Falcon for IT Supports Windows Secure Boot Certificate Lifecycle Management
A recommended execution cadence is weekly or monthly to maintain posture awareness and support audit requirements.While…
A recommended execution cadence is weekly or monthly to maintain posture awareness and support audit requirements.While…
Before a client can authenticate to a service, it must resolve the service hostname to an…
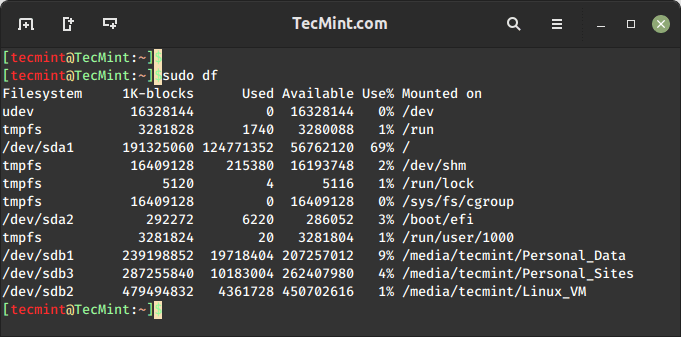
On the internet, you will find plenty of tools for checking disk space usage in Linux….

By correlating runtime application behavior with cloud infrastructure findings, Application Explorer gives organizations a precise view…
Cloud environments are where AI is built, trained, and deployed at scale. Organizations are deploying AI…
Falcon AIDR and its corresponding API enable teams to create named detection policies tailored to their…
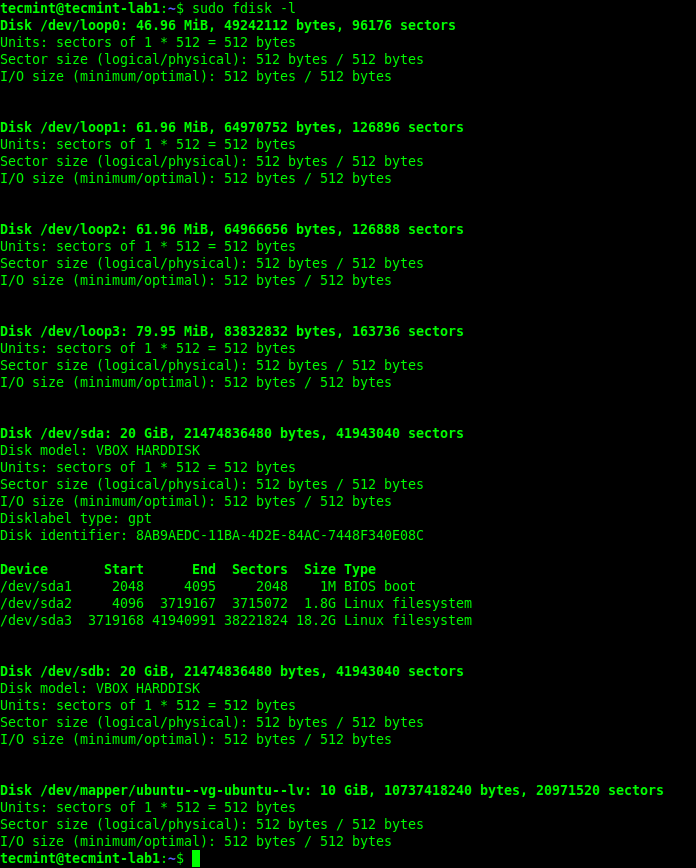
Whether you’re troubleshooting boot issues, preparing to format a drive, or setting up a new disk,…
