Falcon Insight for ChromeOS Adds Automated Response Actions and GovCloud Support
Adversaries move fast, and so must defenders. CrowdStrike is raising the bar for ChromeOS security with…
Adversaries move fast, and so must defenders. CrowdStrike is raising the bar for ChromeOS security with…
Unsupported operating systems have historically become adversary targets. The longer a system remains unsupported, the more…

Unauthorized use of RMM tools has become especially dangerous: Throughout 2024, eCrime actors frequently used RMM…
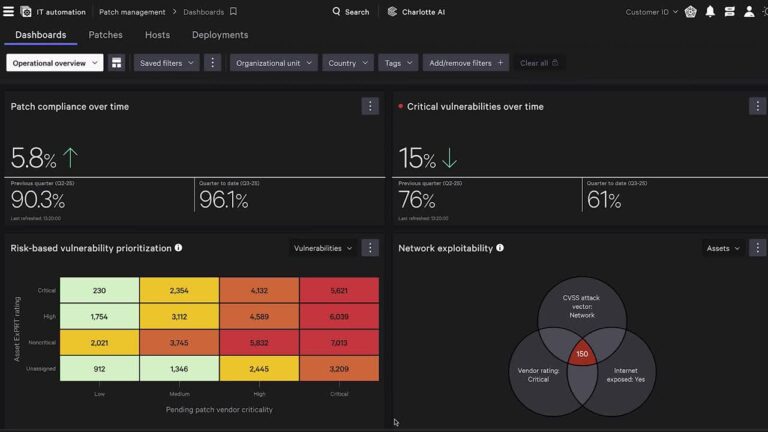
Traditional vulnerability management is broken. Security teams rely on one set of tools to find vulnerabilities;…
The Hub doesn’t just display what’s happening — it tells teams what to do about it…
A Visionary Leader in MDR See what other industry analysts are saying about CrowdStrike on our…

Where these traditional tools stay silent, CrowdStrike Signal takes action. It identifies activity that deviates from…
Here, we outline this attack and explain how the CrowdStrike Falcon® platform detects and successfully prevents…
Stopping Modern Attacks with AI and Expertise The Frost Radar™ serves as essential research for organizations…
Envisioning the Future of Endpoint Protection Gartner has positioned CrowdStrike furthest right in Completeness of Vision…
These tactics are part of a broader shift. As adversaries increasingly rely on unmanaged infrastructure to…

The real-world assessments conducted by respected testing authorities such as AV-Comparatives help ensure the Falcon platform…
However, the memory patching approach is quite noisy from an attacker perspective because it can raise…
“CrowdStrike Falcon is excellent at detecting anomalous activity where traditional antivirus is otherwise incapable of detecting…
With Device Trust from Android Enterprise integrating with Falcon for Mobile, organizations can now: Enforce consistent…