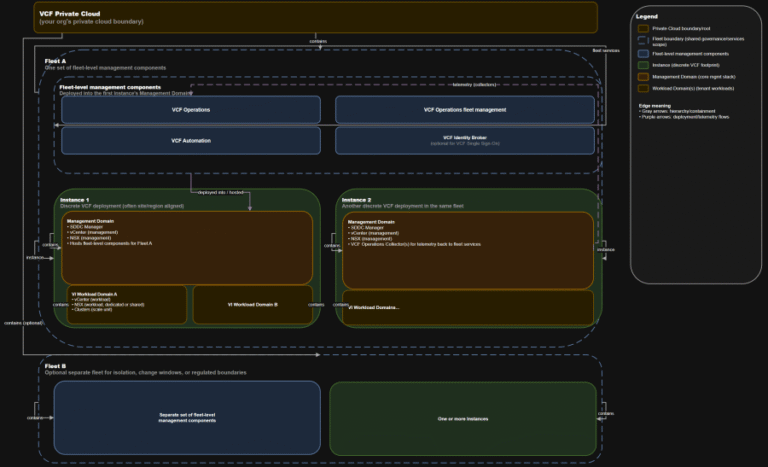
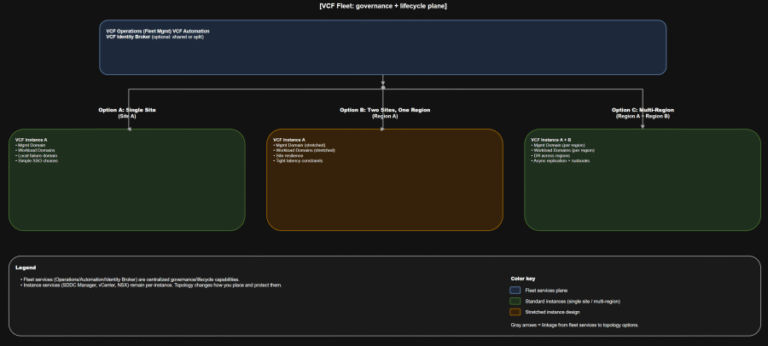
TL;DR A) One fleet, one instance, stretched where justified In VCF 9.0, identity is not a…
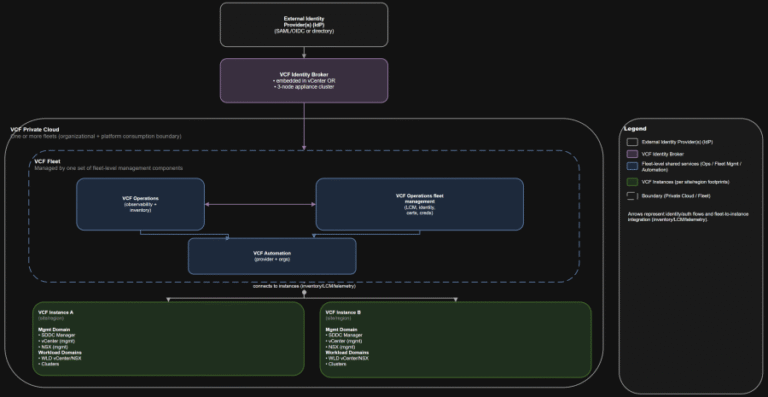
TL;DR Practical implication: if fleet services are impaired, governance and workflows degrade, but the instance-level control…