Fal.Con 2024 – Innovations in Cloud Security | CrowdStrike
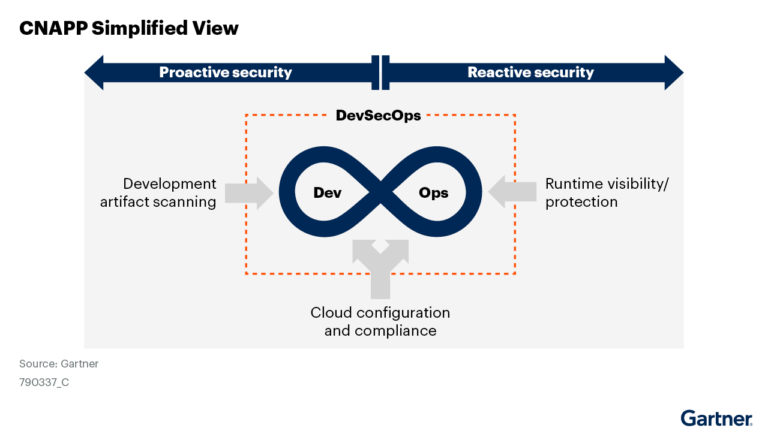
ASPM, recently integrated into Falcon Cloud Security, extends this capability by providing full visibility into your…
ASPM, recently integrated into Falcon Cloud Security, extends this capability by providing full visibility into your…
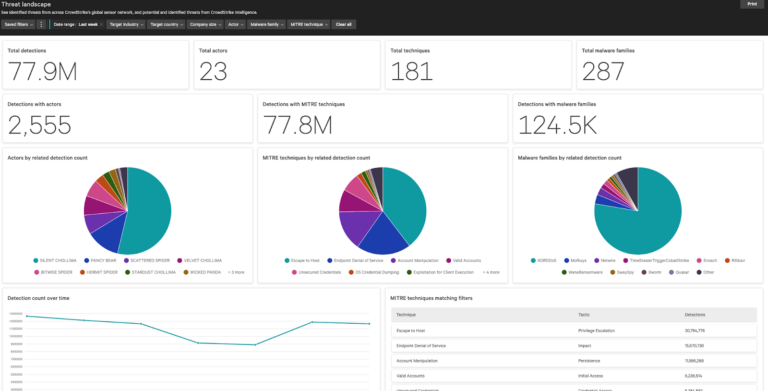
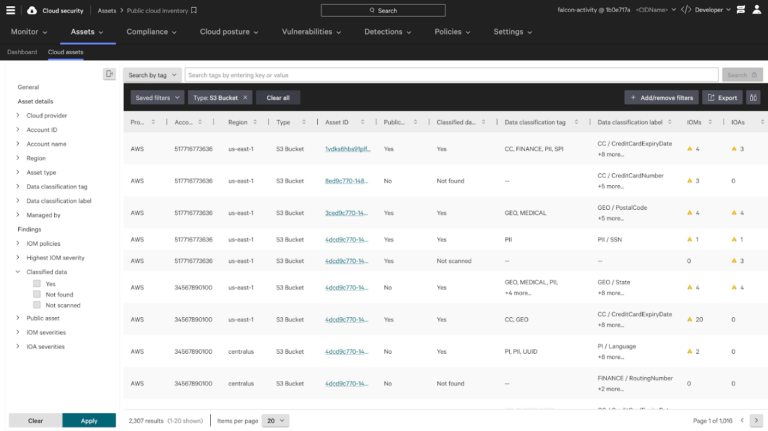
Figure 2. Monitor the movement of data through web applications to protect your sensitive data CrowdStrike…

The Frost & Sullivan report emphasizes the importance of MDR integration. “The deep combination of technology…

Best of all, you can customize your own agenda to match your needs and interests so…
To reduce response times, organizations need to adopt CDR capabilities that go “… beyond basic workload…