CrowdStrike Leads in GigaOm Radar for Identity Threat Detection and Response
Adversary-driven approach: GigaOm praised CrowdStrike’s adversary-centric approach to identity security: “Utilizing threat intelligence, it enriches alerts…
Adversary-driven approach: GigaOm praised CrowdStrike’s adversary-centric approach to identity security: “Utilizing threat intelligence, it enriches alerts…
CrowdStrike is integrating Falcon Identity Protection and CrowdStrike Falcon® Next-Gen SIEM to empower security teams with…
Since implementing Falcon Identity Protection, Cushman & Wakefield has strengthened its identity security while reducing operational…
Adversaries no longer operate in silos, and neither should defenders. Modern cross-domain attacks may start with…
The CrowdStrike 2025 Global Threat Report illustrates the urgent need for strong identity protection as adversaries…
Securing the Nation’s Most Critical Systems: CrowdStrike Achieves FedRAMP High Authorization In an era where adversaries…
Actively Exploited Zero-Day Vulnerability in Microsoft Management Console Microsoft Management Console received a patch for CVE-2025-26633,…
“By moving to Falcon Complete, we saw a drop in our operational expense on cybersecurity by…
They detect techniques across the entire cyber kill chain with out-of-the-box correlation rules mapped to both…
1. Initial Entry and Exploitation After gaining initial access, the adversary moved laterally through the network…
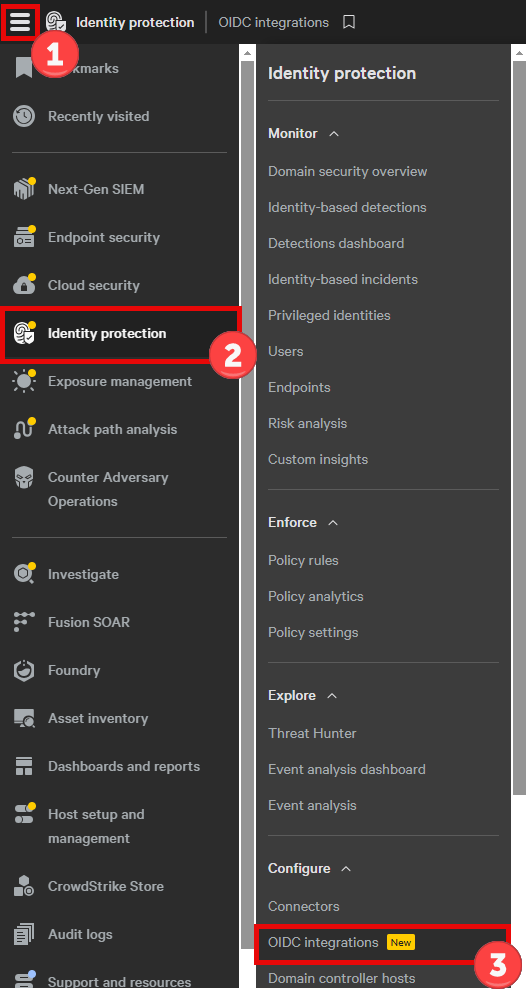
STEP 2: On the OIDC integrations page, click Create OIDC client. These cross-domain attacks exploit the…
Adversaries may tamper with organizations’ infrastructure to facilitate data exfiltration. Some examples include:It is essential to…
Early in the cyberattack kill chain, reconnaissance enables attackers to assemble critical network information to plan…
Since its customer story was first published in 2023, the University of Sunderland has expanded its…
Falcon Identity Protection empowers organizations to stay ahead of identity-based threats by combining advanced prevention, automatic…