Anthropic Claude Mythos Preview: The More Capable AI Becomes, the More Security It Needs
A frontier model is the engine. Data is the fuel. The platform is how you operationalize…
A frontier model is the engine. Data is the fuel. The platform is how you operationalize…
A recommended execution cadence is weekly or monthly to maintain posture awareness and support audit requirements.While…
Charlotte Agentic SOAR provides the critical components needed to operationalize an agentic defense: It brings together:…

By correlating runtime application behavior with cloud infrastructure findings, Application Explorer gives organizations a precise view…
Cloud environments are where AI is built, trained, and deployed at scale. Organizations are deploying AI…
On March 4, 2026, Europol announced the technical disruption of Tycoon2FA, a subscription-based phishing-as-a-service (PhaaS) platform…
An initial spike on Linux platforms linked to runners was observed on March 19, 2026. The…
Falcon AIDR and its corresponding API enable teams to create named detection policies tailored to their…

Stopping compromised access at login is essential, but identity risk doesn’t end there. CrowdStrike acquired SGNL…
To defend themselves, security leaders need clarity on which adversaries to watch, the details of their…
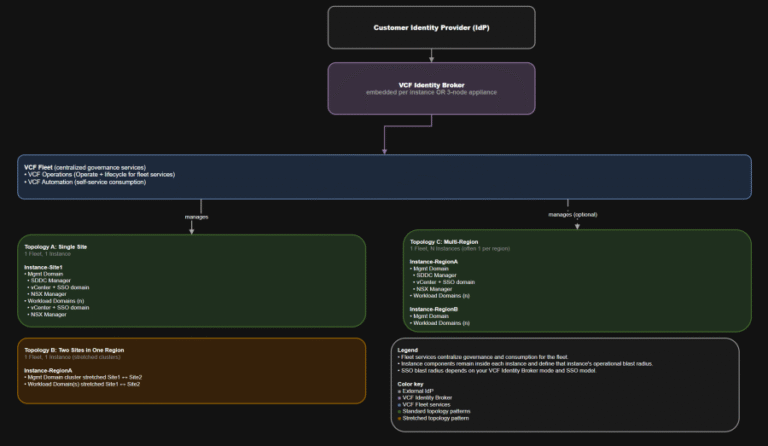
TL;DR This post targets VCF 9.0 GA only: VCF 9.0 (17 JUN 2025) build 24755599, with…
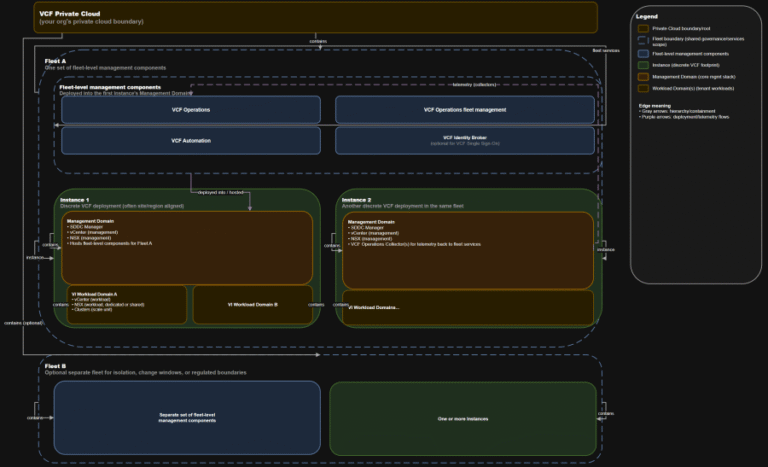
TL;DR A) One fleet, one instance, stretched where justified In VCF 9.0, identity is not a…
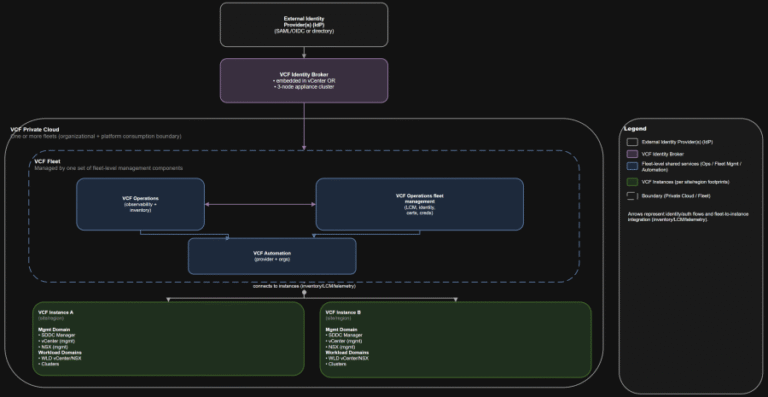
TL;DR Practical implication: if fleet services are impaired, governance and workflows degrade, but the instance-level control…
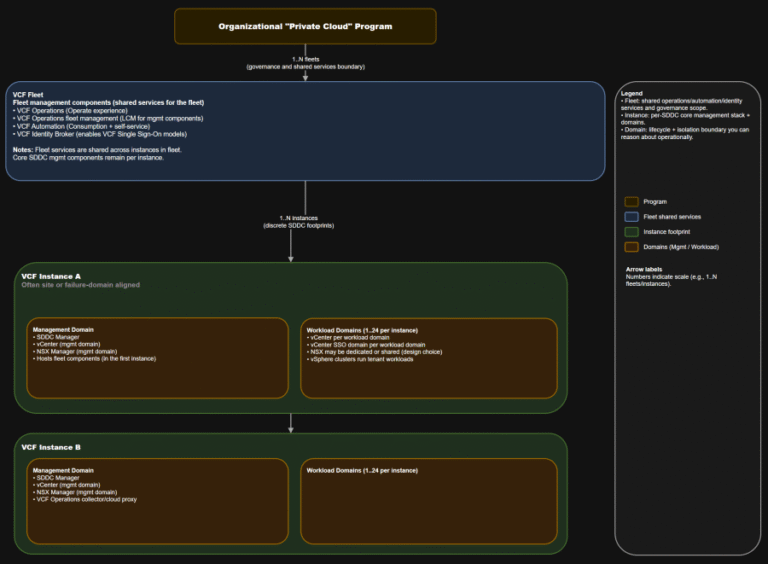
TL;DR This is the “where do we do the thing” map you want in every runbook….
CrowdStrike Falcon Identity Protection — A Great Tool to Gain Visibility We remain committed to innovating…