There are several ways to find out which version of Linux you’re running on your system,…
SOCKS5 At launch, Enhanced Network Visibility will support parsing of plaintext HTTP requests and responses and…
To defend themselves, security leaders need clarity on which adversaries to watch, the details of their…
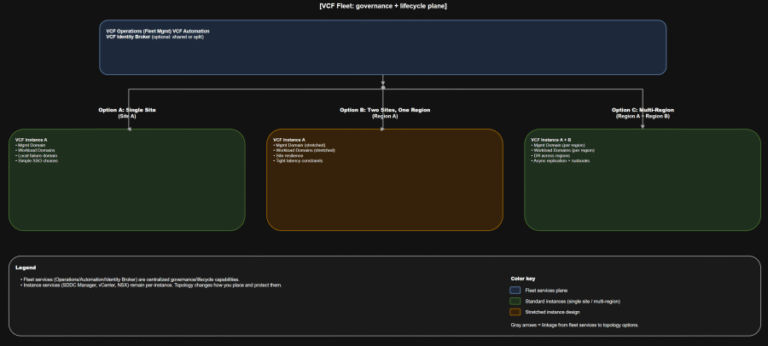
TL;DR Scope: VMware Cloud Foundation 9.0.0.0 GA (primary platform build 24703748) and the associated 9.0 GA…
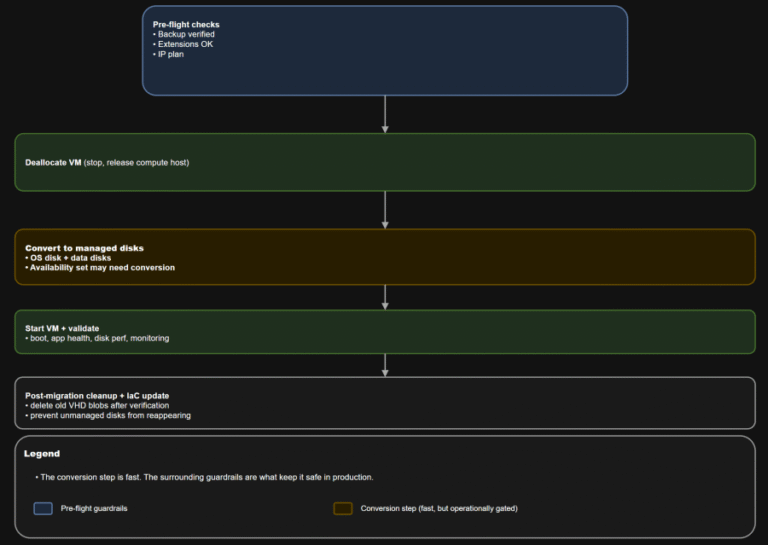
TL;DR Converting a VM to managed disks is usually operationally straightforward: deallocate, convert, start, validate. The…
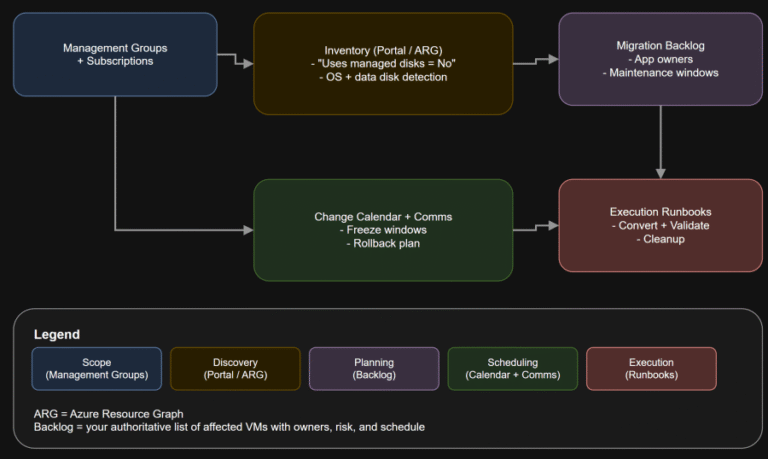
TL;DR If any Azure IaaS VM in your estate still uses unmanaged disks, it is on…
Insider threats pose a growing risk to organizations. Whether insiders take malicious actions, exhibit negligent behavior,…
In this article, you will learn how to list, configure, enable, disable, and troubleshoot network interfaces…